Political parties are often targeted by hackers since they want to achieve various goals.
This is because hackers may attempt to access confidential data like campaign strategies, opposition research, or even personal communications, which helps them interfere with election processes and get an upper hand in the matter.
Besides this, hackers could try to break into party systems to interfere with operations that would affect the outcome of elections and undermine democracy through any means, such as disinformation campaigns and ransom demands.
Recently, cybersecurity researchers at Mandiant discovered that Russian hackers are actively attacking political parties in recent cyber attacks.
Hackers Attacking Political Parties
A Russian state-sponsored hacking group, APT29, targeted German political parties using a phishing campaign in late February 2024.
This operation was different from their normal targets such as governments and embassies since it used German-language baits imitating a major political party.
The threat actors used a new backdoor variant, among other malware payloads, to facilitate gaining entry into the systems so that they could potentially disrupt activities or even spread fake news ahead of elections.
This clearly indicates how the type of threat actors increasingly change and subsequently influence political organizations in democratic processes.
The Russian hacking group APT29 continues to rely heavily on ROOTSAW malware for initial access and intelligence gathering on foreign political affairs.
It shows that Russia has an interest in trying to control Western politics, especially when it comes to issues such as Ukraine.
This is an adaptable threat that will probably see APT29 targeting political parties throughout the West via multiple attack vectors for initial intrusion like phishing attacks, cloud authentication vulnerabilities, and password spraying.
Given ongoing geopolitical tensions, political organizations must be watchful of these mutating cyber espionage campaigns aimed at shaping narratives and outcomes.
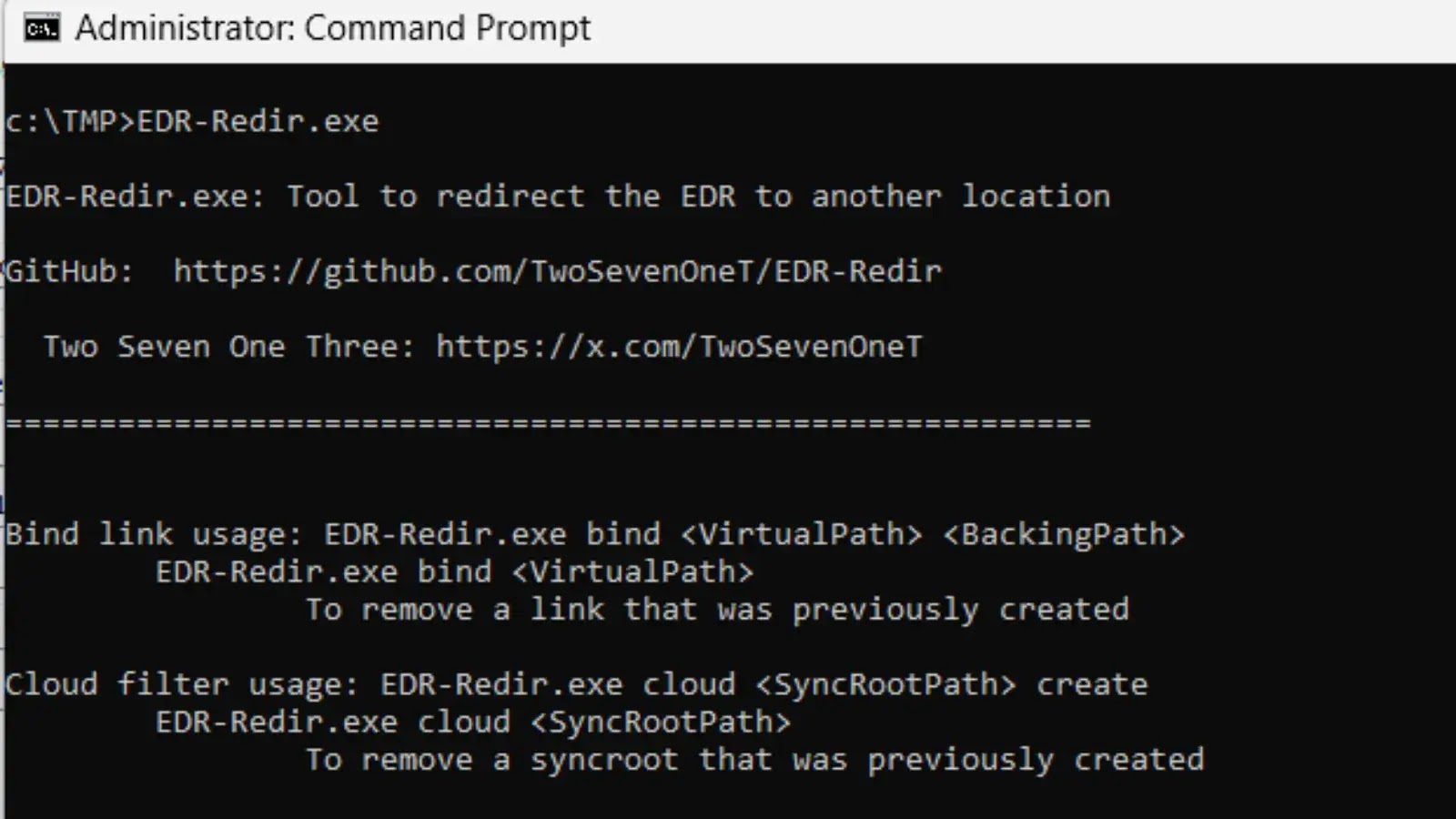
APT29 started spreading phishing emails that contained malware attachments in late February 2024, reads Mandiant report.
These attachments had a link to an infected web page owned by criminals who redirected victims to download the ROOTSAW malware dropper.
ROOTSAW then fetched and executed the WINELOADER backdoor from the same malicious server.
The multi-step infection procedure comprised obfuscated JavaScript, file extraction via such utilities as CertUtil, and inappropriate use of legitimate applications like SQLDumper for delivering malware.
This intricate attack chain clearly demonstrates APT29’s advanced techniques for achieving persistent access through their tailored malware.
WINELOADER is a new, highly customized backdoor used by the Russian state-sponsored hacking group APT29.
While sharing similarities with APT29’s previous BURNTBATTER and MUSKYBEAT malware families, WINELOADER implements unique anti-analysis techniques, avoids public loaders, and uses a novel command-and-control mechanism.
It employs side-loading, process injection, and encrypted payloads to maintain stealth and persistence on compromised systems.
The sophistication of WINELOADER demonstrates APT29’s continued efforts to retool their malware arsenal for stealthy espionage operations against targets of strategic interest.
As geopolitical tensions drive nation-state cyber threats, defenders must stay vigilant against these constantly evolving attack vectors.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.