The MacroPack framework, initially designed for Red Team exercises, is being abused by threat actors to deploy malicious payloads, including Havoc, Brute Ratel, and PhatomCore.
Security researchers at Cisco Talos have analyzed malicious document submissions on VirusTotal from various countries, including the United States, Russia, China, and Pakistan.
These documents varied in their lures, sophistication, and infection vectors, indicating that MacroPack is being abused by multiple threat actors, signifying a potential trend.
MacroPack payload generation
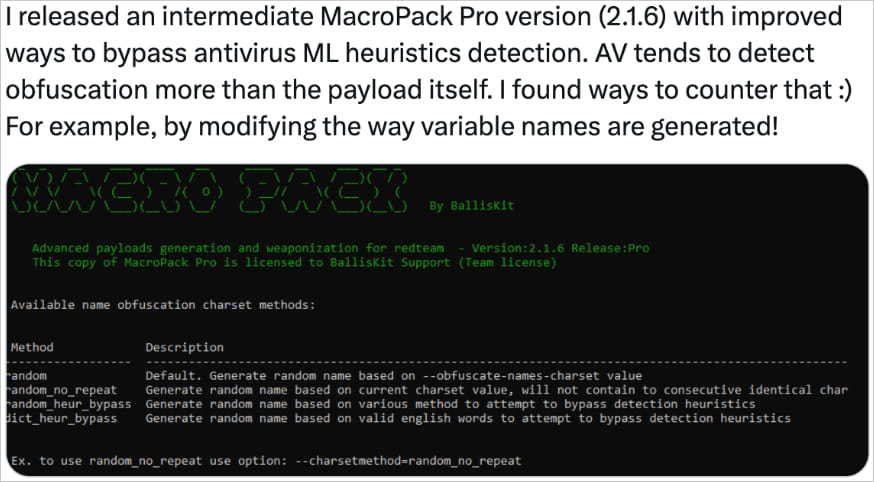
MacroPack is a proprietary tool focused on Red Team exercises and adversary simulations, created by French developer Emeric Nasi (dba BallisKit).
It offers advanced features such as anti-malware bypass, anti-reversing techniques, and the ability to build various document payloads with code obfuscation and embed undetectable VB scripts.
Source: Cisco
There’s also a “lite” open-source version called MacroPack Community, which is no longer maintained.
Cisco reports catching many document samples in the wild that carry signs they were created on MacroPack, including Markov-chain-based function and variable renaming, removal of comments and surplus space characters that minimize static analysis detection rates, and strings encoding.
The giveaway characteristic on all those documents indicating they were built on MacroPack Pro is the existence of four non-malicious VBA subroutines that the researchers say they confirmed were added by the professional version of the framework.
Source: Cisco
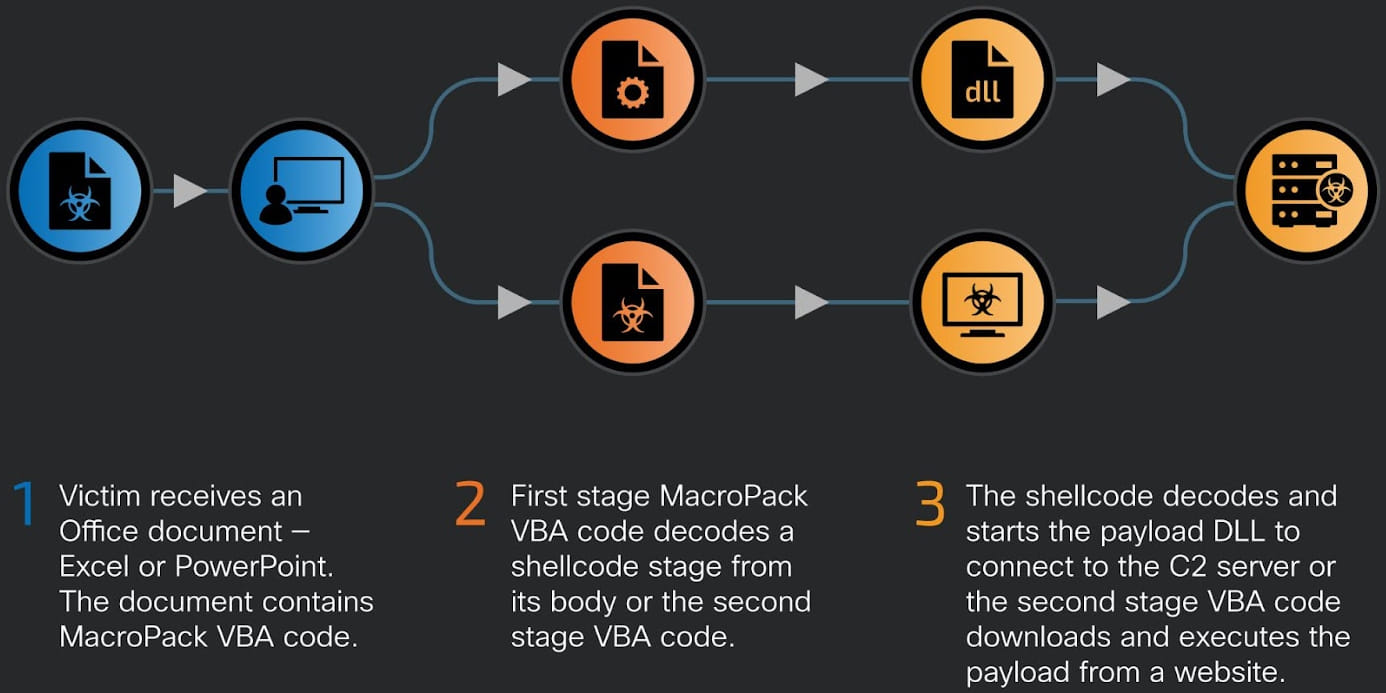
Victims opening these Microsoft Office documents will trigger a first-stage VBA code, which loads a malicious DLL that connects to the attacker’s command and control (C2) server.
Source: Cisco
Documents in the wild
Cisco Talos’ report identifies four significant clusters of malicious activity associated with MacroPack abuse, which are summarized as follows:
- China: Documents from IP addresses in China, Taiwan, and Pakistan (May-July 2024) instructed users to enable macros, delivering Havoc and Brute Ratel payloads. These payloads connected to C2 servers located in Henan, China (AS4837).
- Pakistan: Documents with Pakistani military themes were uploaded from locations in Pakistan. One document, posing as a circular from the Pakistan Air Force, and another as an employment confirmation, deployed Brute Ratel badgers. The documents communicated using DNS over HTTPS and Amazon CloudFront, with one embedding a base64-encoded blob for Adobe Experience Cloud tracking.
- Russia: A blank Excel workbook uploaded from a Russian IP in July 2024 delivered PhantomCore, a Golang-based backdoor used for espionage. The document ran multi-stage VBA code, which attempted to download the backdoor from a remote URL.
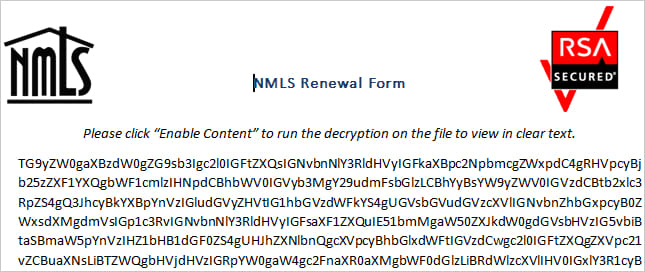
- U.S.: A document uploaded in March 2023 posed as an encrypted NMLS renewal form and used Markov Chain-generated function names to evade detection. The document contained multi-stage VBA code, which checked for sandbox environments before attempting to download an unknown payload via mshta.exe.
Source: Cisco
Brute Ratel is a post-exploitation attack framework hackers have been deploying as an alternative to Cobalt Strike since mid-2022.
Ransomware groups were also spotted using a cracked version of the tool to evade EDRs and AVs during attacks.
The abuse of MacroPack adds another layer of stealth to these attacks and is a worrying development for defenders.
BleepingComputer has contacted Emeric Nasi about the observed abuse, but we have not received a response yet.