The Different Types Of Bug Bounty Hunters

Source link
Related Articles
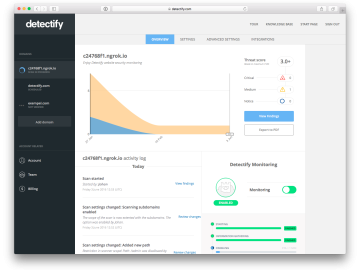
All Mix →[Release] New scan profile overview allows you to see progress over time
Our brand new scan profile overview is finally here! For a long time, we have preached continuous security, encouraging our users to schedule recurring tests…
How to use AI for improved vulnerability report writing
Report writing is an integral part of bug bounty or any type of vulnerability assessment. In fact, sometimes, it can become the most important phase.…
Quicksilver + Quicksearches = Ultimate Power
I’m often asked why I think so much of Quicksilver, and why it’s always part of my pitch when I’m trying to get someone to…
My Mom Died on Saturday
Created/Updated: September 21, 2022 My mom died on Saturday. My biological mother became unable to function when I was around five due to mental illness,…
What Operating System do I need to hack?
What Operating System do I need to hack? Source link
My Current Thoughts on Gun Control
Like many others, I’ve been in a number of debates about gun control in recent weeks. Here are my main thoughts on the topic: The…