The Different Types Of Bug Bounty Hunters

Source link
Related Articles
All Mix →The Primary Law of Intelligent Immigration Policy
First, answer two questions: What is our country? What defines it? What parts could not be removed without it becoming something different? If a country…
Your First 90 Days as Security Lead, Part 1: Building Your Security Foundation
Congratulations! You’ve just been named the new security lead for your organization. You probably have many projects swirling through your mind, like addressing a critical…
What Operating System do I need to hack?
What Operating System do I need to hack? Source link
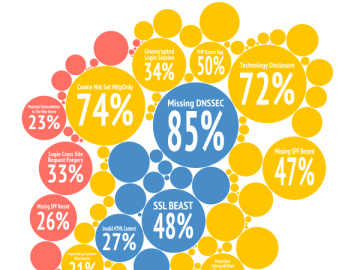
First encounters through the eyes of the Detectify scanner
What do typical websites look like through the eyes of our vulnerability scanner the first time they are tested? How does that picture change over time?…
How to Lower Your Heart Rate Before Public Speaking
There are two kinds of stress associated with public speaking. I have one, but not the other. The first one is really bad and it’s…
The iPhone 5 Doesn’t Need to be Revolutionary
This video is an entertaining look at the hype and reality leading up to today’s iPhone 5 release. I think they get a lot right,…