Fake shipment tracking scams are rapidly scaling across the world, exploiting the 161 billion annual parcel volume that fuels global e-commerce, according to threat intelligence provider Group-IB.
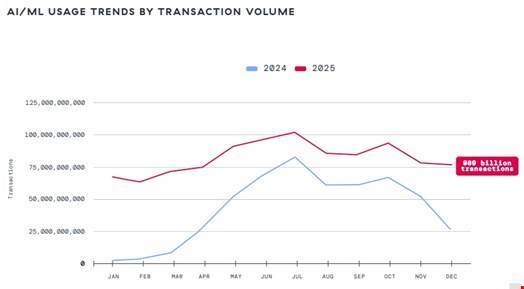
The firm’s Threat Intelligence research team detected a spike in this type of scheme exploiting the popularity of parcel delivery services in 2025.
From almost no such activity observed in 2024, the researchers identified over 100 fake shipment tracking campaigns almost every month throughout the past year, with peaks at 218 and 208 unique campaigns in June and December 2025, respectively.
Some of these campaigns are linked to Darcula, a Chinese-language phishing-as-a-service (PhaaS) platform offering tools that are used in over 100 countries.
Fake Shipment Tracking Scams Explained
The researchers noted that, while many phishing and fake shipment tracking scams rely on cheap, disposable and lightly regulated domains to operate quickly and anonymously (such as [.]xyz,[.]help, [.]shop, [.]click and [.]top) they also abuse trusted extensions like .com through lookalike variations designed to mimic real brands.
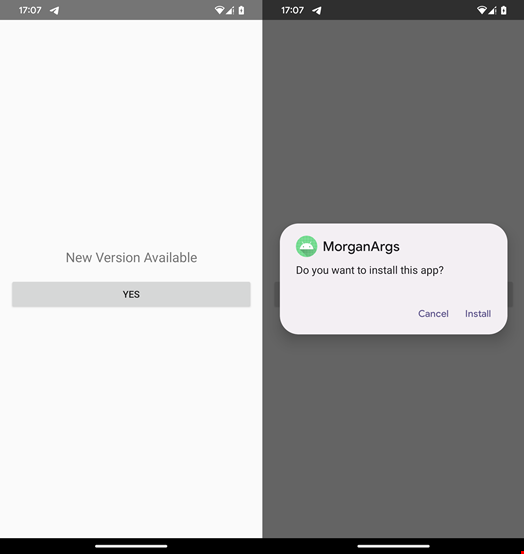
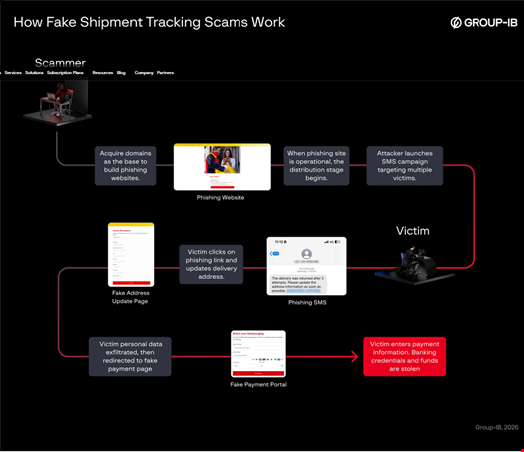
A typical fake shipment tracking scam campaign starts with an attacker setting up a phishing domain and a fake website.
Next, they typically use one of the following methods to infect victims, both sent through an SMS that includes phishing messages claiming failed deliveries:
- Using a legitimate-looking anonymous number (e.g. formatted like local mobile prefixes)
- Using Sender ID spoofing so that the message appears to come from the same official sender the victim’s phone already trusts
The attackers typically use URL masks so that the malicious URLs embedded in the phishing SMS appear legitimate and the malicious page renders properly on mobile devices, increasing the likelihood of victim engagement.
Victims who click to “update address details” or “pay small fees” are then led to pages where they are encouraged to fill in missing personal and/or financial information. This is where victim funds and credentials are stolen.
Observed Infrastructure Links to Dracula Phishkit
While no single threat actor has been definitively linked to these schemes, the Group-IB researchers observed that many of the phishing sites share infrastructure and characteristics commonly associated with Darcula.
Darcula Phishkit is a Chinese-language PhaaS platform that emerged in 2023 and has been used in phishing attacks against organizations (e.g. government, airlines, postal services, financial services) in over 100 countries.
It offers cybercriminals more than 20,000 counterfeit domains to spoof brands and over 200 phishing templates.
Dracula used to commercialize its PhaaS kit through Telegram. However, Group-IB noted that the group removed its public contact information, accounts, domains and platform following its exposure by security vendor Mnemonic.
The group continues to promote its tools through underground channels, confirmed the Group-IB researchers in a March 13 report.
Shipment Tracking Scam Mitigations
The Group-IB report provided a list of recommendations to prevent and mitigate fake shipment tracking scams for both individuals and businesses.
It urged business to:
- Educate the public and customers by regularly publishing alerts about ongoing phishing attempts abusing their brands
- Strengthen official domains using strong authentication and domain security protocols such as DMARC, SKIM and SPF to reduce emails sent under the company name
- Employ a brand protection service that can actively track fake domains, fraudulent pages and suspicious TLD registrations impersonating the brand
- Provide a public verification tool that allows customers to verify tracking numbers, and check and confirm official messages and communication channels to immediately reduce scam success rates
- Ensure strong branding practices in official messages such as consistent short codes, single verified domain, and secure https links
- Work with mobile operators to filter scam SMS patterns and block impersonation attempts before they reach the customer
- Have a clear reporting channel (e.g. fraud@yourcompany.com)