A powerful new Windows malware family dubbed Salat Stealer, a Go-based Remote Access Trojan (RAT) that blends classic infostealing with a stealthy QUIC/WebSocket command-and-control (C2) channel and resilient blockchain-backed infrastructure.
Written in Go, it supports remote shell access, desktop and webcam streaming, keylogging, clipboard theft, browser and crypto‑wallet data theft, and SOCKS5-based pivoting, giving operators interactive and long-term control over compromised systems.
The malware is typically distributed as a UPX-packed Windows executable and masquerades as legitimate system processes such as explorer.exe, svchost.exe, or lsass.exe to blend into normal process lists and evade quick triage by defenders.
On startup, Salat Stealer calls Go’s os.Executable() API to obtain its own file path, which it then reuses for self-replication, process checks, and cryptographic derivation.
Its configuration and strings are protected by a six‑mode string decryption scheme, including an AES‑128‑GCM mode keyed with the MD5 hash of the constant “biba” and an XOR mode that uses the hex representation of the Russian phrase “Я люблю сосать.”
Salat Stealer goes far beyond a traditional password stealer, operating as a full post-exploitation framework once it lands on a victim host.
To uniquely tag each victim, the malware concatenates the hostname, a hardware identifier (HWID), and a hardcoded salt (LDrx1ePUV27Zt8tq2S14) and hashes the result with MD5, converting the digest to a 32‑character agent ID embedded in every beacon.
It also attempts to escalate privileges via a function named main_Elevate, relaunching itself with administrator rights when possible to widen access to sensitive data and system controls.
Salat Malware Abuses QUIC
Salat Stealer supports multiple runtime modes based on its command-line arguments, enabling operators to deploy it in specialized roles.
A “-k” switch starts a keylogger‑only mode, a three‑argument mode executes JSON‑encoded command arrays, and a four‑argument mode creates a named mutex and waits in a select loop while the default path launches the full RAT feature set.
The integrated keylogger continuously captures keystrokes, allowing attackers to harvest credentials and messages that never get stored in browsers or files, complementing the malware’s extensive browser and token theft capabilities.
For C2, Salat Stealer dynamically probes multiple transports, preferring WebSocket and HTTP/3 (QUIC) for stealthy, low-noise communications that are harder to distinguish from modern web traffic.
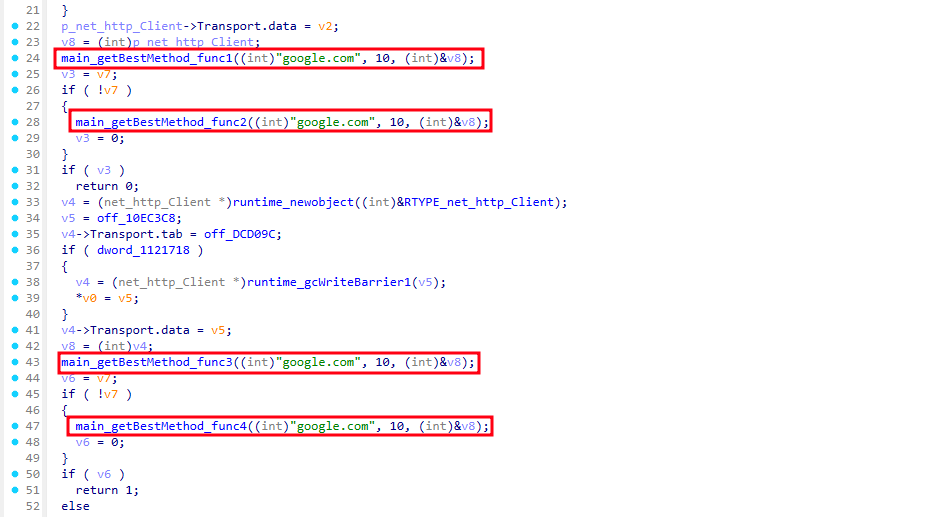
The malware relies on the quic-go and gorilla/websocket libraries, falling back to HTTP/2 when QUIC or WebSocket channels are blocked.
C2 URLs are doubly encrypted inside the binary and decrypted via a chained pipeline of hex decoding and custom modes that culminate in AES‑GCM decryption before yielding five embedded /sa1at/ endpoints across multiple domains and ports.
If repeated connection attempts to all endpoints fail, Salat Stealer queries the TON (The Open Network) blockchain over DNS‑over‑HTTPS, verifies a smart contract using embedded RSA public keys, and decodes fresh C2 configuration, making takedown efforts extremely difficult.
Stealthy C2 Control
Before its first beacon, Salat Stealer enumerates detailed system information via WMI, including GPU and CPU names, OS details, RAM size, active window title, and administrator status, then packs these fields into a JSON object identified by the victim’s agent ID.
This initial registration beacon is encrypted (RSA or AES, depending on the endpoint) and sent to the C2, giving operators rich telemetry to prioritize high‑value hosts.
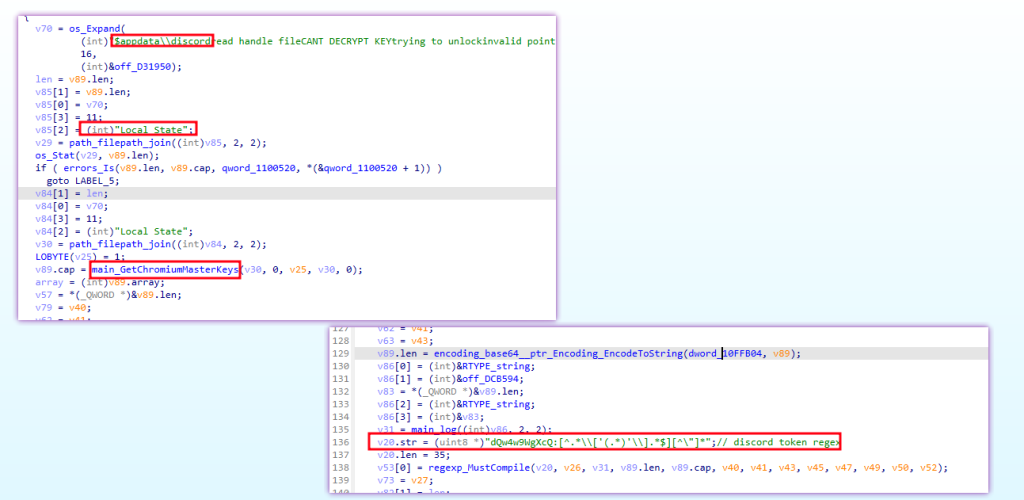
The malware then archives and exfiltrates a wide range of data screenshots, process lists, Discord and Steam tokens, Chromium and Gecko browser data (including DPAPI‑decrypted secrets), and cryptocurrency wallets compressing everything into a ZIP for upload.
A background task loop continuously polls the C2 and executes a wide command set, including sleep, self‑destruct, file download, screenshot capture, interactive shell, data theft, and peer‑to‑peer SOCKS proxying, effectively turning infected systems into remotely operated footholds.
To survive reboots, Salat Stealer combines three persistence methods: copying itself to hidden system locations, creating scheduled tasks that run at logon and every 30 minutes, and adding Run‑key entries under HKCUSOFTWAREMicrosoftWindowsCurrentVersionRun.
Given its QUIC/WebSocket C2, blockchain‑backed resilience, and deep credential theft features, defenders should focus on behavioral EDR detections, QUIC/WebSocket inspection, and monitoring for suspicious scheduled tasks, masquerading binaries, and unusual TON‑related DNS‑over‑HTTPS activity.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.






