Security Affairs newsletter Round 490 by Pierluigi Paganini – INTERNATIONAL EDITION

A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free in your email box.
Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.
International Press – Newsletter
Cybercrime
Bad Stark! The cybercriminal’s playground
The Dark Nexus Between Harm Groups and ‘The Com’
Phishing Pages Delivered Through Refresh HTTP Response Header
How scammers bypass customer identity verification using deepfakes
Data on nearly 1 million NHS patients leaked online following ransomware attack on London hospitals
Chinese National Charged for Multi-Year “Spear-Phishing” Campaign
Police Hack Into ‘Ghost’, An Encrypted Platform for Criminals
Global Coalition Takes Down New Criminal Communication Platform
Storm clouds on the horizon: Resurgence of TeamTNT?
Indictment Charges Two in $230 Million Cryptocurrency Scam
An international criminal network dedicated to unlocking stolen mobile phones and stealing the digital lives of victims has been dismantled
More than $44 million in cryptocurrency stolen from Singaporean platform BingX
Malware
CISA warns of Windows flaw used in infostealer malware attacks
Exotic SambaSpy is now dancing with Italian users
Loki: a new private agent for the popular Mythic framework
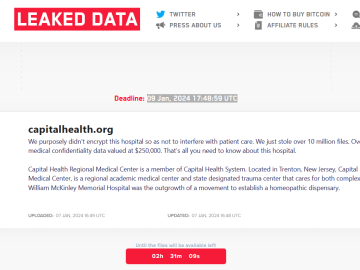
Microsoft: US Healthcare Sector Targeted by INC Ransomware Affiliate
Hacking
Hacker tricks ChatGPT into giving out detailed instructions for making homemade bombs
Microsoft Says Recent Windows Vulnerability Exploited as Zero-Day
Sabotage by Signal: An Investigative Report into Lebanon’s Deadly Pager Explosions and How Cyber Warfare Hijacked Communication
China Using Powerful Hacking Firms to Run Its Espionage War
US government ‘took control’ of a botnet run by Chinese government hackers, says FBI director
Ivanti warns of another critical CSA flaw exploited in attacks
Password Spraying Detection in Active Directory
Air-Gapped Networks Vulnerable to Acoustic Attack via LCD Screens
A Journey From sudo iptables To Local Privilege Escalation
This Windows PowerShell Phish Has Scary Potential
Intelligence and Information Warfare
US Space Forces stops use of AI tools for information security concerns
North Korean Hackers Target Cryptocurrency Users on LinkedIn with RustDoor Malware
Hezbollah vows to punish Israel after pager explosions across Lebanon
Hezbollah pagers explode across Lebanon, causing thousands of injuries
An Offer You Can Refuse: UNC2970 Backdoor Deployment Using Trojanized PDF Reader
Derailing the Raptor Train
An Offer You Can Refuse: UNC2970 Backdoor Deployment Using Trojanized PDF Reader
Russian election interference efforts focus on the Harris-Walz campaign
UNC1860 and the Temple of Oats: Iran’s Hidden Hand in Middle Eastern Networks
The NCCC has decided to restrict the use of Telegram in government agencies, military formations, and critical infrastructure facilities
Spotlight, Spy Way of Life | France The Peninsula Paris, a luxury hotel turned spy hub by Gaza and Ukraine crisis
Cybersecurity
Apple seeks to drop its lawsuit against Israeli spyware pioneer NSO
Enterprise ServiceNow Knowledge Bases at Risk: Extensive Data Exposures Uncovered
Treasury Sanctions Enablers of the Intellexa Commercial Spyware Consortium
NSA’s secret Amazon-developed cloud environment progressing ‘very well’
Chrome Introduces One-Time Permissions and Enhanced Safety Check for Safer Browsing
Discord launches end-to-end encrypted voice and video chats
Doctor Web resumed virus database updates after the attack on its infrastructure
Apple’s new macOS Sequoia update is breaking some cybersecurity tools
“Bad Romance”: How Kaspersky Lab Failed to Conquer the Western Cybersecurity Market
Is Tor still safe to use?
Investigations in the so-called darknet: Law enforcement agencies undermine Tor anonymisation
CISA boss: Makers of insecure software are the real cyber villains
FTC exposes massive surveillance of kids, teens by social media giants
Former OpenAI Employee Leaks AGI Progress Documents to Congress
Internet surveillance firm Sandvine says it’s leaving 56 ‘non-democratic’ countries
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Subscribe to the newsletter for free here:
https://www.linkedin.com/build-relation/newsletter-follow?entityUrn=7093942975545667584
Pierluigi Paganini
(SecurityAffairs – hacking, newsletter)