- Cloud Risk Is No Longer Unpredictable. It Is Settling Into a Pattern.
- Three Defining Signals That Change How Cloud Risk Should Be Read
- 1. Identity architecture is deciding who wins the breach race
- 2. Agentic AI is making exploitability the new unit of cloud risk prioritization
- 3. Cloud environments change instantly, while remediation still moves by ticket
- Access and Response Speed Now Decide Cloud Security Outcomes
- Contributors
- Frequently Asked Questions (FAQs)
- Why is remediation speed becoming critical in cloud security?
- What is attack-path analysis in cloud security?
- How are AI workloads expanding the cloud attack surface?
Key Takeaways
- Identity and permissions now determine what is reachable, making them the primary drivers of cloud risk.
- Runtime exposure, not individual findings, determines how low-risk issues combine into real impact.
- SaaS and OAuth integrations extend the control plane and amplify blast radius through delegated trust.
- Supply chain and CI/CD pipelines introduce risk before deployment, often bypassing runtime controls.
- Detection is widespread, but remediation delays create exploitable exposure windows.
- Agentic AI systems can continuously enumerate identities, permissions, and trust relationships, accelerating the discovery of privilege escalation paths.
Cloud Risk Is No Longer Unpredictable. It Is Settling Into a Pattern.
Across most enterprise environments, the same conditions produce the same outcomes. Identities carry more access than required. Trust relationships extend beyond clear boundaries. Exposure lingers longer than intended. Nothing appears broken in isolation, yet together these elements create a system where security compromise follows a familiar path.
The Cloud Security Forecast 2026 brings these signals into focus. The data does not point to a surge in novel attack techniques. It reflects something more uncomfortable. The same identity relationships, permission inheritance models, and delegated trust paths are producing consistent compromise patterns across organizations, independent of cloud provider or industry.
The insights from Qualys Threat Research Unit (TRU), together with findings from the Qualys Cloud and Application Security Maturity Survey 2026 conducted in collaboration with more than 250 global enterprises, point to a structural reality. Cloud exposure is not an outlier to investigate, but an expected byproduct of how modern enterprise environments are designed and operated. The new cloud landscape, shaped by AI capabilities and unprecedented scale, requires disinheriting the question of where risk might emerge and refocusing on how long that risk remains in place once it appears.
Qualys Insights
Three Defining Signals That Change How Cloud Risk Should Be Read
With these insights, it is becoming clearer that risk rarely arises from a single flaw. It forms through how identities, pipelines, SaaS integrations, and AI-connected services interact across the environment. In cloud architectures defined by delegated trust and automation, exposure increasingly reflects how systems connect rather than what breaks.
1. Identity architecture is deciding who wins the breach race
In cloud environments, authority is encoded in IAM policies, role inheritance, and federated trust relationships. When these relationships combine across service accounts, workload identities, and delegated roles, they create permission graphs that can enable privilege escalation without exploiting a single vulnerability.
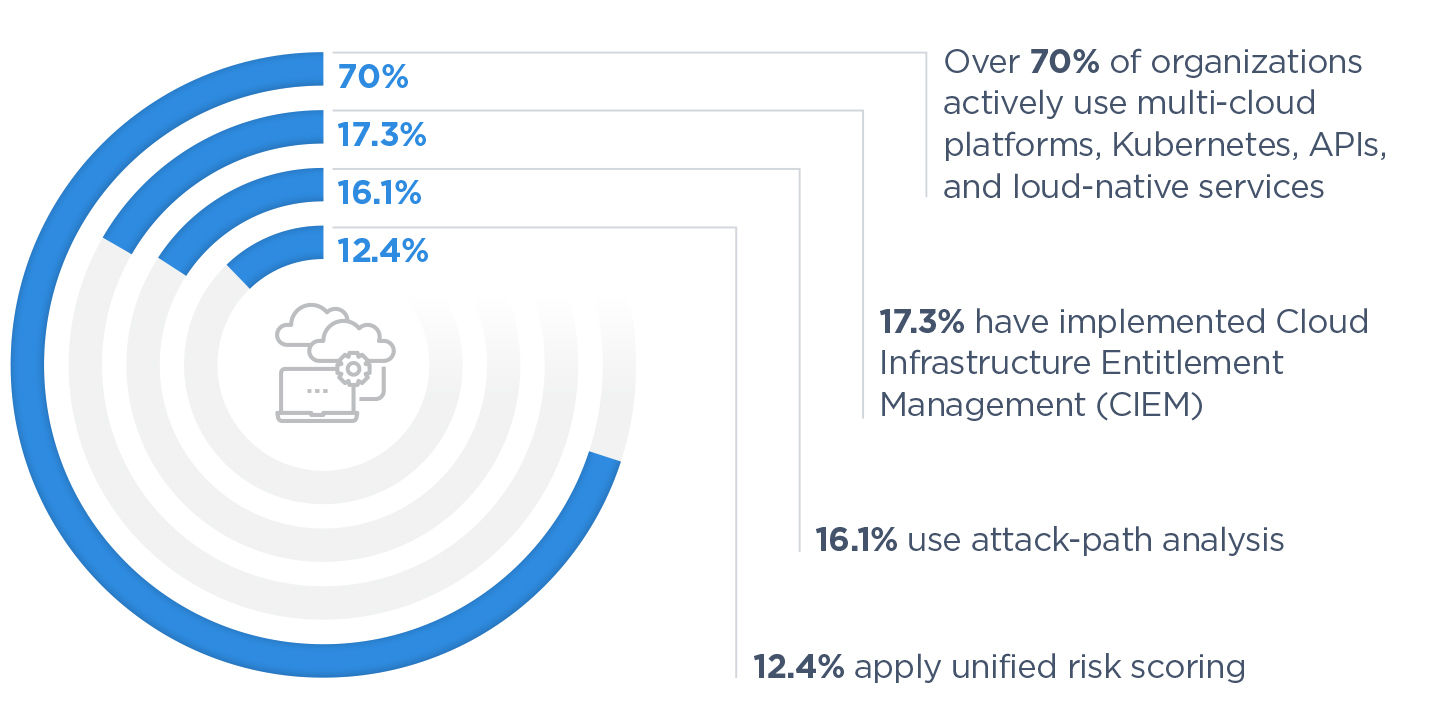
Yet governance maturity remains limited: only 17.3% of organizations have implemented Cloud Infrastructure Entitlement Management (CIEM), and just 26.1% incorporate identity context into risk prioritization. Large portions of the identity landscape remain unexamined, leaving reachable access paths that traditional configuration reviews rarely model end-to-end and that are only discovered when they are abused.
2. Agentic AI is making exploitability the new unit of cloud risk prioritization
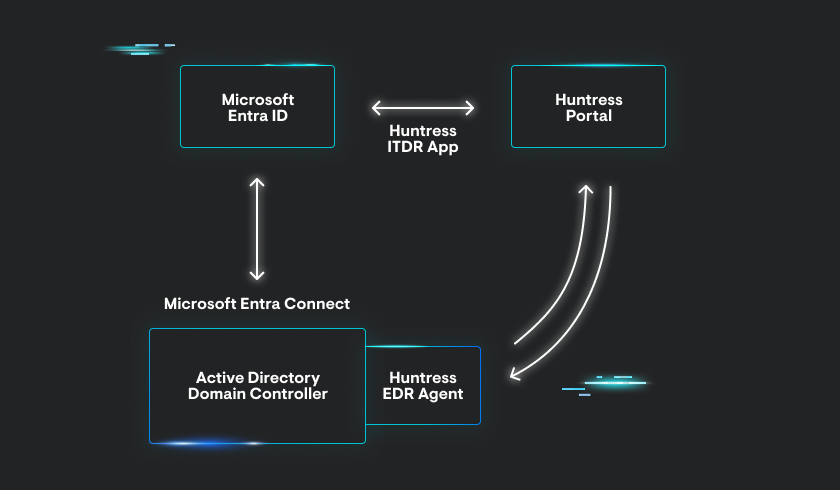
Agentic systems can continuously enumerate identities, policies, OAuth scopes, and trust relationships across cloud control planes, constructing permission graphs that reveal escalation paths humans rarely detect manually.
This collapses a long-standing divide in cloud security operations, where vulnerability teams analyze CVEs while infrastructure and identity teams investigate access paths in separate workflows. Agentic reasoning correlates these signals, exposing the conditions that create an actual path to compromise rather than isolated technical findings.
Adoption is advancing quickly. With 35.7% of organizations already operating AI or LLM workloads but only 19.1% reporting adequate visibility and controls, the infrastructure capable of reasoning over identity relationships is expanding faster than the governance models designed to supervise it.
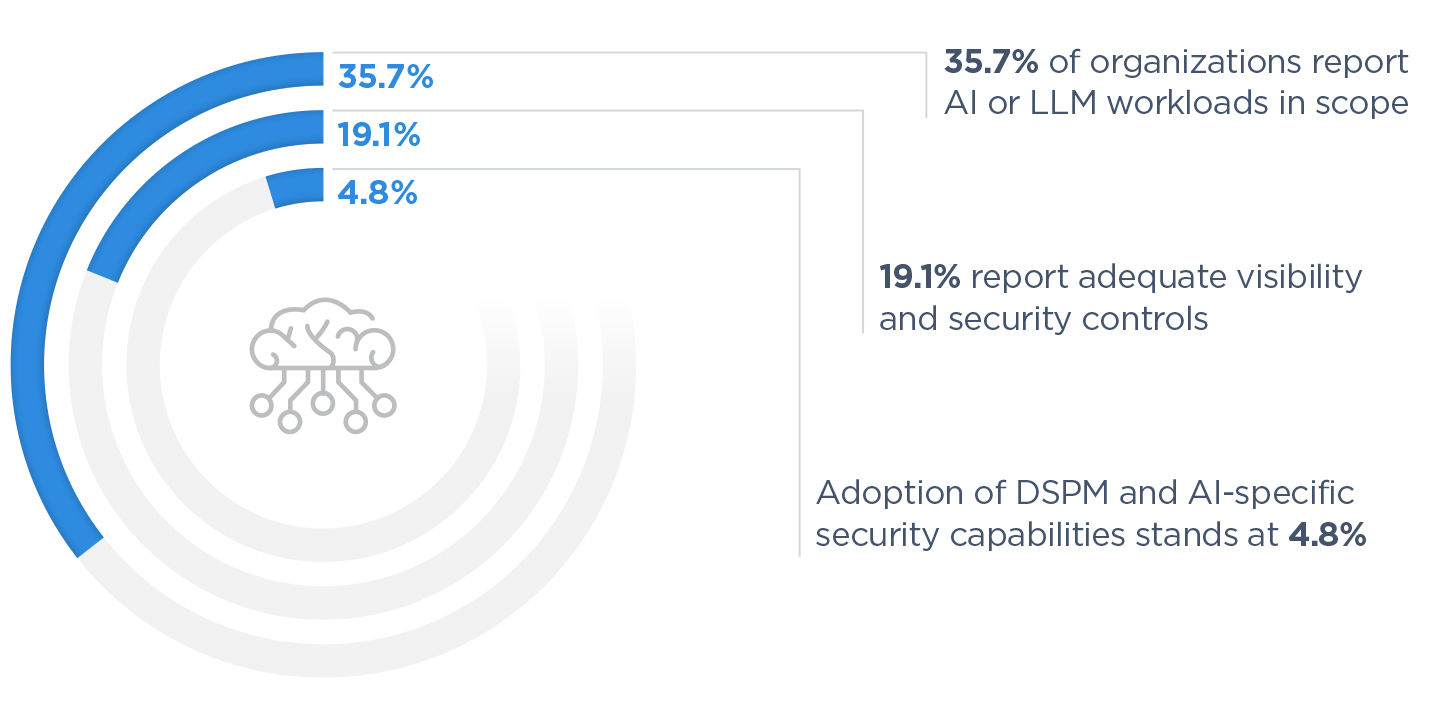
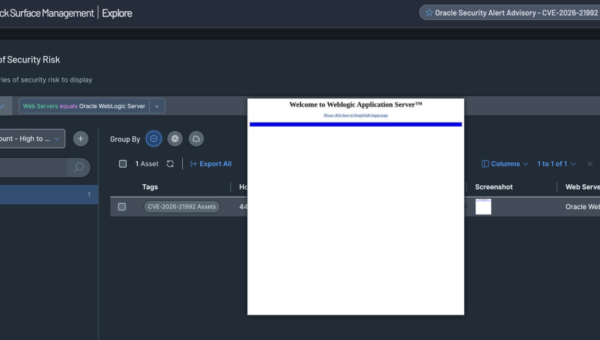
At the same time, AI is widening the attack surface. Model endpoints, agents, vector stores, and tool integrations introduce new machine identities and quiet trust relationships across the cloud. Attackers exploit the seams. Instead of a single flaw, they stitch together low-severity conditions such as stale OAuth grants, over-privileged service accounts, exposed CI/CD secrets, or permissive APIs into escalation paths.
3. Cloud environments change instantly, while remediation still moves by ticket
Infrastructure-as-code, CI/CD pipelines, and ephemeral workloads continuously introduce new roles, secrets, service accounts, and network paths into cloud environments. Each deployment can alter access relationships long before governance processes review the change.
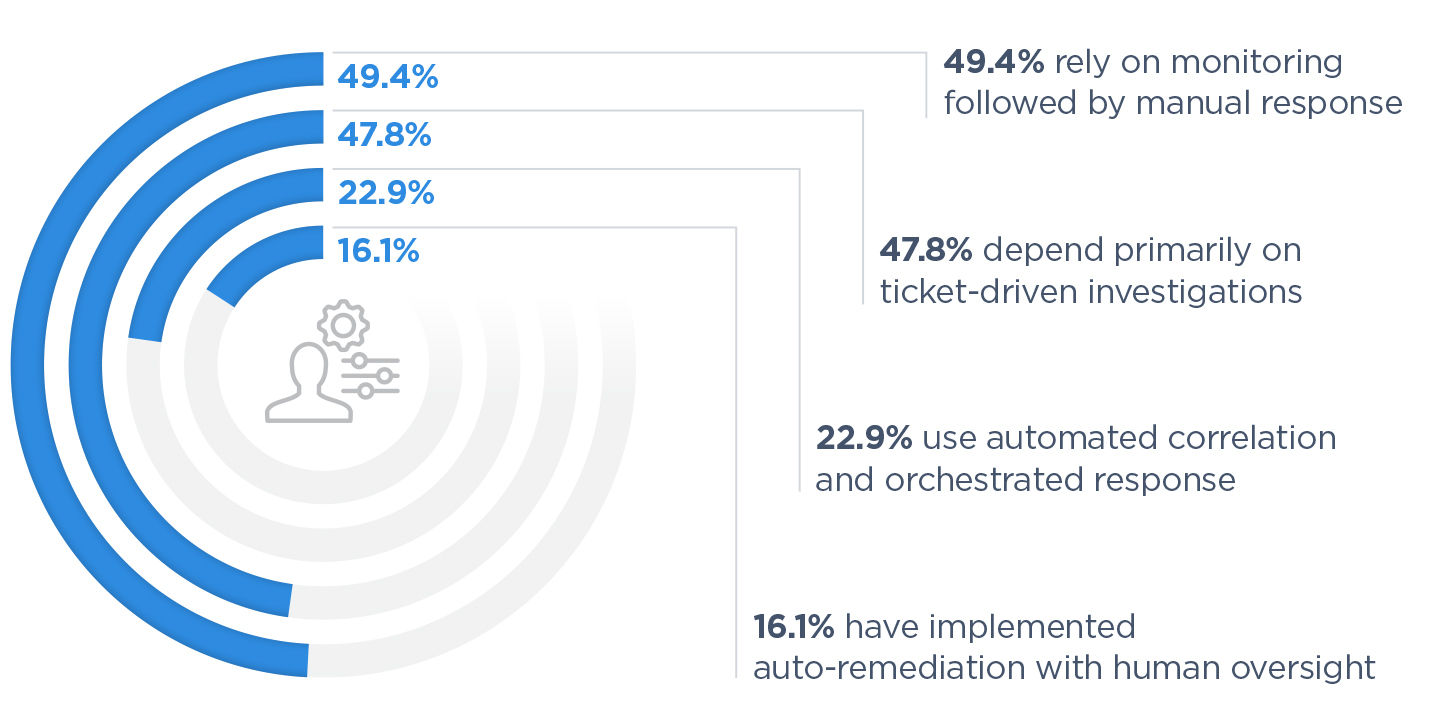
Yet 49.4% of organizations still rely on monitoring followed by manual response workflows, creating a structural delay between configuration changes and remediation actions that attackers can exploit.
Taken together, these signals point to a deeper shift in how cloud risk is forming. Identity systems, SaaS integrations, software supply chains, and AI workloads are no longer peripheral components of the environment. Their interactions increasingly determine how access propagates and how compromise unfolds across modern cloud architectures.
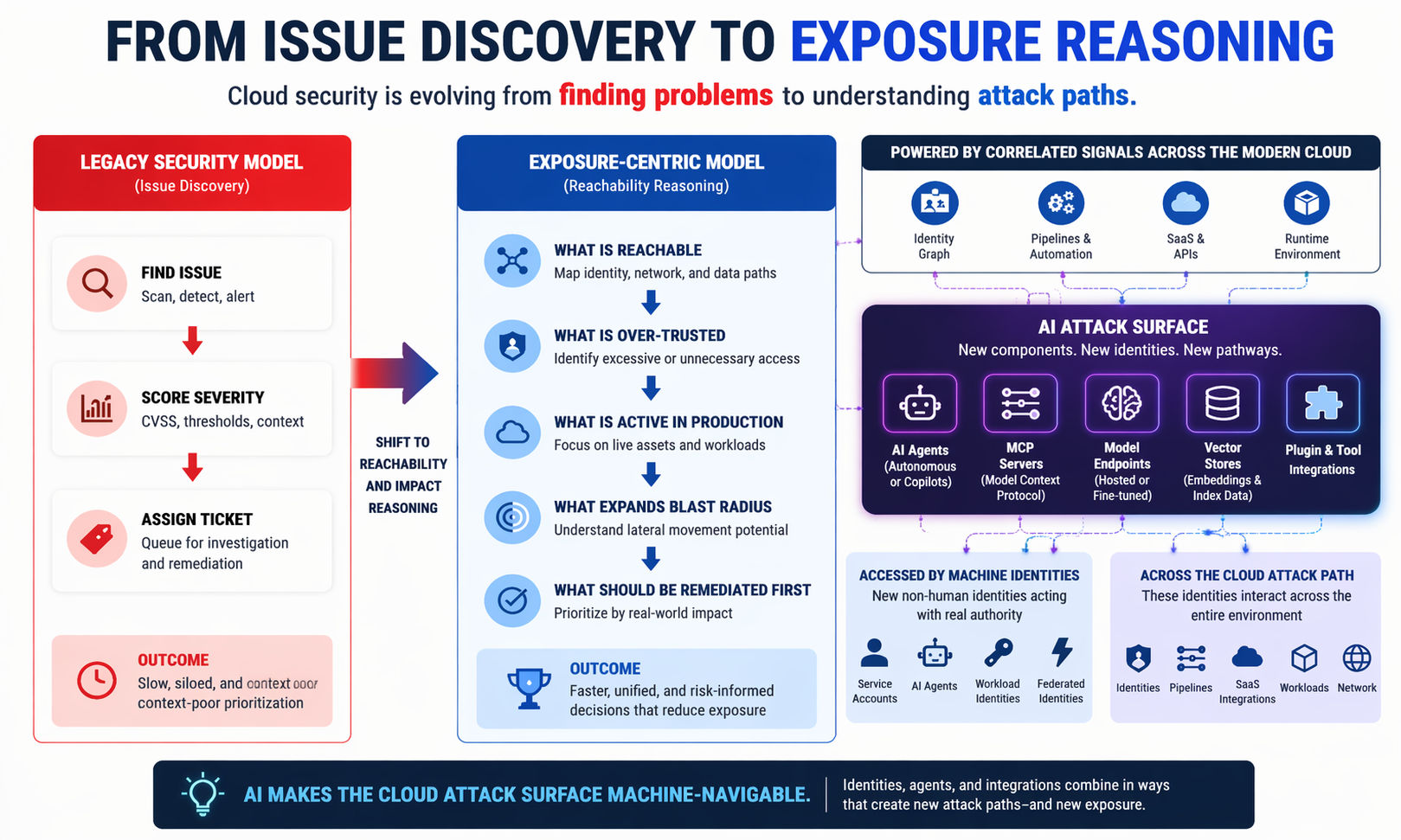
Exposure management is shifting from cataloging issues toward understanding reachability, asking not only what is vulnerable but which combinations of identities, configurations, and integrations create a viable path to impact.
Access and Response Speed Now Decide Cloud Security Outcomes
Cloud environments now operate as fluid systems of access relationships. Identities, services, integrations, and pipelines continuously redefine what systems can reach, modify, or extract across the environment.
As the Cloud Security Forecast 2026 highlights, the implication is less about adding controls and more about reducing fragmentation across the cloud control plane. Cloud security must operate as a connected system in which signals are correlated in real time, risk is interpreted in the context of actual access, and decisions translate directly into enforced action rather than into queued investigation.
This shifts the center of gravity from monitoring toward control. Enforcement moves upstream into pipelines, identity is continuously rationalized across environments, and high-confidence actions execute without delay while governance remains intact. The advantage will not come from seeing more signals. It will come from reducing unnecessary access at the same pace at which it is created.
Get the full Cloud Security Forecast 2026 report for deeper insight into how identity, automation, and decision speed are reshaping cloud security in 2026.
Contributors
- Rahul Pareek, Senior Security Analyst, Cloud, Qualys
- Atul Parmar, Senior Security Analyst, Cloud, Qualys
- Abhinav Mishra, Director, Product Management, TotalCloud Kubernetes and Container Security, Qualys
Frequently Asked Questions (FAQs)
What is driving most cloud security incidents today?
Most cloud incidents originate from misgoverned identities and access relationships rather than software vulnerabilities. Excessive IAM permissions, long-lived credentials, service accounts, and delegated trust relationships often allow attackers to operate through legitimate APIs once authenticated.
Why are identity permissions becoming the primary cloud attack surface?
In cloud architectures, authority is encoded in IAM policies, roles, and trust relationships rather than network boundaries. When these permissions combine across users, workloads, service accounts, and federated identities, they form permission graphs that can enable privilege escalation or data access without exploiting a vulnerability.
What is Cloud Infrastructure Entitlement Management (CIEM)?
CIEM tools analyze cloud identity permissions, role inheritance, and trust relationships to identify excessive privileges and risky access paths. By continuously mapping IAM graphs across cloud environments, CIEM helps security teams enforce least privilege and prevent privilege escalation.
How do SaaS integrations and OAuth increase cloud risk?
SaaS integrations and OAuth applications introduce persistent delegated access to cloud data and services. When scopes are overly broad or tokens persist for long periods, attackers who compromise those integrations can access sensitive systems without triggering traditional infrastructure defenses.
How does agentic AI change cloud security risk?
Agentic systems can continuously enumerate identities, permissions, and trust relationships across cloud control planes. By reasoning over IAM graphs and configuration changes at machine speed, they can identify privilege escalation paths and exposed access far faster than traditional human-driven analysis.
Why is remediation speed becoming critical in cloud security?
Cloud environments change continuously through CI/CD pipelines, infrastructure-as-code, and ephemeral workloads. New permissions, secrets, and integrations can appear within minutes. If remediation processes rely on manual review and ticket workflows, exposure can persist long enough for attackers to discover and exploit it.
What is attack-path analysis in cloud security?
Attack-path analysis evaluates how identities, permissions, network paths, and misconfigurations combine into viable escalation routes. Instead of scoring findings individually, it models how an attacker could move through the environment to reach sensitive systems or data.
How are AI workloads expanding the cloud attack surface?
AI pipelines introduce new identities, data pipelines, model endpoints, and inference services that interact with cloud infrastructure. These components often require privileged access to storage, compute, and APIs, expanding the identity and data access surface that must be governed.