A set of 21 newly discovered vulnerabilities impact Sierra OT/IoT routers and threaten critical infrastructure with remote code execution, unauthorized access, cross-site scripting, authentication bypass, and denial of service attacks.
The flaws discovered by Forescout Vedere Labs affect Sierra Wireless AirLink cellular routers and open-source components like TinyXML and OpenNDS (open Network Demarcation Service).
AirLink routers are highly regarded in the field of industrial and mission-critical applications due to high-performance 3G/4G/5G and WiFi and multi-network connectivity.
Various models are used in complex scenarios like passenger WiFi in transit systems, vehicle connectivity for emergency services, long-range gigabit connectivity to field operations, and various other performance-intensive tasks.
Forescout says Sierra routers are found in government systems, emergency services, energy, transportation, water and wastewater facilities, manufacturing units, and healthcare organizations.

Flaws and impact
Forescout’s researchers discovered 21 new vulnerabilities in Sierra AirLink cellular routers and the TinyXML and OpenNDS components, which are part of other products, too.
Only one of the security issues has been rated critical, eight of them received a high severity score, and a dozen present a medium risk.
The most noteworthy vulnerabilities are summarized below:
- CVE-2023-41101 (Remote Code Execution in OpenDNS – critical severity score of 9.6)
- CVE-2023-38316 (Remote Code Execution in OpenDNS – high severity score of 8.8)
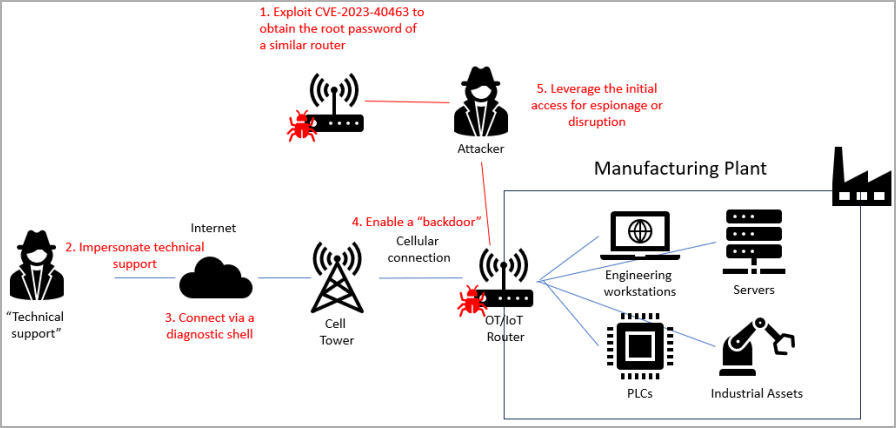
- CVE-2023-40463 (Unauthorized Access in ALEOS – high severity score of 8.1)
- CVE-2023-40464 (Unauthorized Access in ALEOS – high severity score of 8.1)
- CVE-2023-40461 (Cross Site Scripting in ACEmanager – high severity score of 8.1)
- CVE-2023-40458 (Denial of Service in ACEmanager – high severity score of 7.5)
- CVE-2023-40459 (Denial of Service in ACEmanager – high severity score of 7.5)
- CVE-2023-40462 (Denial of Service in ACEmanager related to TinyXML – high severity score of 7.5)
- CVE-2023-40460 (Cross Site Scripting in ACEmanager – high severity score of 7.1)
For at least five of the above flaws, attackers do not require authentication to exploit them. For several others affecting OpenNDS, authentication is likely not required, as common attack scenarios involve clients attempting to connect to a network or service.
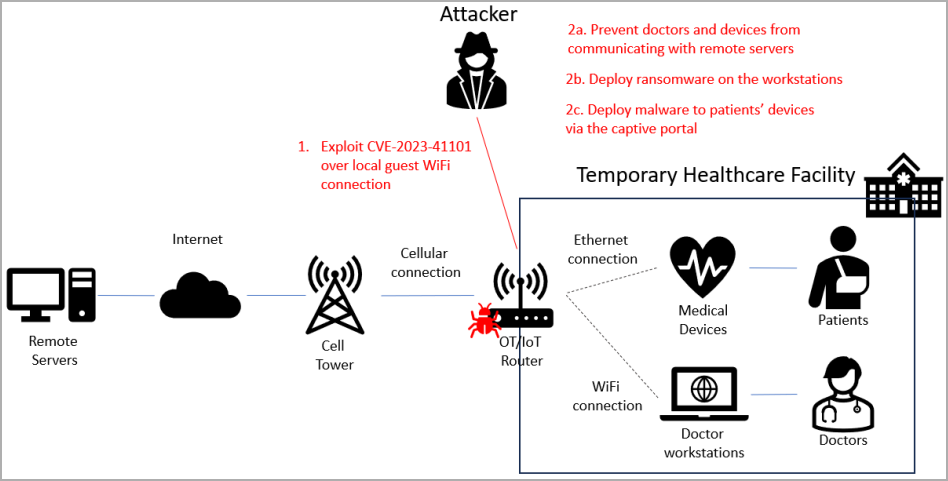
According to the researchers, an attacker could exploit some of the vulnerabilities “to take full control of an OT/IoT router in critical infrastructure.” The compromise could lead to network disruption, enable espionage, or move laterally to more important assets, and malware deployment.
“Apart from human attackers, these vulnerabilities can also be used by botnets for automatic propagation, communication with command-and-control servers, as well as performing DoS attacks,” the researchers explain.
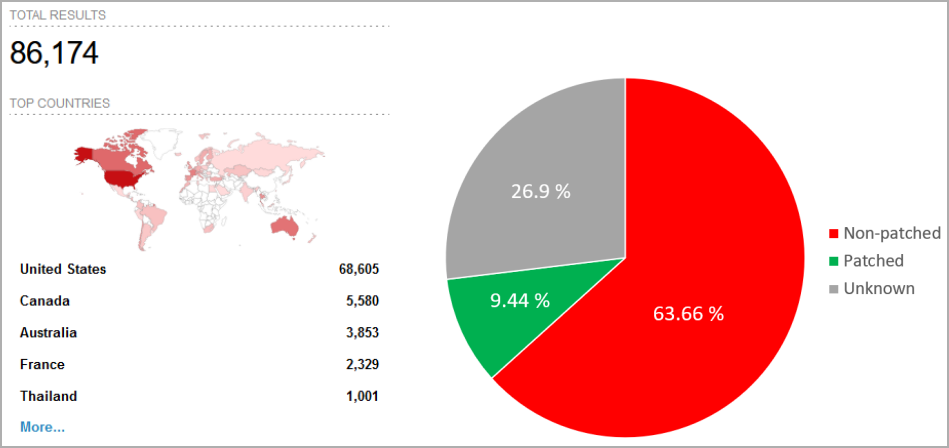
After running a scan on Shodan search enging for internet-connected devices, Forescout researchers found over 86,000 AirLink routers exposed online in critical organizations engaged in power distribution, vehicle tracking, waste management, and national health services.
About 80% of the exposed systems are in the United States, followed by Canada, Australia, France, and Thailand.
Of those, fewer than 8,600 have applied patches to vulnerabilities disclosed in 2019, and more than 22,000 are exposed to man-in-the-middle attacks due to using a default SSL certificate.
Remediation advice
The recommended action for administrators is to upgrade to the ALEOS (AirLink Embedded Operating System) version 4.17.0, which addresses all flaws, or at least ALEOS 4.9.9, which contains all fixes except for those impacting OpenNDS captive portals that set a barrier between the public internet and a local area network.
The OpenNDS project has also released security updates for the vulnerabilities impacting the open-source project, with version 10.1.3.
Note that TinyXML is now abandonware, so there will be no fixes for the CVE-2023-40462 vulnerability that impacts the project.
Forescout also recommends taking the following additional actions for enhanced protection:
- Change default SSL certificates in Sierra Wireless routers and similar devices.
- Disable or restrict non-essential services like captive portals, Telnet, and SSH.
- Implement a web application firewall to protect OT/IoT routers from web vulnerabilities.
- Install an OT/IoT-aware IDS to monitor external and internal network traffic for security breaches.
Forescout has released a technical report that explains the vulnerabilities and the conditions that allow exploiting them.
According to the company, threat actors are increasingly targeting routers and network infrastructure environments, launching attacks with custom malware that use the devices for persistence and espionage purposes.
For cybercriminals, routers are usually a means to proxy malicious traffic or to increase the size of their botnet.