Theft of Arbitrary files from LocalStorage | Hacking on Android With Gaurang | #InsecureShop – 02

Source link
Related Articles
All Mix →Mike Wilkes on Resilience Amid Evolving Threats
Table of Contents From Philosophy to Firewalls A CISO Career Path Spanning Sectors The Two Types of CISOs and the Real Skills CISOs Need Today…
Bug Bounty and Other Inclusive Communities
Table of Contents Obsidian rwxrob Enjoy my content? Hive Five newsletter Don't bee a stranger In these strange times it’s important that we come together.…
More improvements to Attack Surface Custom Policies
Table of Contents Tl;dr We’ve made a few improvements to Attack Surface Custom Policies, such as viewing alerts more easily and deleting custom policies. We’ve…
Broken Access Control – Lab#12 Multi-step process with no access control on one step | Short Version
Broken Access Control – Lab#12 Multi-step process with no access control on one step | Short Version Source link
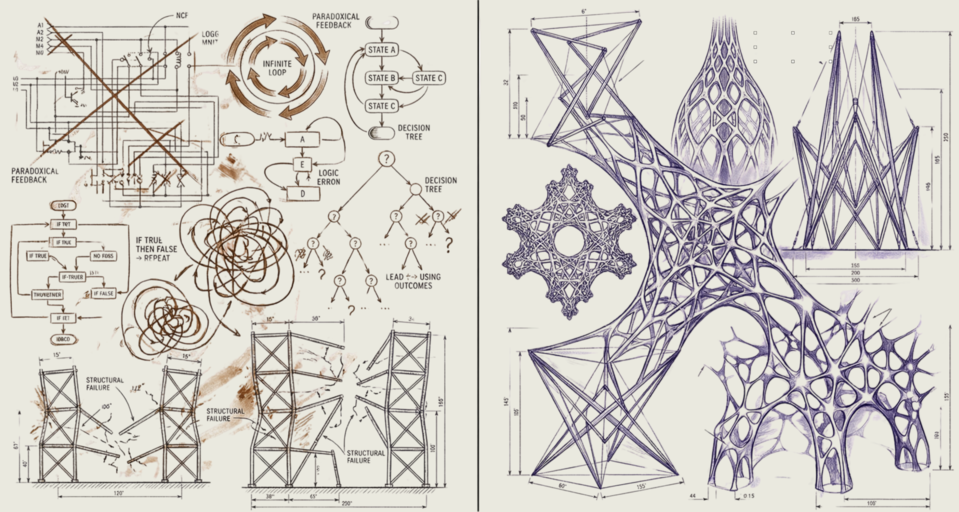
Bitter Lesson Engineering | Daniel Miessler
Table of Contents This is about more than just agentic engineering LIFE MANAGEMENT BUSINESS GENERAL AI INTERACTION My takeaways I have a new concept I’m…
What Is a Business Logic Vulnerability? [Example]
Table of Contents What Is a Business Logic Vulnerability? What Is the Business Impact of Business Logic Vulnerabilities? What Industries Are Impacted By Business Logic…