New research from Varonis Threat Labs reveals Storm infostealer, a malicious subscription service that bypasses Google Chrome encryption. Learn how this tool uses server-side decryption and cookie theft to target crypto wallets and private accounts without triggering security alarms.
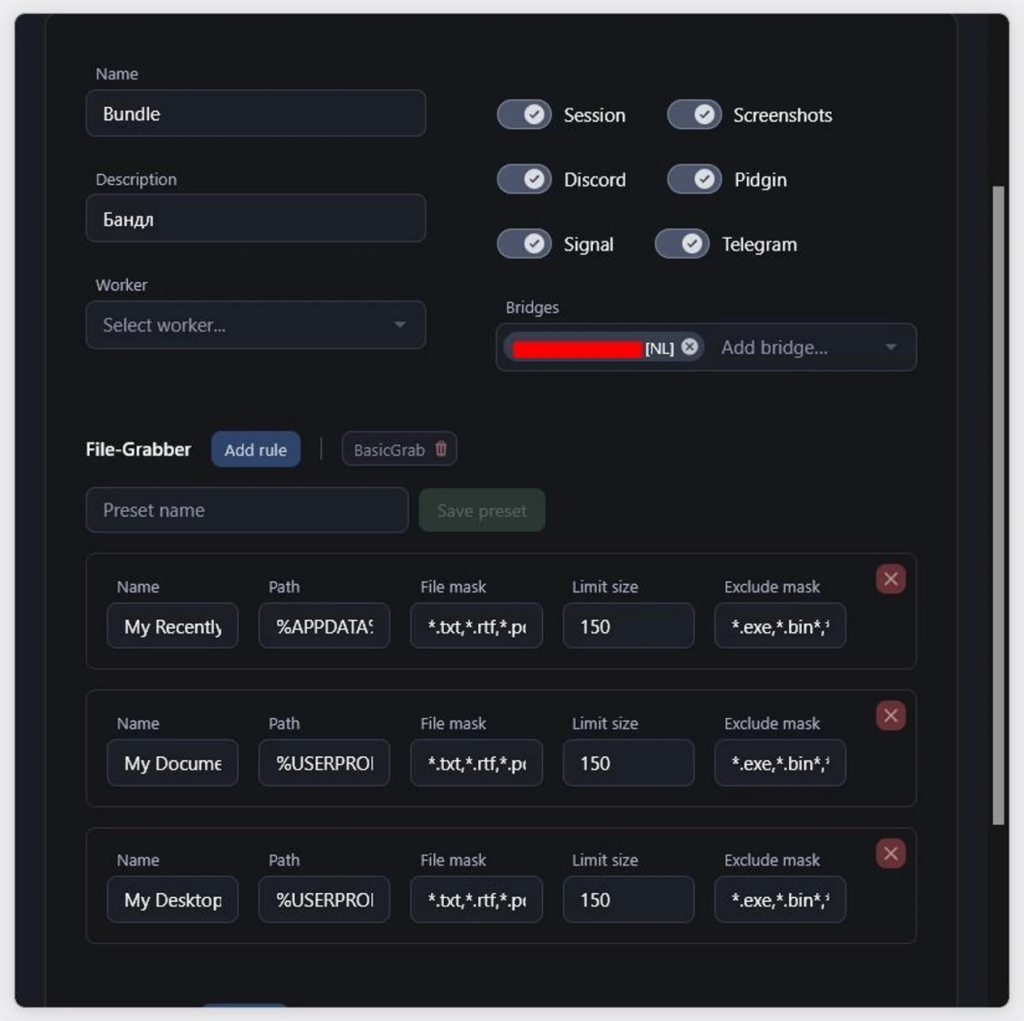
A new threat dubbed Storm infostealer is finding ways to break into our web browsers. Discovered by Varonis Threat Labs in early 2026, Storm is a malicious program that, upon infection, looks to harvest victims’ browser credentials, session cookies, crypto wallets, and related data, among other information.
Once the information is collected, it is then sent to a private server owned by the attackers. According to researchers, Storm infostealer uses a technique called server-side decryption for this purpose, which also makes it difficult for antivirus software to detect, since there is no telemetry data left.
This is a direct response to App-Bound Encryption, a security shield Google introduced in Chrome 127 back in July 2024. While that update was meant to tie encryption keys directly to the browser to prevent data theft, Storm infostealer has the ability to bypass this obstacle.
Additionally, besides Google Chrome, it can also extract data from other Chromium-based browsers and Gecko-based browsers, including Microsoft Edge, Firefox, and Waterfox.
As Varonis researchers noted, the tool has a very broad range of target browsers. No wonder it has been “productised and sold as a subscription feature,” with prices starting at $300 for a seven-day demo and climbing to $1,800 for professional criminal teams.
What’s worse, since Storm infostealer can hijack sessions, for your information, if a hacker has your session cookie, your Multi-Factor Authentication (MFA) becomes completely irrelevant because they are already “in.” Varonis found that the tool is already being used in the wild, with a logs panel showing 1,715 entries from victims in the following countries:
- India
- Brazil
- United States
- United Kingdom
However, the threat doesn’t end there. Storm Infostealer also targets Telegram, Signal, and Discord accounts, while simultaneously hunting for crypto wallets on platforms like Binance and Coinbase. It can even take screenshots across multiple monitors to see exactly what you’re working on.
To protect your devices and data from Storm infostealers, users should know that hackers rely on their sessions staying active for long periods; therefore, manually logging out of sensitive banking or crypto accounts when you are finished is important, rather than just closing the tab. As Varonis threat experts warn in the report, these stolen sessions are usually just “the start of what comes next,” leading to total account takeovers that ignore even the strongest passwords.