Researchers discovered a Russian-linked threat actor, UNC5812, utilizing a Telegram persona named “Civil Defense. ”
This persona has been distributing Windows and Android malware disguised as legitimate software designed to aid potential conscripts in Ukraine.
Once installed, these malicious apps silently deploy additional malware, including SUNSPINNER, while engaging in influence operations to undermine Ukrainian mobilization efforts.

UNC5812, a threat actor, launched a malware campaign targeting Ukrainian military recruits in September 2024 by creating a Telegram channel (@civildefense_com_ua) and a website (civildefense.com.ua) to distribute malware.


UNC5812 likely purchased promoted posts in legitimate Ukrainian Telegram channels to lure victims. For instance, on September 18th, a missile alert channel with over 80,000 subscribers promoted “Civil Defense” to its audience.
Protecting Your Networks & Endpoints With UnderDefense MDR – Request Free Demo
Similar promotions continued as late as October 8th, suggesting ongoing efforts to infiltrate new Ukrainian communities by advertising sponsorship opportunities, which UNC5812 probably exploited to gain promotion.


The UNC5812 group deployed a sophisticated phishing campaign to lure victims to a compromised “Civil Defense” website, a gateway to various malware payloads.
Pronsis Loader, a PHP-based downloader that leverages JVM bytecode to deliver SUNSPINNER and PURESTEALER, targets Windows users.
Android users are targeted with a modified CRAXSRAT backdoor, sometimes bundled with SUNSPINNER.
While macOS and iPhone support is advertised, only Windows and Android payloads were observed during analysis.
The Civil Defense website employs social engineering tactics to deceive users into installing the CRAXSRAT malware, which justifies bypassing the App Store by claiming to protect user anonymity and security.
The website directs users to a video instructing them to disable Google Play Protect and manually grant extensive permissions to the malicious APK, thus compromising their device’s security.


It is conducting a multi-pronged influence operation to undermine Ukrainian mobilization efforts by using its Telegram channel to collect videos of alleged unfair mobilization practices, likely to be repurposed to discredit the Ukrainian military.
The group’s website features anti-mobilization content and imagery, some of which is sourced from pro-Russian social media networks, which aims to erode public trust in the Ukrainian military and hinder recruitment efforts.
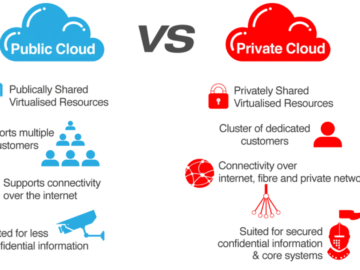
UNC5812 uses a website (civildefense.com.ua) to deliver separate malware chains for Windows and Android. Both chains deploy a decoy app, SUNSPINNER, that displays fake Ukrainian military recruiter locations.


Windows users download CivilDefense.exe (Pronsis Loader), which retrieves SUNSPINNER and a downloader for PURESTEALER, a credential-stealing infostealer.
In contrast, Android users download CivilDefensse.apk (CraxsRAT variant) that may display a Civil Defense splash screen or SUNSPINNER.
Google has identified and mitigated a phishing campaign targeting potential Ukrainian military recruits.
The Russian threat actor UNC5812 conducted the campaign by leveraging a fake “Civil Defense” website to distribute the Android spyware CRAXSRAT.
It has taken steps to protect users by blocking malicious websites, updating Google Play Protect, and enhancing app scanning infrastructure, underscoring the increasing sophistication of Russian cyber threats and the importance of robust security measures to combat them.
Run private, Real-time Malware Analysis in both Windows & Linux VMs. Get a 14-day free trial with ANY.RUN!