The term Agentic SOC (Security Operations Center) is one of the most popular concepts in security today. But what does it truly mean in practice, and how does Elastic Security approach this next evolution of security operations?
In simple terms, an Agentic SOC is a security operations center that has deployed AI Agents and corresponding AI Agent Skills to perform SOC-related workflows such as detection engineering, alert triage, incident investigation, escalation, response, and threat hunting. When these workflows are performed by AI agents, they’re often called “Agentic workflows.” These AI Agents and Skills may run natively in a security operations platform like SIEM, XDR, or security analytics, or they may be layered on top of legacy SIEM as an “AI SOC Agent” or “AI SOC analyst”, or they may even be run from an AI Coding Tool.
Regardless of how they are implemented, the shift to the Agentic SOC is not about AI replacing human analysts; it’s about transforming how the SOC functions. To keep pace with rapidly evolving attackers, defenders must leverage AI and autonomous agents to respond as quickly as possible. At its core, an Agentic SOC is defined by how a security operations center uses AI and agents to protect against adversaries.
Let’s simplify a successful security operations center to three fundamental pillars, all of which the Agentic SOC significantly enhances:
- Observe: The foundation of all security is centralized data—aggregating logs and events into one location, which is the core strength of a SIEM solution.
- Detect: This involves deploying core protections like endpoint-based security (XDR, such as Elastic Defend) and security solution-focused detections (cloud, identity data). This technology drives the generation of high-quality alerts. Elastic, for example, ships over 1,700 pre-built rules for its SIEM by default, not including its XDR solution’s endpoint rule library.
- Act: This is the critical final stage of triaging, investigating, and acting on the generated alerts.
Agentic SOC in Action
Imagine this real-life scenario unfolding in your Security Operations Center using the Elastic security platform. It begins not with a siren, but with a simple, direct Slack notification. Building on our recent blog on Attack Discovery, Workflows, and Agent Builder, let’s further examine how Elastic Security can help you respond to an active attack.
- The Initial Alert and Immediate Action
Your security analyst receives an urgent notification in their team channel. This message isn’t just a heads-up; it points directly to an observed, active attack. Crucially, the Elastic Agentic SOC has already taken decisive, pre-emptive action: a vulnerable host has been isolated from the network to contain the threat and limit potential damage. This was all powered by Elastic Workflows and Elastic Agent Builder processing realtime alert and attack data from Elastic. - The Centralized Case
The analyst’s next step is a click away, moving from Slack directly to the centralized Case within Elastic that was created by the workflow. Elastic Case Management enables the SOC to coordinate the response and provides a single pane of glass into all aggregated critical information:
Attack Summary: A high-level overview detailing what has occurred using Attack Discovery.
Attached Alerts: The specific security alerts that triggered the initial observation.
Observables: A list of suspicious artifacts (IP addresses, file hashes, domains, etc.) collected from the event.
Attached Events: Non-alert events that, while not an alert themselves, provide critical context and are of further interest to the investigation.
- Supporting the Investigation
To support the immediate findings, detailed Investigations are attached directly to the Case. These searches allow the analyst to visually and contextually step through the sequence of events leading up to, during, and immediately following the attack.
The Elastic Case also provides instant context by highlighting Similar cases. By cross-referencing observables, the system identifies previous incidents involving the same entities or artifacts, providing a deeper understanding of the threat actor’s history and potential motives. - The Path to Resolution
The agents don’t just catalog the past; it dictates the future. A clear set of Next steps and actions are outlined, with specific team members assigned for review and execution.
The analyst then steps through a methodical process reviewing the automated analysis:
- Reviewing Findings: Scrutinizing all aggregated data, alerts, and investigations.
- Evidence Collection: Collecting any additional forensic evidence needed for a complete analysis.
- Remediation: Executing manual or automated actions, such as deleting malicious files or killing persistent processes on the isolated host with Elastic Defend.
- Final Release: Eventually, the host is safely released back to the network, but not before additional, targeted rules or policies are automatically applied to prevent a recurrence based on the lessons learned from this incident.
In the Agentic SOC, the analyst moves seamlessly from a high-level alert to a comprehensive investigation to full remediation—all within a unified, intelligent workflow powered by Elastic.
Elastic Security and Core SIEM Workflows
Before exploring advanced agentic workflows, it’s essential to recognize that Elastic Security already provides a comprehensive suite of core capabilities crucial for modern security operations. This foundation begins with the ingestion of security-relevant data, which is automatically normalized to a common schema, ensuring consistency and ease of analysis. The platform offers Extended Detection and Response (XDR) capabilities via Elastic Defend, a robust detection engine built directly into the Elastic Stack, and sophisticated alert workflows that include built-in correlations to reduce noise and surface true threats.
Elastic Security further differentiates itself by tightly integrating key operational functions. This includes entity-based threat hunting, machine learning for anomaly detection and behavior analysis, and comprehensive case management for tracking incidents. Finally, the platform provides end-to-end response and forensic capabilities, enabling security teams to move swiftly from initial alert to investigation and remediation, all within a unified, scalable platform.
Empowering Analysts with Agentic Capabilities
AI-Powered Alert Triage and Prioritization
The Elastic Security Solution integrates AI capabilities via Agent Builder to augment and make SOC operations truly agentic. This is where efficiency improvements are most keenly felt:
- Conversational Triage: A built-in agent is readily available to Tier 1/2 analysts, allowing them to use conversational commands to query and prioritize open alerts (e.g., “What priority alerts should I review from the last 30 days?”). This is the first entry point for using AI to augment SOC operations.
- LLM Agnostic Platform: A key differentiating feature of Elastic’s Agent Builder is that it is LLM agnostic, allowing organizations to pick their preferred model, even locally running models for privacy or regulatory reasons.
- Attack Discovery: This premier feature moves beyond basic triage. It uses LLM configurations to create higher-order attack detections, taking hundreds of open alerts and prioritizing them into a small, manageable subset of known attacks or incidents. This dramatically reduces the impact of alert fatigue.
Enriched Investigations
Once an attack or incident is found, the agent helps start the investigation:
- Summarization and Enrichment: The agent can be used to summarize the attack, identify important artifacts, and conduct automated third-party enrichments (like checking VirusTotal). This tailored experience provides a full assessment, including an attack chain, threat intelligence information, related cases, entity risk scoring, and a full investigation guide.
- Case Management: The agent can be instructed to take immediate action, such as generating a security case and notifying the team in Slack, all through simple conversational commands that execute pre-configured workflows.
Automated Response and Threat Hunting
The true power of the Agentic SOC is realized through action and automation that goes beyond simple conversation:
Workflows and SOAR-like Automation: Agents can reference and execute Workflows, Elastic’s SOAR-like automation tool. These workflows allow analysts to take immediate, complex actions. For example, a command like “Please create a case for this attack, and notify my team in Slack” triggers multiple, pre-defined steps. Further critical response actions, such as isolating a host, can be executed with a single workflow action while the investigation continues.
AI-Assisted Threat Hunting: AI assists threat hunters by leveraging Entity Analytics and pre-built skills. The agent can be asked to find high-risk hosts and users to begin hunting, and then automatically generate specific ESQL queries (e.g., “Please tell me the most uncommon processes executed for each host”) to uncover unusual or malicious activity.
The Mandate of Automation
For maximum effectiveness, all these steps,from alert triage and enrichment to case creation and host isolation,can be configured to run automatically as an Agentic Alert Triage workflow. This allows the system to solve problems as soon as they are discovered, setting up the human analyst in the loop with a consolidated case and all the necessary findings in a single pane of glass.
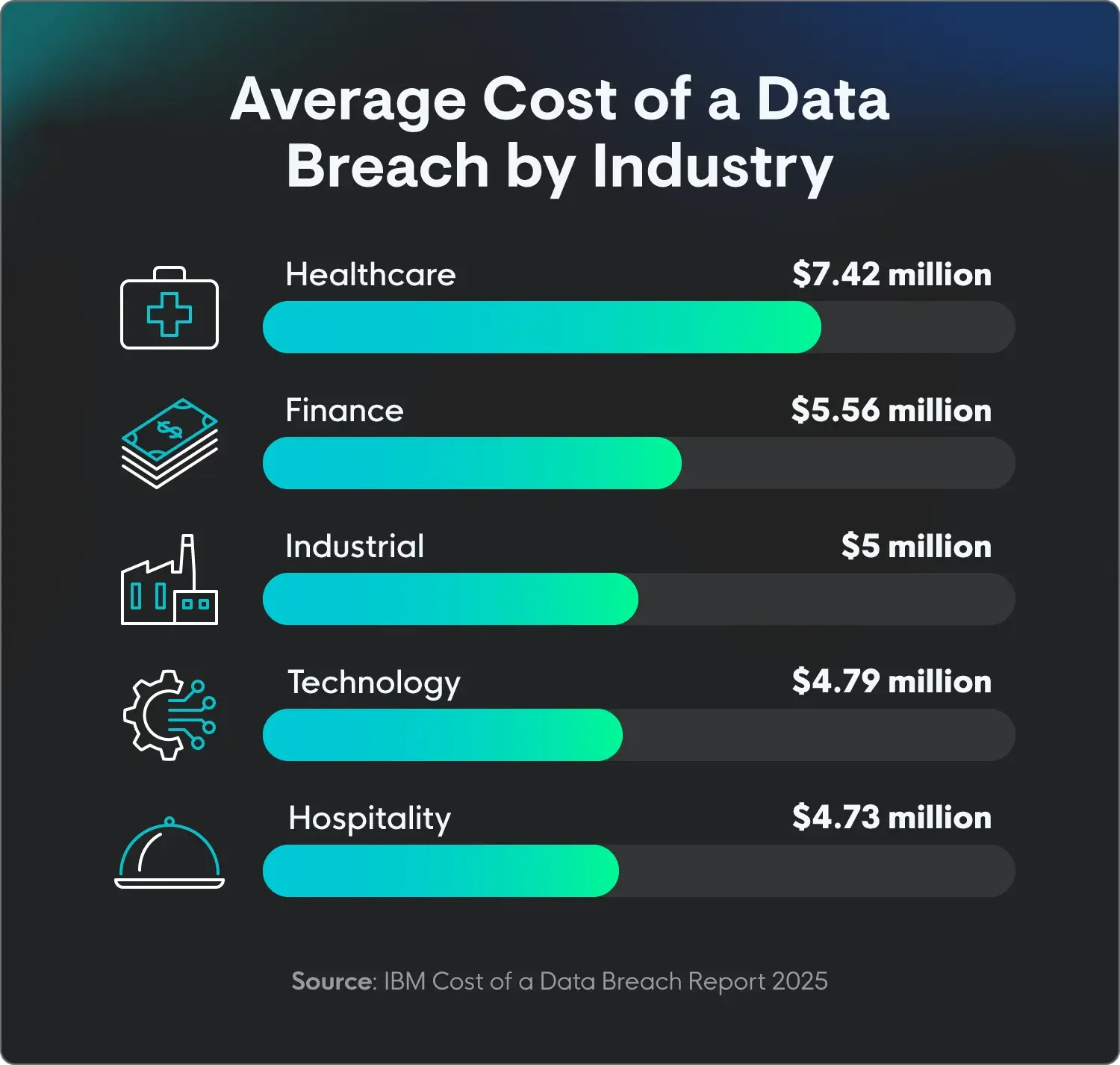
This approach delivers substantial efficiency improvements, making speed the single most important factor in a modern, Agentic SOC.
Elastic’s Agentic Security Operations Platform
Whether you use our UI, our agents, or your own, Elastic Security provides a strong open foundation for modern security operations. best-in-class data architecture, search, workflows, analytics, detection engineering content, and automation.
Getting started
Before you get started: AI coding agents operate with real credentials, real shell access, and often the full permissions of the user running them. When those agents are pointed at security workflows, the stakes are higher: you’re handing an automated system access to detection logic, response actions, and sensitive telemetry. Every organization’s risk profile is different. Before enabling AI-driven security workflows, evaluate what data the agent can access, what actions it can take, and what happens if it behaves unexpectedly
Don’t have an Elasticsearch cluster yet? Start an Elastic Cloud free trial. It takes about a minute to get a fully configured environment.