Security Affairs newsletter Round 572 by Pierluigi Paganini – INTERNATIONAL EDITION

A new round of the weekly Security Affairs newsletter has arrived! Every week, the best security articles from Security Affairs are free in your email box.
Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press.
International Press – Newsletter
IOCTA 2026 – The evolving threat landscape: how encryption, proxies and AI are expanding cybercrime
Germany Doxes “UNKN,” Head of RU Ransomware Gangs REvil, GandCrab
Storm-1175 focuses gaze on vulnerable web-facing assets in high-tempo Medusa ransomware operations
BreachForums Data Leaks: Technical Analysis and Timeline Attribution (2022–2026)
Cryptocurrency ATM giant Bitcoin Depot reports $3.6 million stolen in cyberattack
Company that supplies software for patient records attacked by hackers
Senator launches inquiry into 8 tech giants for failures to adequately report CSAM
Malware
Thirty-Six Malicious npm Strapi Packages Deploy Redis RCE, Database Theft, and Persistent C2
Masjesu Rising: The Commercial IoT Botnet Built for Stealth, DDoS, and IoT Evasion
EXPMON detected sophisticated zero-day fingerprinting attack targeting Adobe Reader users
Critical Supply Chain Compromise in Smart Slider 3 Pro: Full Malware Analysis
GlassWorm goes native: New Zig dropper infects every IDE on your machine
CPUID hacked to deliver malware via CPU-Z, HWMonitor downloads
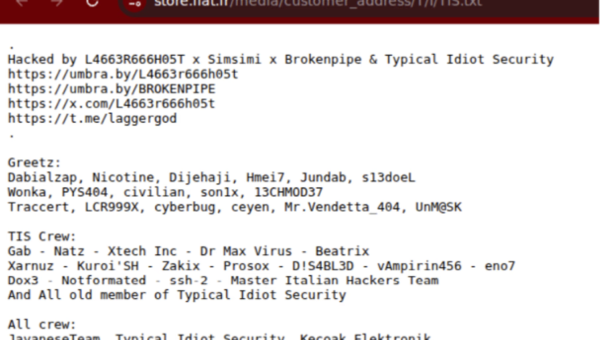
Hacking
A hacker has allegedly breached one of China’s supercomputers and is attempting to sell a trove of stolen data
Over 14,000 F5 BIG-IP APM instances still exposed to RCE attacks
Fortinet Patches Actively Exploited CVE-2026-35616 in FortiClient EMS
GPUBreach: Privilege Escalation Attacks on GPUs using Rowhammer
Critical Flowise Vulnerability in Attacker Crosshairs
Anthropic Claims Its New A.I. Model, Mythos, Is a Cybersecurity ‘Reckoning’
CVE-2026-25769: Critical Remote Code Execution in Wazuh via Unsafe Deserialization
Intent redirection vulnerability in third-party SDK exposed millions of Android wallets to potential risk
Marimo OSS Python Notebook RCE: From Disclosure to Exploitation in Under 10 Hours
Intelligence and Information Warfare
DPRK-Related Campaigns with LNK and GitHub C2
Malicious LNK Files Distributing a Python-Based Backdoor and Changes in Distribution Techniques (Kimsuky Group)
Russia’s banks face major service outages amid internet crackdown
Iranian-Affiliated Cyber Actors Exploit Programmable Logic Controllers Across US Critical Infrastructure
Britons warned about Russian hackers targeting internet routers for espionage
Pawn Storm Campaign Deploys PRISMEX, Targets Government and Critical Infrastructure Entities
APT28 exploit routers to enable DNS hijacking operations
ICE acknowledges it is using powerful spyware
Artificial Intelligence and Foreign Information Manipulation: Chinese and Russian approaches
New Lua-based malware “LucidRook” observed in targeted attacks against Taiwanese organizations
UK says it exposed Russian submarine activity near undersea cables
Beyond BITTER: MENA Civil Society Targeted in Hack-For-Hire Operation Linked to BITTER APT
Iranian-Affiliated APT Targeting of Rockwell/Allen-Bradley PLCs
Cybersecurity
‘It’s a real shock’: quantum-computing breakthroughs pose imminent risks to cybersecurity
The political effects of X’s feed algorithm
Project Glasswing
Critical Infrastructure at Risk: 179 ICS Devices Exposed Online
ICE acknowledges it is using powerful spyware
The-broken-physics-of-remediation
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, newsletter)