A threat actor known as Silver Fox is targeting Japanese organizations with a new wave of spearphishing attacks timed to coincide with the country’s busy tax-filing and corporate restructuring season.
The campaign focuses heavily on manufacturers and enterprises that are currently dealing with high volumes of financial and HR-related communications.
This seasonal timing is deliberate. During this period, employees expect emails about salary adjustments, tax filings, and personnel changes, making them more likely to trust malicious messages disguised as routine internal communication.
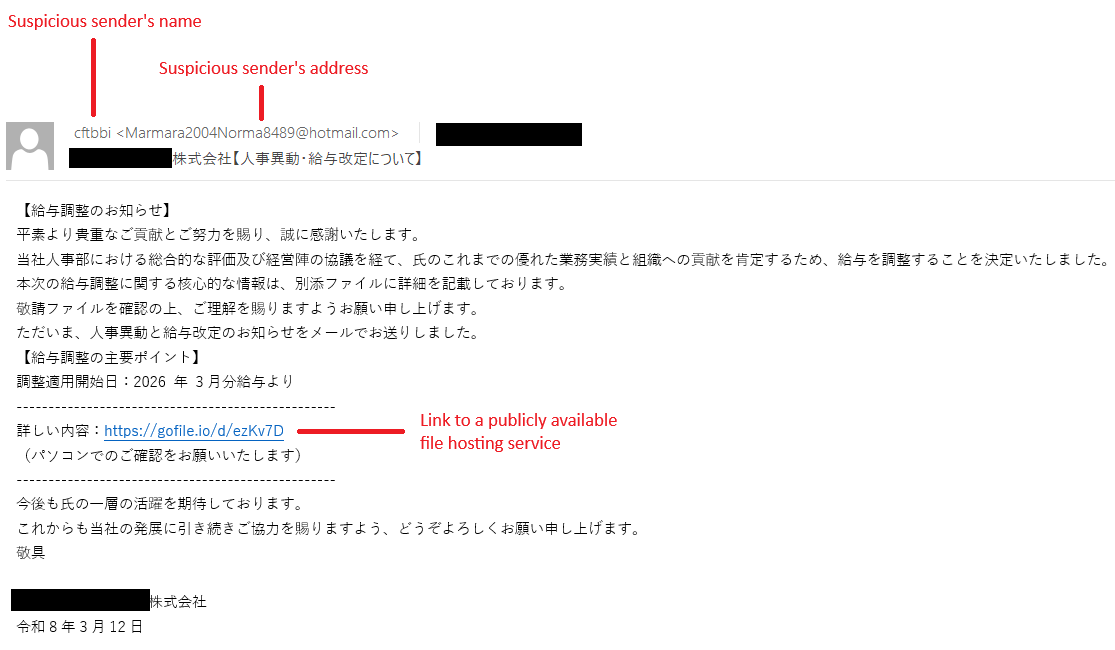
The attackers are sending carefully crafted emails that impersonate HR departments, finance teams, or even company executives. These messages often include the target company’s name in the subject line to increase credibility.
Common themes observed in the campaign include tax compliance violations, employee stock ownership plan updates, and salary revisions.
Example lures reference topics such as “Personnel Changes and Salary Adjustments” or “Tax Compliance and Penalty Notices,” all designed to create urgency and prompt quick action.
According to the report, Silver Fox initially focused on Chinese-speaking targets before expanding into Southeast Asia, Japan, and potentially North America, running each campaign in a local language.
To further enhance legitimacy, Silver Fox uses real employee names in the sender field. This indicates prior reconnaissance, suggesting the campaign is highly targeted rather than mass spam.
Malware Delivery and Impact
The phishing emails typically contain malicious attachments or links leading to downloadable files. These files are disguised as HR or financial documents, often using familiar naming conventions to avoid suspicion.
Once opened, the payload deploys ValleyRAT, a remote access trojan previously linked to Silver Fox operations. Detected as Win64/Valley, this malware enables attackers to:
- Gain full remote control of infected systems.
- Steal sensitive corporate data.
- Monitor user activity.
- Maintain long-term persistence within networks.
This level of access allows threat actors to move laterally, escalate attacks, and potentially stage further compromises across the organization.
Active since at least 2023, Silver Fox initially focused on Chinese-speaking targets but has since expanded its operations across Southeast Asia, Japan, and parts of North America.
The group has targeted multiple sectors, including finance, healthcare, education, government, and even cybersecurity firms.
Notably, the group has a history of aligning campaigns with regional business cycles. Similar tax-themed phishing activity was observed in Japan during the same period last year, highlighting a consistent and strategic approach.
Mitigations
Despite their convincing appearance, these phishing emails often contain subtle red flags. Organizations should reinforce awareness and encourage employees to verify all financial or HR-related requests through separate communication channels.
Key precautions include:
- Verifying sender email addresses, even if the name appears familiar.
- Avoiding downloads from public file-sharing platforms like WeTransfer or GoFile.
- Checking whether the request aligns with standard company processes.
- Being cautious of unusual language or tone inconsistencies.
- Inspecting compressed attachments such as ZIP or RAR files before opening.
Security teams should also ensure endpoint protection tools are updated and actively monitoring for threats like ValleyRAT.
The Silver Fox campaign underscores how attackers exploit predictable business cycles to increase success rates. With employees under pressure to process time-sensitive tasks, even well-trained staff may overlook warning signs.
Organizations operating in Japan and elsewhere should treat seasonal phishing spikes as a recurring threat pattern. Prompt reporting of suspicious emails and proactive user awareness remain critical to preventing compromise.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.