Scanning for hardcoded secrets in source code | Security Simplified

Source link
Related Articles
All Mix →An ethical hacker’s perspective on EASM
Table of Contents What is EASM? Why is EASM important? Ephemeral bugs Shadow IT assets Out-of-date assets Acquisitions Asset visibility EASM for ethical hackers Domains…
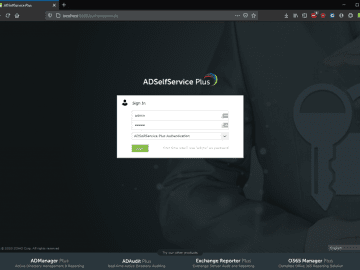
how I bruteforced my way into your Active Directory – honoki
Table of Contents The Target The Setup The Bugs The Exploit The Outcome Timeline Last May, I discovered that a critical vulnerability I had reported…
The Importance of Credential Rotations: Best Practices for Security and Data Protection
Table of Contents The Significance of Credential Rotations Understanding Credential Rotation Categories of Credentials Critical Material (A) Material (B) Non-Material (C) When and Who Performs…
Podcasting + Excercise : A Perfect Match
I think a big part of a person’s strengths is knowing how to properly handle his/her weaknesses. In my case, I hate to be bored.…
On Customer Service | Daniel Miessler
I think a lot about customer service. Or, what I really mean is that I get angry a lot about customer service. I’m not speaking…
Federated ID, OpenID, and OAuth: A Web Authentication Primer
Table of Contents Federated ID Technology OpenID How It Works OAuth Summary Links Federated ID Federated ID, also called Federated Identity Management (FIM), allows a…