Rhysida ransomware group hacked Abdali Hospital in Jordan

The Rhysida ransomware group claimed to have hacked Abdali Hospital, a multi-specialty hospital located in Jordan.
Abdali Hospital is a multi-specialty hospital located in the modern development of Al-Abdali, Amman, Jordan. Abdali Hospital provides care to patients in numerous specialties. Apart from its general surgery section, it has specialists in orthopedics and rheumatology, gynecology, urology and endocrinology, neurology, nephrology, pulmonology, internal medicine, oncology, infectious disease, and anesthesiology. The hospital also offers aesthetic specialties including plastic surgery and dermatology. Finally, there is a women’s health center with a specialty in breast cancer.
The Rhysida ransomware group claimed to have breached the Abdali Hospital in Jordan and added it to the list of victims on its Tor leak site.
The group published images of stolen documents as proof of the hack. Leaked images include ID cards, contracts and more.
“With just 7 days on the clock, seize the opportunity to bid on exclusive, unique, and impressive data. Open your wallets and be ready to buy exclusive data. We sell only to one hand, no reselling, you will be the only owner!” reads the announcement published on the Tor leak site of the Rhysida ransomware group.

The ransomware group claims to have stolen a substantial trove of ‘sensitive data’ and is auctioning it for 10 BTC. As usual, the Rhysida ransomware operators plan to sell the stolen data to a single buyer. The gang will publicly release the data over the seven days following the announcement.
At the end of November, the ransomware group claimed to have hacked King Edward VII’s Hospital in London.
The group also claimed the hack of the British Library and China Energy Engineering Corporation.
The Rhysida ransomware group has been active since May 2023. According to the gang’s Tor leak site, at least 62 companies are victims of the operation.
The ransomware gang hit organizations in multiple industries, including the education, healthcare, manufacturing, information technology, and government sectors. The victims of the group are “targets of opportunity.”
Last week, FBI and CISA published a joint Cybersecurity Advisory (CSA) to warn of Rhysida ransomware attacks. The advisory is part of the ongoing #StopRansomware effort, disseminating information about tactics, techniques, and procedures (TTPs) and indicators of compromise (IOCs) associated with ransomware groups.
The report includes IOCs and TTPs identified through investigations as recently as September 2023.
“Threat actors leveraging Rhysida ransomware are known to impact “targets of opportunity,” including victims in the education, healthcare, manufacturing, information technology, and government sectors. Open source reporting details similarities between Vice Society (DEV-0832)[1] activity and the actors observed deploying Rhysida ransomware.” reads the joint advisory. “Additionally, open source reporting[2] has confirmed observed instances of Rhysida actors operating in a ransomware-as-a-service (RaaS) capacity, where ransomware tools and infrastructure are leased out in a profit-sharing model. Any ransoms paid are then split between the group and the affiliates.”
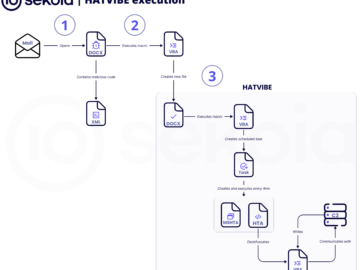
Rhysida actors leverage external-facing remote services (e.g. VPNs, RDPs) to gain initial access to the target network and maintain persistence. The group relied on compromised credentials to authenticate to internal VPN access points. According to the advisory, the threat actors have exploited Zerologon (CVE-2020-1472) in Microsoft’s Netlogon Remote Protocol in phishing attempts.
The group relies on living off-the-land techniques such as native (built into the operating system) network administration tools to perform malicious operations.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, Rhysida ransomware)