A DShield honeypot sensor recently recorded a complete compromise sequence involving a self-replicating SSH worm that exploits weak passwords to spread across Linux systems.
The incident highlights how poor SSH hygiene and the use of default credentials remain among the most persistent threats to Internet-connected devices.
Even in 2026, attackers continue leveraging automated credential stuffing and brute-forcing tools to take over Linux and IoT systems within seconds.
During a recent internship project, the DShield sensor addressed a real-world attack chain combining credential brute forcing, multi-stage malware drop, persistent backdoor creation, and command-and-control (C2) behavior over IRC channels.
Timeline of the Compromise
- 08:24:13: Attacker connects from IP 83.135.10.12.
- 08:24:14: Brute-force success using credentials pi / raspberryraspberry993311.
- 08:24:15: 4.7 KB bash script uploaded via SCP.
- 08:24:16: Script executed; persistence established.
- 08:24:17: Attacker disconnects, worm initiates C2 check-in and active scanning.
Within only four seconds, the system was fully converted into a botnet node.
The connection originated from 83.135.10.12, traced to Versatel Deutschland, a German ISP. The attacker’s SSH fingerprint (SSH-2.0-OpenSSH_8.4p1 Raspbian-5+b1, HASSH: ae8bd7dd09970555aa4c6ed22adbbf56) suggests the source was another already compromised Raspberry Pi.
Such devices, often left online with default settings, have become ideal targets for use in large-scale botnets.
Seconds after authentication, the attacker deployed a small bash script designed to achieve persistence, turn off competing malware, and modify the system’s host file to redirect a known C2 domain to a loopback address.
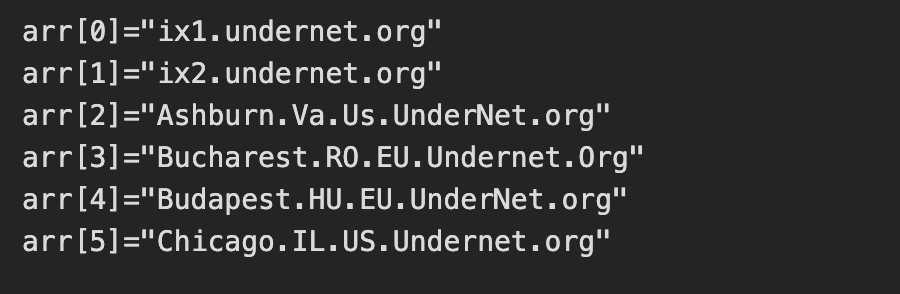
Next, the malware established communication with the operator through six IRC networks, joining a channel named #biret.
The uploaded and executed script was a 4.7KB bash script captured by the DShield sensor.
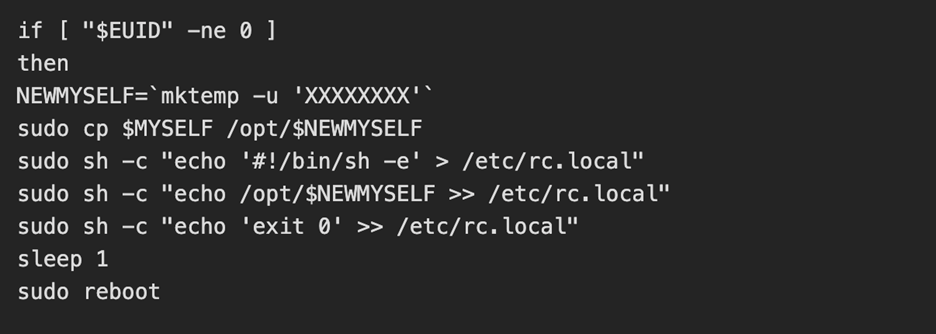
To verify authenticity, the worm used an embedded RSA key to validate signed commands a rare but notable security mechanism within the malicious code.
The infected device responded to “PING” commands from the C2 with “PONG,” confirming successful enrollment into the botnet.
Implications
Soon after joining the botnet, the malware installed two tools: zmap (a high-speed network scanner) and sshpass (for automated SSH logins).
Using these, it scanned 100,000 random IP addresses looking for open SSH ports. For each, the worm attempted two credential pairs:
- pi/raspberry.
- pi / raspberryraspberry993311.
Any vulnerable host found was infected in the same rapid sequence, allowing the worm to propagate autonomously across the Internet.
Though no cryptominer was installed, the script included functions to kill rival cryptomining processes, indicating that such payloads could be deployed on command later.
This attack underscores three critical lessons:
- Weak or default passwords still drive large-scale compromises.
- IoT and hobbyist devices, particularly Raspberry Pis, remain high-value botnet resources.
- Self-propagating worms can spread silently in seconds once a single host is breached.
Security teams and home users can mitigate these threats by:
- Disabling password authentication and enforcing SSH key-based logins.
- Removing the default pi user from Raspberry Pi devices.
- Enabling tools like fail2ban to block repeated SSH attempts.
- Segregating IoT systems from main production networks.
This captured attack demonstrates how unprotected Linux devices can be rapidly weaponized into global botnets. Even a single Raspberry Pi with default credentials can act as a launchpad for large-scale automated threats.
The lesson is simple yet urgent: never leave SSH exposed without strong authentication and hardening.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.






