Downfall, a fan expansion for the popular Slay the Spire indie strategy game, was breached on Christmas Day to push Epsilon information stealer malware using the Steam update system.
As developer Michael Mayhem told BleepingComputer, the compromised package is the prepackaged standalone modified version of the original game and not a mod installed via Steam Workshop.
“One of our devices was hit with malware that did not get flagged or blocked by the security we had running on it. As far as I currently know, it was not a password-stealing malware as 2FA did not trigger or stop this, and of the accounts compromised, all were under different e-mail addresses (and none of those addresses themselves were stolen),” Mayhem told BleepingComputer, saying that he’s “reluctant to state anything with absolute certainty” until he obtains a professional assessment.
“This has led us to believe it was a token hijack instead (as suggested to us by a security professional), designed specifically to hijack Steam and use it to upload and Discord to prevent warning users, but that at the moment is just speculation.”
The attackers compromised one of Downfall’s developers’ Steam and Discord accounts, allowing them to gain control of the mod’s Steam account.
“The breach window was roughly 1:30 PM-2:30 PM Eastern (1830-1930 UTC+0) on 12/25. If you did launch Downfall on 12/25 during the breach window and got a Unity library installer popup, please continue to read. You may be also at risk. The security breach allowed a malicious upload to replace the Downfall packaged game,” Mayhem said in a statement published on Wednesday.
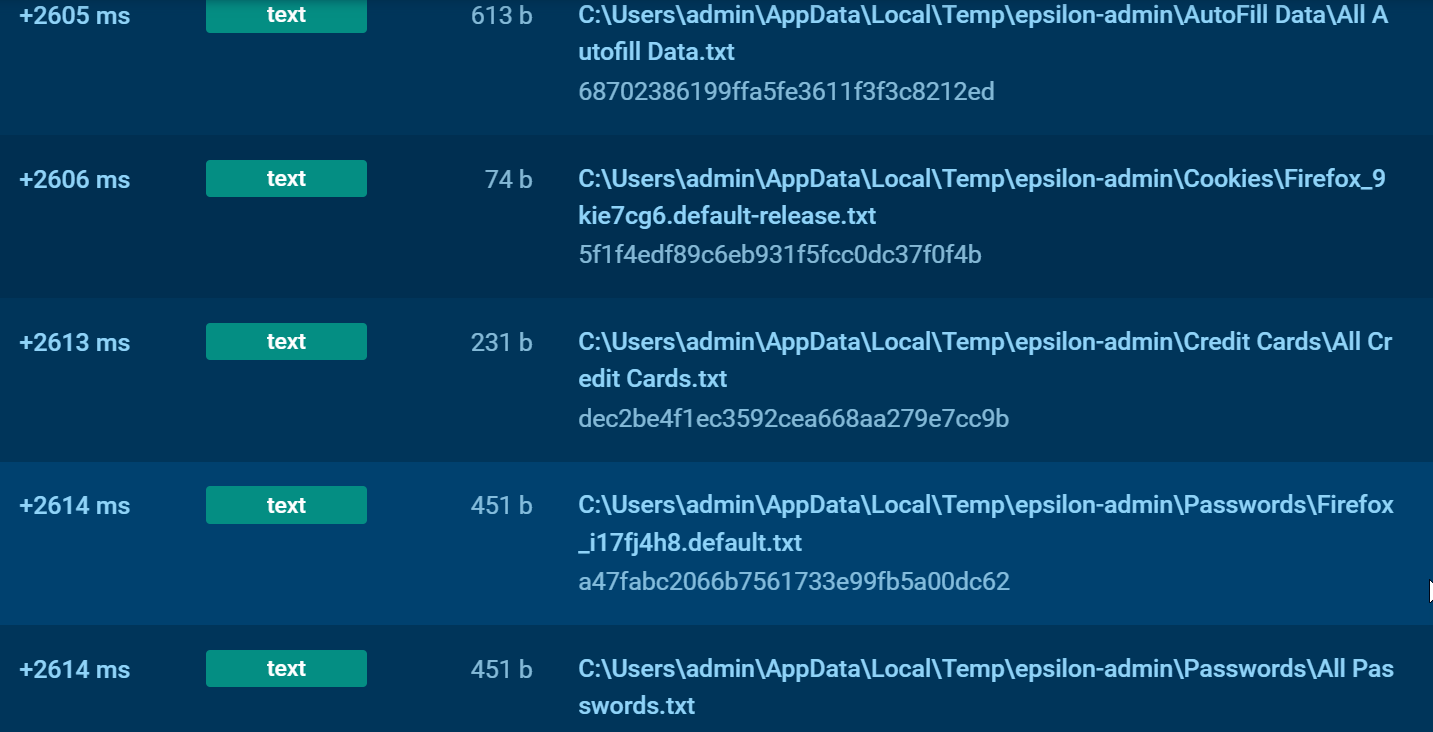
Once installed on a compromised computer, the malware will collect cookies and saved passwords and credit cards from web browsers (Google Chrome, Yandex, Microsoft Edge, Mozilla Firefox, Brave, Vivaldi), as well as Steam and Discord info.
It will also look for documents containing ‘password’ in the filenames and for more credentials, including the local Windows login and Telegram.
Downfall users are advised to change all important passwords, especially those for accounts not protected by 2FA (2-factor authentification).
Users who received the malicious update reported that the malware would install itself as a Windows Boot Manager application in the AppData folder or as UnityLibManager in the /AppData/Roaming folder.
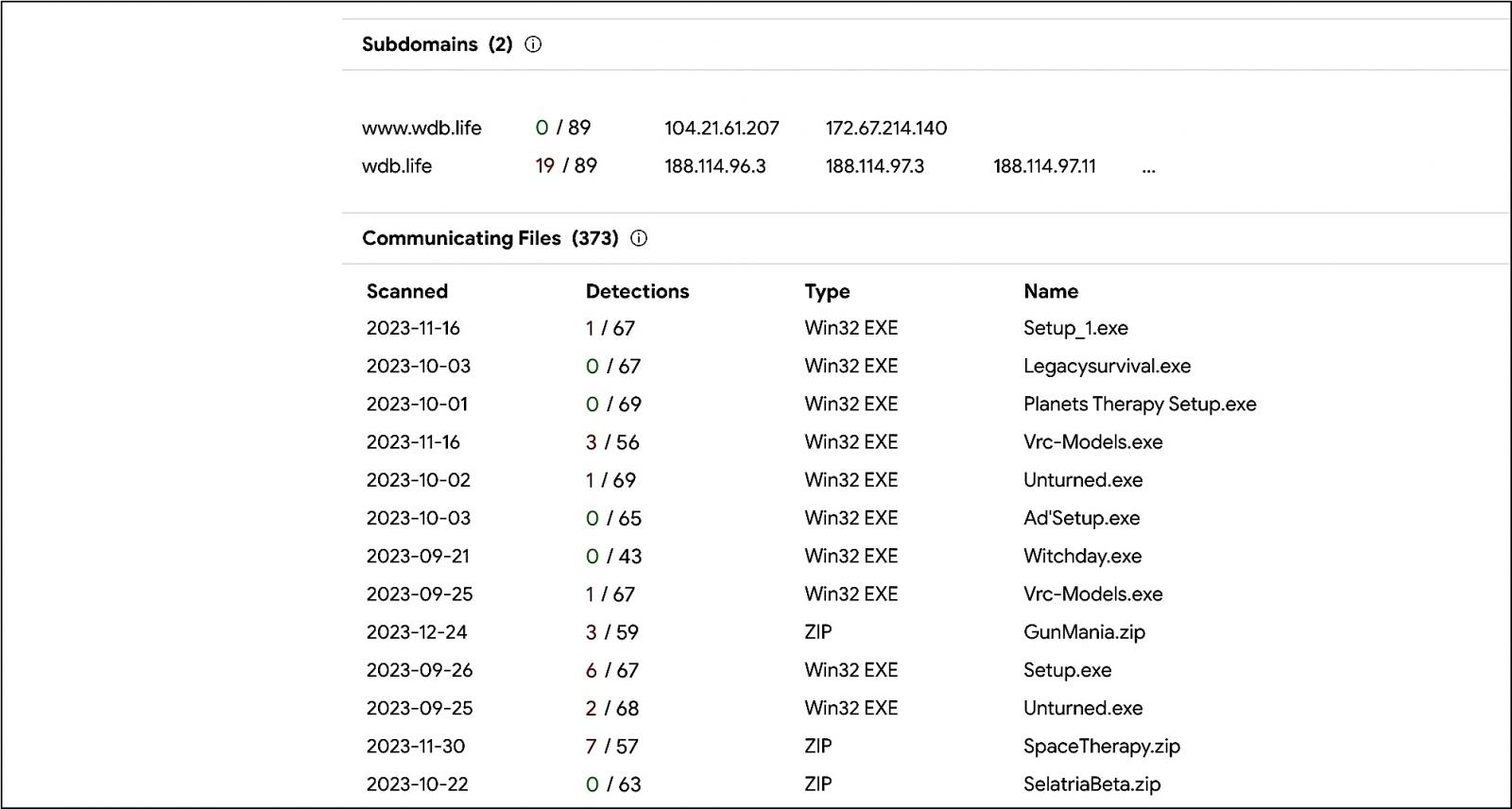
Epsilon Stealer is an information-stealing malware sold via Telegram and Discord to other threat actors. It is commonly used to target gamers on Discord by tricking them into installing the malware under the guise of testing a new game for bugs in exchange for payment.
However, after the game is installed, it also deploys the malware which runs in the background and steals the user’s passwords, credit card details, and authentication cookies.
The stolen information is either used by the threat actors to breach further accounts or sold on dark web marketplaces.
According to VirusTotal data, it’s likely that the threat actor behind this attack has also targeted other games and game developers.
Steam tightens security
In October, Valve announced that it now requires SMS-based security checks from game developers pushing an update on the default release branch on Steam.
The decision was taken in response to an increasing number of compromised Steamworks accounts being used to upload malicious game builds to infect players with malware starting in late August.
“As part of a security update, any Steamworks account setting builds live on the default/public branch of a released app will need to have a phone number associated with their account so that Steam can text you a confirmation code before continuing,” Valve said in October.
“The same will be true for any Steamworks account that needs to add new users. This change will go live on October 24, 2023, so be sure to add a phone number to your account now. We also plan on adding this requirement for other Steamworks actions in the future.”
Update 12/28/23: The email account of the developer was not breached.







