Hackers are abusing adversary-in-the-middle (AiTM) session hijacking to steal employee salaries in a new “payroll pirate” campaign tracked by Microsoft as Storm-2755 and targeting Canadian users.
By hijacking live Microsoft 365 sessions, the group redirects payroll deposits to attacker-controlled bank accounts while bypassing multifactor authentication (MFA) and blending in with normal user activity.
The group’s end goal is to modify payroll and HR records so that salaries are silently routed to accounts they control, causing direct financial losses for both workers and employers.
Instead of spear-phishing a specific sector, Storm-2755 relies on malvertising and SEO poisoning for broad, generic searches like “Office 365” or mistyped queries such as “Office 265.”
According to Microsoft Incident Response Detection and Response Team (DART), Storm-2755 is a financially motivated actor focused on Canadian employees rather than any single industry or organization.
These poisoned results push an attacker domain, bluegraintours[.]com, to the top of search results, luring victims into a fake Microsoft 365 sign-in page that closely mimics the legitimate portal.
AiTM sign‑in page and Axios hijack
When users enter their corporate credentials on the spoofed page, the attacker’s infrastructure proxies the real Microsoft 365 sign-in flow, stealing both passwords and session tokens in real time.
Logs from affected tenants show a 50199 sign‑in interrupt error just before Storm-2755 successfully takes over the account, followed by the same session ID continuing under a different user‑agent, Axios 1.7.9, indicating token replay rather than a normal login.
This pattern matches an AiTM attack, where the adversary sits between the user and the cloud service to capture session cookies and OAuth access tokens that represent a fully authenticated session.
Because these tokens are already validated, the attacker can reuse them to access Microsoft 365 services without re-entering credentials or passing traditional MFA challenges, effectively bypassing non–phishing-resistant MFA.
Storm-2755 then uses Axios 1.7.9 as an HTTP client to silently replay stolen tokens back into the victim’s environment, maintaining non‑interactive sign-ins to the OfficeHome application roughly every 30 minutes.
This periodic token replay preserves their access without prompting the user until defenders revoke active sessions, reset credentials, or enforce stricter token-lifetime policies.
In many cases, stolen tokens remain usable for around 30 days unless disrupted by expiration, rotation, or policy changes, during which the actor can sign in to Outlook, My Sign‑Ins, My Profile, and HR platforms.
For a subset of victims, Storm-2755 goes further by changing passwords and MFA settings to establish longer‑term persistence even after original tokens expire.
Mitigations
Once inside, Storm-2755 conducts targeted searches across intranet portals, SharePoint, and mailboxes for keywords like “payroll”, “HR”, “finance”, “account”, and “admin” to locate salary and HR workflows.
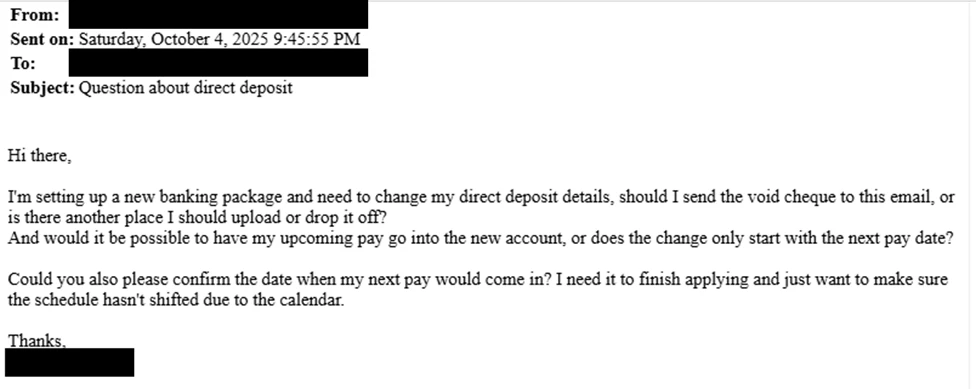
They also send emails with subjects such as “Question about direct deposit” to HR or finance teams, impersonating employees to request changes to bank details.
Where social engineering fails, the actor pivots directly into SaaS platforms like Workday using the hijacked session to update direct deposit information manually.
In one confirmed case, Storm-2755 successfully changed Workday banking details so that the victim’s paycheck was routed to an attacker-owned account, with the employee only realizing after missing a salary payment.
To hide their activity, the attackers create inbox rules that move emails containing “direct deposit” or “bank” into hidden folders such as Conversation History, preventing victims from seeing HR responses about account changes.
They also tend to refresh stolen sessions around 5:00 AM in the user’s time zone, reducing the chance that a legitimate login will invalidate their token replay.
Microsoft recommends immediate token revocation, removal of malicious inbox rules, and forced credential and MFA resets for impacted accounts, along with enforcing phishing‑resistant MFA such as FIDO2/WebAuthn.
Organizations are further urged to apply Conditional Access with adaptive session lifetimes and Continuous Access Evaluation, monitor for unusual user‑agents like Axios accessing OfficeHome, and alert on suspicious inbox rule creation as part of their broader zero‑trust and SIEM monitoring strategy.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.