Ransomware is evolving faster than many defenses can keep up. In 2026, attackers are no longer just encrypting files they are systematically dismantling security tools, stealing sensitive data, and even preparing for a post-quantum future.
Despite a slight global decline in ransomware incidents, the threat remains deeply entrenched and increasingly sophisticated.
In the manufacturing sector alone, ransomware caused an estimated $18 billion in losses during the first three quarters of 2025, based on joint findings from Kaspersky and VDC Research.
This shift suggests fewer but more damaging attacks, with threat actors focusing on high-value targets and scalable operations.
According to Kaspersky Security Network, fewer organizations reported ransomware incidents in 2025 compared to 2024. However, this decline does not signal reduced risk. Instead, attackers are becoming more efficient and targeted.
A defining trend in 2026 is the widespread use of “EDR killers” tools designed to turn off endpoint detection and response systems before deploying ransomware.
Attackers increasingly rely on Bring Your Own Vulnerable Driver (BYOVD) techniques, abusing legitimate signed drivers to terminate security processes.
This approach allows adversaries to blend into normal system activity while quietly dismantling defenses.
Evasion is now a planned phase of the attack lifecycle, not an afterthought. As a result, organizations face the dual challenge of detecting intrusions while ensuring their own security tools are not being neutralized.
Ransomware groups are also adopting advanced cryptography. New families now use post-quantum encryption methods designed to resist both classical and future quantum-based decryption attempts.
One notable example is the PE32 ransomware family, which uses the ML-KEM standard and Kyber1024 algorithm to secure encryption keys.
This mechanism offers security comparable to AES-256 and aligns with NIST’s post-quantum cryptography standards. Such innovations make data recovery without paying ransom increasingly unlikely.
Ransomware Gangs Use BYOVD and EDR
As ransom payments dropped to 28% in 2025, attackers are shifting tactics. Many campaigns now skip encryption entirely and focus on data theft and extortion. Groups like ShinyHunters leverage stolen data and threaten public leaks to pressure victims.
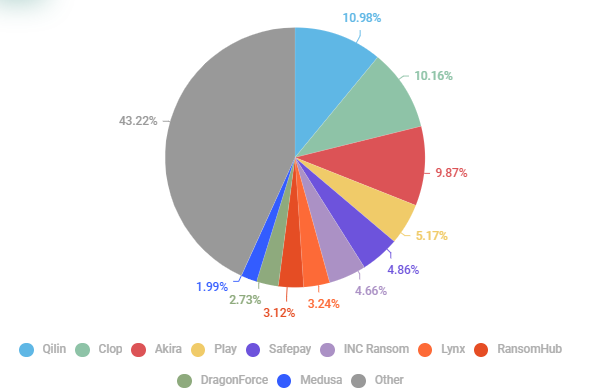
RansomHub’s sudden dormancy in 2025 marked a shift, and Qilin became the dominant player from Q2 onward.
This model reduces detection time and avoids reliance on encryption routines. It also changes the risk landscape backups no longer mitigate the primary threat, as data exposure leads to regulatory penalties and reputational damage.
The ransomware ecosystem is becoming more industrialized, with initial access brokers (IABs) playing a critical role. These actors sell pre-compromised access to corporate networks, often obtained through infostealers and phishing.
Remote access services such as RDP, VPN, and increasingly RDWeb are the most traded entry points. As organizations improve defenses around exposed RDP services, attackers are shifting toward RDWeb portals, which are often less secure.
Underground forums and Telegram channels continue to facilitate ransomware operations, offering stolen data, access credentials, and even ransomware-as-a-service tools. However, law enforcement is pushing back.

In 2026, authorities seized major platforms like RAMP and LeakBase, following earlier takedowns of Nulled, Cracked, and XSS. While these actions disrupt operations, new platforms quickly emerge to fill the gap.
Qilin emerged as the most active ransomware group in 2025, followed by Clop and Akira. Meanwhile, new actors like The Gentlemen are gaining attention for their structured, professional operations and focus on data-centric extortion.
Smaller groups such as Devman, NightSpire, and Vect highlight the low barrier to entry, reinforcing how dynamic and crowded the ransomware ecosystem has become.
As ransomware continues to evolve, organizations must adapt to a threat that increasingly targets not just systems, but the very security controls designed to protect them.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.