Saving time by automating bug bounty reports

Source link
Related Articles
All Mix →[tl;dr sec] #315 – Securing OpenClaw, Top 10 Web Hacking Techniques of 2025, Discovering Negative-Days with LLMs
Table of Contents AI for Security Engineers (with Cursor's Security Lead) AppSec Cloud Security AI + Security AI for Security Engineers (with Cursor’s Security Lead)…
MICROSOFT SAYS: RUSSIAN SOLARWINDS HACKERS HIT U.S. GOVERNMENT AGENCIES AGAIN
According to the New York Times, Microsoft says the state-backed Russian hacker group Nobelium—the same actor behind the 2020 SolarWinds attacks—took control of the State…
Unlocking Engagement with Employee Feedback
Table of Contents The Importance of Employee Feedback Implementing the Surveys Feedback Turns into Action Since 2018, HackerOne has maintained an employee engagement survey participation…
Defense for Vulnerable React Server Component Workflows — API Security
Table of Contents What is CVE-2025-55182? What is CVE-2025-66478? What is the Impact? How Does Wallarm Protect Against These Vulnerabilities? Recommended Remediation Conclusion On December…
What Happens to Content When Top-Tier Production Quality is Commoditized?
I think AI is about to massively improve the quality of our best content. But not for the reason you might expect. Not because AI…
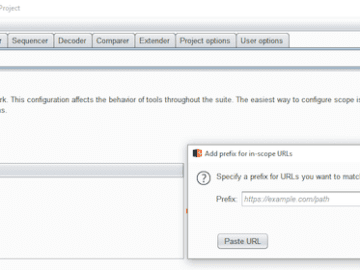
Introducing Unified HackerOne Scope Management with Burp Suite Support
Table of Contents What is a scope? What is Burp Suite? Defining target scope in Burp Suite HackerOne Scope Management Easily Import Scoped Assets into…