SSRF Hacking With Yuvraj | Hacker2Hacker | SSRF

Source link
Related Articles
All Mix →Bug Bounty Response Efficiency| HackerOne Success Index
Quickly acknowledging, validating, and resolving submitted issues while recognizing the researcher’s effort is vital for successful vulnerability coordination. This fourth blog in our series on…
Detectify continues consolidating its authority in G2’s security categories
TL/DR. Detectify’s solution has been recognized by the G2 Fall Report 2022 as a Leader in the categories Website Security (ranking #1), Penetration Testing, and…
Lerhan: Bypassing IDOR protection with URL shorteners
Table of Contents Introduction What is URL shortening Jazztel shortened URL workflow When shortened URLs become an issue Passing it through Gobuster Data breakdown Doing…
My OpenAI Event Predictions (May 2024)
Table of Contents What I anticipate All about agents A personal DA A mix of agent stuff Summary I don’t have any insider knowledge—unless you…
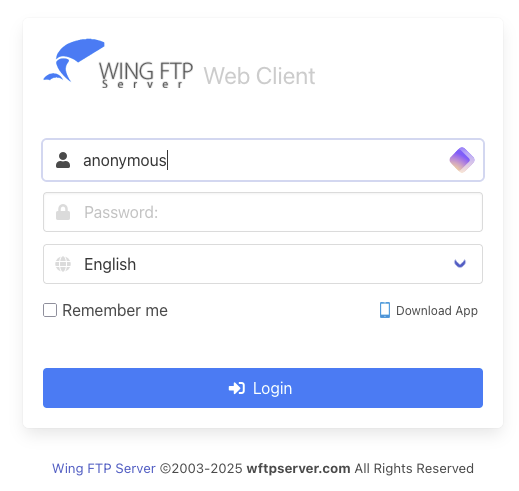
What the NULL?! Wing FTP Server RCE (CVE-2025-47812)
Table of Contents Good Old Anonymous! Strlen() vs NULL Why the heck is this interesting?!? Lua Code Injection into Session Files Triggering the Code Injection…
Leaking Session Tokens with CVE-2023-4966
Table of Contents Introduction Patch Diffing Finding the Vulnerable Function Exploiting the Endpoint Verifying the Session Token Final Thoughts Introduction It’s time for another round…