Russian hackers are using a new remote access toolkit called “CTRL” to silently hijack Remote Desktop Protocol (RDP) sessions via FRP-based reverse tunnels, enabling stealthy, hands-on access to compromised Windows systems.
The toolkit blends credential theft, keylogging, and RDP abuse into a cohesive post-exploitation framework that currently flies under the radar of public malware scanners and threat feeds.
The domain is hosted on infrastructure in Partner Hosting LTD’s ASN (AS215826), a UK-registered network established in February 2025, with servers located in Frankfurt, Germany.
At the time of analysis, the FRP relay was observed on two IPs – 194.33.61[.]36 and 109.107.168[.]18 – with port 7000 running an FRP server that Censys natively fingerprints as FRPS.
Censys ARC researchers uncovered CTRL while scanning exposed directories and LNK artifacts, tracing a malicious shortcut back to an open payload-hosting folder on hui228[.]ru.
The host at 194.33.61[.]36 also exposes SSH and HTTP, and its OpenSSH 9.6p1 service remains vulnerable to CVE-2024-6387, CVE-2025-26465, and CVE-2025-26466, indicating poor patch hygiene by the operators.
The investigation originated from Censys open directory scanning for LNK files, where an LNK file hosted on a separate server referenced hui228[.]ru for payload downloads.
None of the binaries or infrastructure tied to CTRL appear in VirusTotal or common public threat intelligence sources, suggesting a privately developed toolkit used in limited operations.
Delivery and Execution Chain
CTRL is a custom .NET toolkit distributed via a weaponized Windows shortcut file masquerading as a private key folder.
The LNK’s metadata timestamps are zeroed and it carries the description “Polycue” which may be a possible project codename.
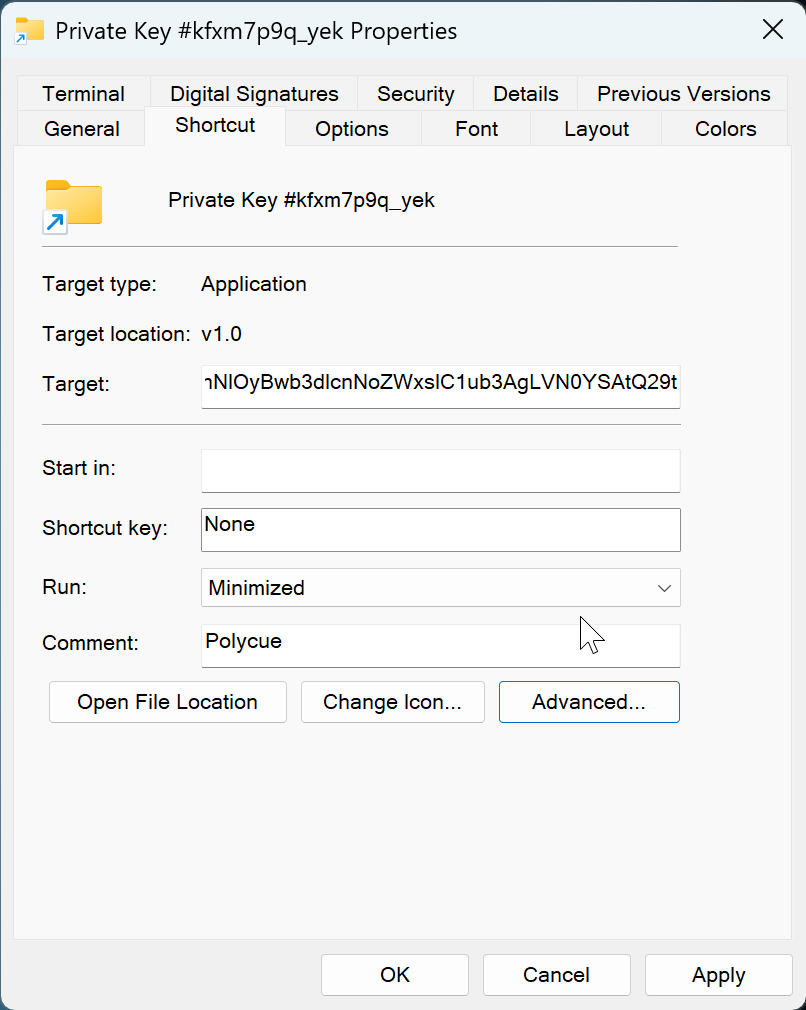
The LNK file, named “Private Key #kfxm7p9q_yek.lnk,” uses a folder icon and zeroed timestamps to evade casual inspection and timeline analysis, while embedding an entire multi-layer PowerShell loader as a large base64 blob.
When executed, the shortcut launches PowerShell in a hidden window, decodes and decompresses an in-memory .NET stager, and stores it as a binary value under plausible Explorer-related registry keys, avoiding any standalone PE file on disk.
The stager then escalates privileges via a fodhelper-based UAC bypass, performs connectivity checks to hui228[.]ru:7000, and pulls down three .NET components that handle encrypted payload loading, FRP tunneling, and RDP enablement.
All core payloads are persisted as registry binaries and reloaded via scheduled tasks using encoded PowerShell, strengthening stealth and resilience across reboots.
Once established, CTRL turns an infected host into a persistent RDP platform controlled solely over FRP tunnels rather than traditional C2 beacons.
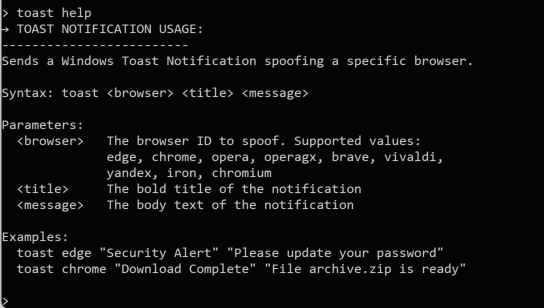
The main ctrl.exe component decrypts and runs a “ctrl Management Platform” agent that exposes a named pipe (ctrlPipe) on the victim, offering commands to read keylogs, launch a sophisticated Windows Hello–style phishing window, shadow or take over active RDP sessions, and trigger data exfiltration workflows.
A companion FRP wrapper decrypts a Go-based FRP v0.65.0 DLL and maps it in memory, establishing reverse tunnels for RDP (3389) and a raw TCP shell on port 5267 back to hui228[.]Are you using an auth token of “ADAD.”
Meanwhile, an RDP wrapper component patches termsrv.dll, installs RDP Wrapper, adds Defender exclusions, and configures Windows for unlimited concurrent RDP sessions so the operator can silently shadow or hijack user desktops without consent prompts.
OPSEC and Detection Guidance
The toolkit’s design shows strong operator OPSEC: no hardcoded C2 addresses exist in the binaries, and the only reference to hui228[.]ru and its auth token is written at runtime into frpc.toml on the victim.
.NET’s Assembly.Load() cannot load native DLLs, the wrapper includes a complete manual PE mapper (DLLFromMemory class) that operates entirely in user-mode memory.
All operator interactions occur inside RDP sessions carried by FRP tunnels, and keylog or credential data is accessed locally via the ctrlPipe, minimizing distinctive network signatures.
On the network side, organizations should block or alert on outbound connections to 194.33.61[.]36 and 109.107.168[.]18 over port 7000, monitor for FRPS protocol fingerprints, and track the unique SSH host key fingerprint associated with 194.33.61[.]36 to catch potential infrastructure rotation within the same hosting provider.
For defenders, high-value host indicators include binary data stored under HKLMSOFTWAREMicrosoftWindowsCurrentVersionExplorer (ShellStateVersion1, IconSizeVersion1, IconUnderlineVersion1), scheduled tasks named DriverSvcTask, NetTcpSvc, TermSvcHost, and WindowsHealthMonitor, hidden local accounts with the password “ADAD,” the ctrlPipe named pipe, and C:Tempkeylog.txt.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.