A sophisticated multiplatform supply-chain attack orchestrated by the North Korea-aligned APT group ScarCruft, targeting ethnic Koreans in China’s Yanbian region through a compromised gaming platform.
The attack, believed to have been ongoing since late 2024, weaponized both Windows and Android components of sqgame[.]net, a video game platform that hosts traditional Yanbian-themed card and board games.
The threat actor compromised the sqgame.]net platform to distribute trojanized versions of games with the BirdCall backdoor a sophisticated surveillance tool previously known only in Windows versions.
ScarCruft, also known as APT37 or Reaper, has been operating since at least 2012 and is suspected to be a North Korean espionage group.
The gaming platform serves the Yanbian Korean Autonomous Prefecture, a region bordering North Korea that hosts the largest ethnic Korean community outside Korea.
Researchers believe the primary targets are refugees, defectors, and individuals deemed of interest to the North Korean regime.
ScarCruft Targets Gaming Platform
The Windows desktop client received malicious updates through a compromised mono.dll library hosted at the platform’s update server.
The APK available for download on the official website is the same as the APK initially found on VirusTotal.
The trojanized DLL contains a downloader that first checks for analysis tools and virtual machine environments before proceeding.
Once the coast is clear, it downloads and executes shellcode containing the RokRAT backdoor, which subsequently deploys the more sophisticated BirdCall backdoor.
After execution, the malicious mono.dll automatically replaces itself with a clean version downloaded from compromised South Korean websites a typical tactic of ScarCruft that erases visible artifacts.
ESET’s investigation revealed trojanized versions of two Android games: Yanbian Red Ten and New Drawing, both available directly from the sqgame[.]net download page.
The Android version of BirdCall, internally named “zhuagou” (meaning “catching dogs”), represents a new tool in ScarCruft’s arsenal.
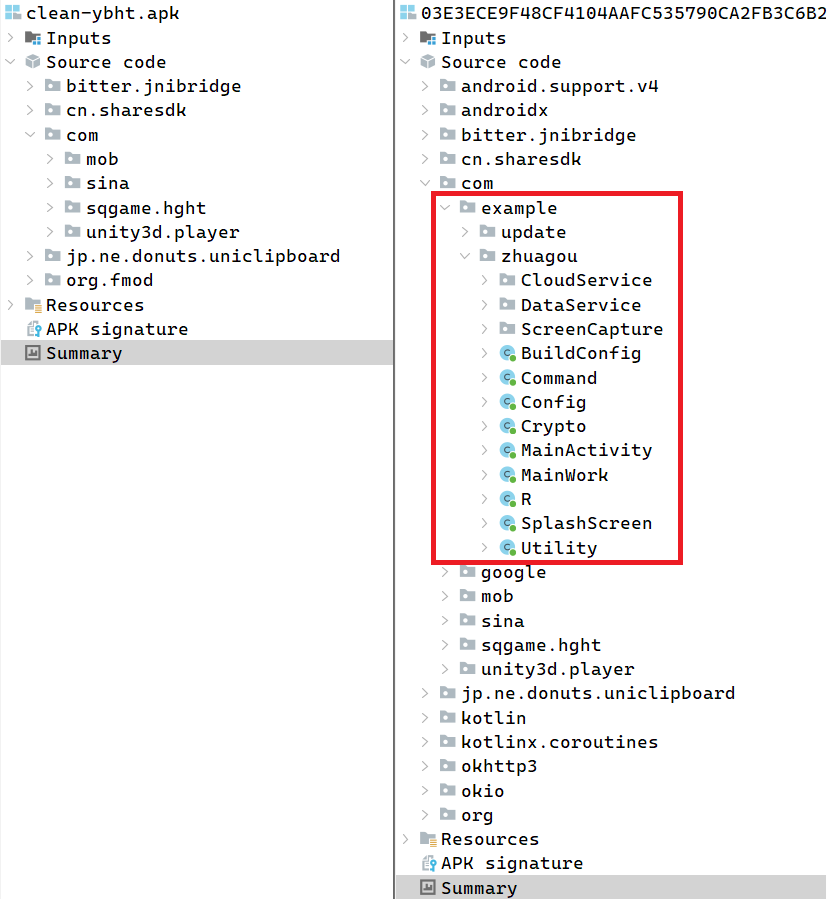
The Android backdoor implements a subset of the Windows version’s capabilities, focusing on data collection and surveillance. It harvests contacts, SMS messages, call logs, documents, and media files with specific extensions including .doc, .docx, .xls, .xlsx, .ppt, .pptx, .txt, .hwp, .pdf, .jpg, .m4a, and .p12.
The targeting of .hwp files used by South Korean Hancom Office confirms the focus on Korean-speaking victims.
Android Backdoors
Both backdoor versions feature extensive spying capabilities. The malware can capture screenshots, with some Android samples playing silent MP3 files in loops to prevent the app from being suspended in the background.
Notably, the Android variant includes microphone recording functionality constrained to a three-hour window between 7 PM and 10 PM local time.
ESET identified seven Android BirdCall versions spanning from version 1.0 in October 2024 to version 2.0 in June 2025, with the latest version adding code obfuscation.
Both Windows and Android versions use legitimate cloud storage services for command-and-control communications, including Dropbox, pCloud, Yandex Disk, and Zoho WorkDrive.
ESET researchers observed twelve Zoho WorkDrive accounts associated with the Android backdoor operations, all registered with zohomail addresses.
The campaign represents a significant evolution in ScarCruft’s capabilities, marking the group’s expansion into multiplatform espionage operations.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.