The cybercrime group Muddled Libra (aka Scattered Spider, UNC3944). The contents of this rogue VM and activity from the attack provide valuable insight into the operational playbook of this threat actor.
This single VM acted as the attackers’ beachhead, revealing a detailed, step-by-step view of how the group conducts reconnaissance, steals credentials, and moves laterally using mostly legitimate tools.
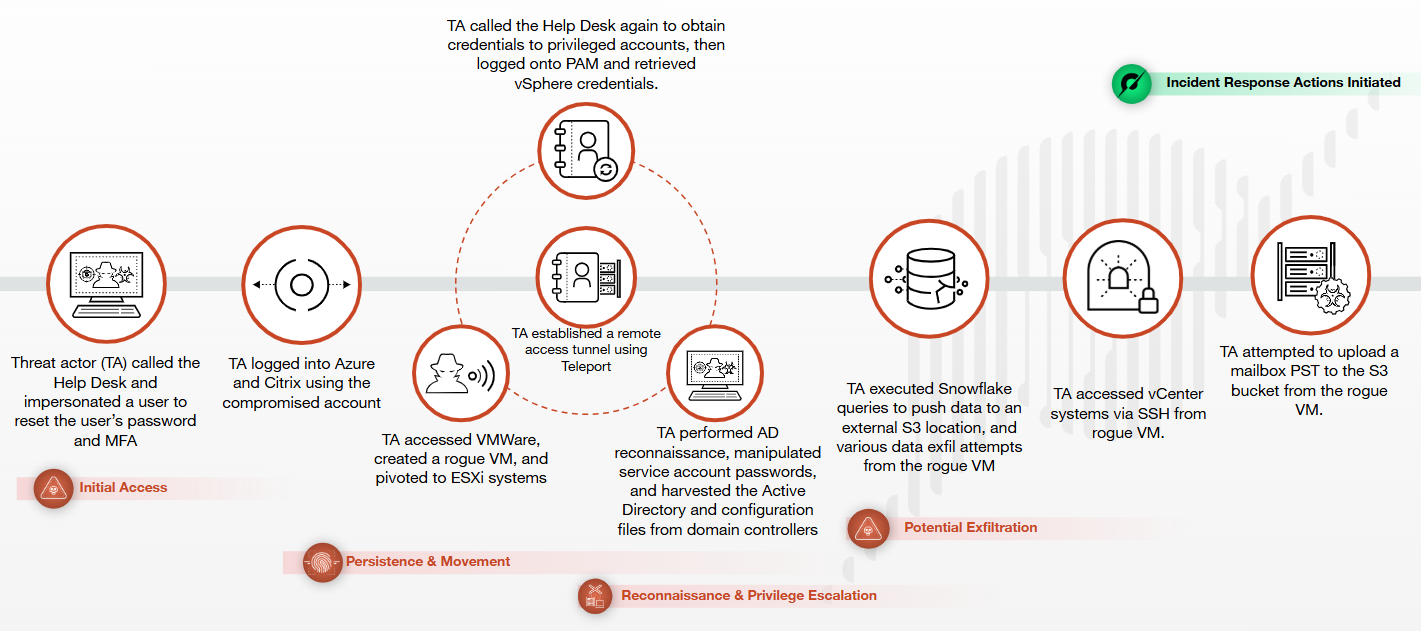
Muddled Libra is a financially motivated threat group known for aggressive social engineering, including smishing and vishing, to get initial access to organizations and their outsourced call centers, BPOs and MSPs.
Rather than relying heavily on malware, they focus on manipulating people, abusing identity workflows and turning an organization’s own infrastructure into an attack platform.
During a September 2025 incident response, analysts uncovered a rogue virtual machine inside a victim’s VMware vSphere environment.
Past investigations show they are comfortable impersonating employees to reset passwords and MFA, then quickly pivoting across internal systems once one account is compromised.
How the Rogue VM Was Used
Roughly two hours after gaining access, the attackers logged into the victim’s vSphere portal and created a VM simply named “New Virtual Machine,” then used the local Administrator account as their main foothold.
From this VM they downloaded stolen certificates from the environment and used them to forge tickets, helping them move through the network while appearing legitimate.
Within minutes they established persistence with an SSH tunnel using the Chisel tool, delivered in a goon.zip archive hosted in an attacker-controlled AWS S3 bucket, and maintained a C2 connection over TCP port 443 for about 15 hours.
The group then turned to Active Directory, powering down two virtualized domain controllers via vSphere so they could mount their virtual disks and copy the NTDS.dit database and SYSTEM registry hive to the rogue VM.
Minutes later, decrypted credential files named result and result.kerb appeared on the Administrator desktop, containing NTLM and Kerberos hashes for users in the environment.
Around the 30‑minute mark, the attackers ran ADRecon and later downloaded ADExplorer64, extracting detailed information on domains, trusts, sites, password policies, DCs, SPNs, users and GPOs, then packaging the output into a victim‑named ZIP file.
Within ADRecon’s results, the attackers focused on ComputerSPNs.csv, looking for critical services such as Veeam, terminal services, Hyper‑V, MSSQL and Exchange that could support deeper access or data theft.
They then researched the victim’s business profile online using NAICS code lookups, likely to understand which data would be most valuable for exfiltration.
Threat actors affiliated with Muddled Libra are highly proficient at exploiting human psychology by impersonating employees to attempt password and multi-factor authentication (MFA) resets.

About 30 minutes after those searches, the group began pulling large datasets from the target’s Snowflake environment into the rogue VM and experimenting with ways to upload the data to external file‑sharing platforms that were not blocked by corporate controls.
Living Off the Land, Troubleshooting
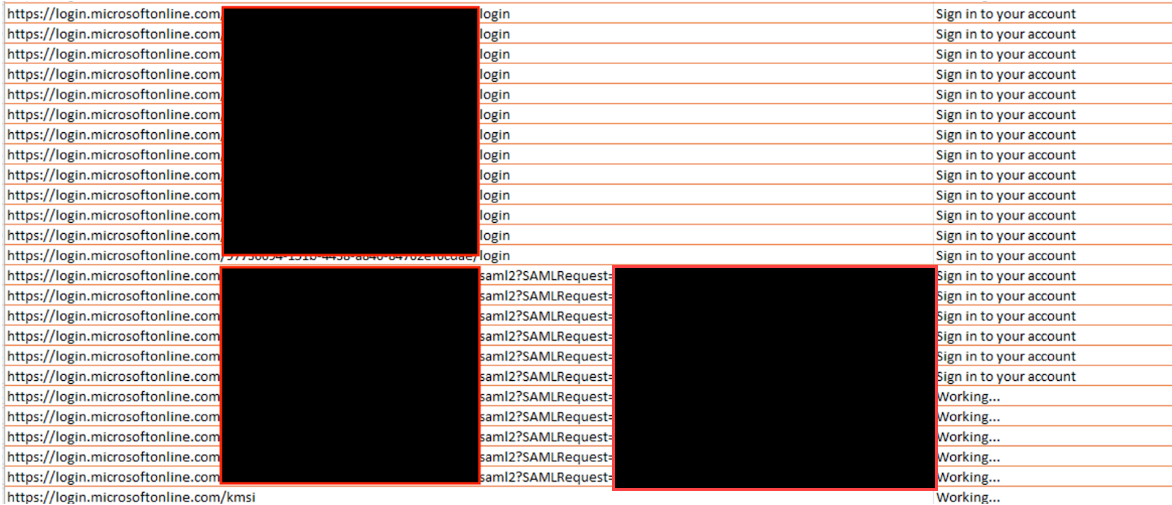
To find an unblocked exfiltration path, the attackers searched Bing for “upload files” and “upload files no registration,” probing sites like upload[.]ee, filetransfer[.]io, filebin[.]io, Dropbox and others from the VM.
Threat actors creating VMs within targeted environments to avoid detection from endpoint tools like endpoint detection and response (EDR) or extended detection and response (XDR).
However, the case also shows why defenders must monitor VMware vSphere, ESXi and Snowflake activity, not just traditional endpoints, and watch for unusual VM creation, DC shutdowns and bulk AD or database access.
They then expanded lateral movement using their SSH tunnel, RDP and PsExec (downloaded directly from Microsoft Sysinternals), while compromising additional accounts.
At one point they attempted to download older Outlook installers from Microsoft, troubleshot slow mailbox downloads with speed tests on fast[.]com, and finally sought to exfiltrate a PST file using the S3 Browser client to upload mail data into an attacker‑controlled S3 bucket.
Even on the rogue VM, Microsoft Defender flagged several tools used by the attackers, including Chisel, ADRecon and GoSecretsDump, illustrating that endpoint protections can still provide value inside virtualized environments.
Organizations can strengthen defenses with identity‑centric controls, strict admin access, and detections for living‑off‑the‑land behavior, while layered solutions such as Palo Alto Networks Advanced WildFire, Cortex Cloud, Cortex XDR and XSIAM help detect malicious tools, anomalous cloud operations and suspicious tunneling patterns linked to groups like Muddled Libra.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.