They are all Injection Vulnerabilities! – Security Simplified

Source link
Related Articles
All Mix →Optimizing text for ChatGPT: NLP and text pre-processing techniques
Table of Contents Text preprocessing Tokenization and ChatGPT input limits A general programmatic approach Byte-Pair Encoding (BPE) Sending lots of text to ChatGPT In order…
The Logical Solution to the Civil Union vs. Marriage Debate
The answer is so simple that it may temporarily disorient you. Civil unions are a government function Marriage is a church function In other words,…
Newly added security tests April 5, 2017: Joomla and WordPress vulnerabilities
To bring you the most up-to-date security service and help you stay on top of threats, we update Detectify on a regular basis. Here are…
Vulnerability Disclosure is Now Mandatory for Federal Agencies – Here’s How to Make it Happen
Federal agencies exist to protect and support the nation and its citizens. Despite their elaborate processes to reduce cyber risk, many American agencies lack modern…
how I bruteforced my way into your Active Directory – honoki
Table of Contents The Target The Setup The Bugs The Exploit The Outcome Timeline Last May, I discovered that a critical vulnerability I had reported…
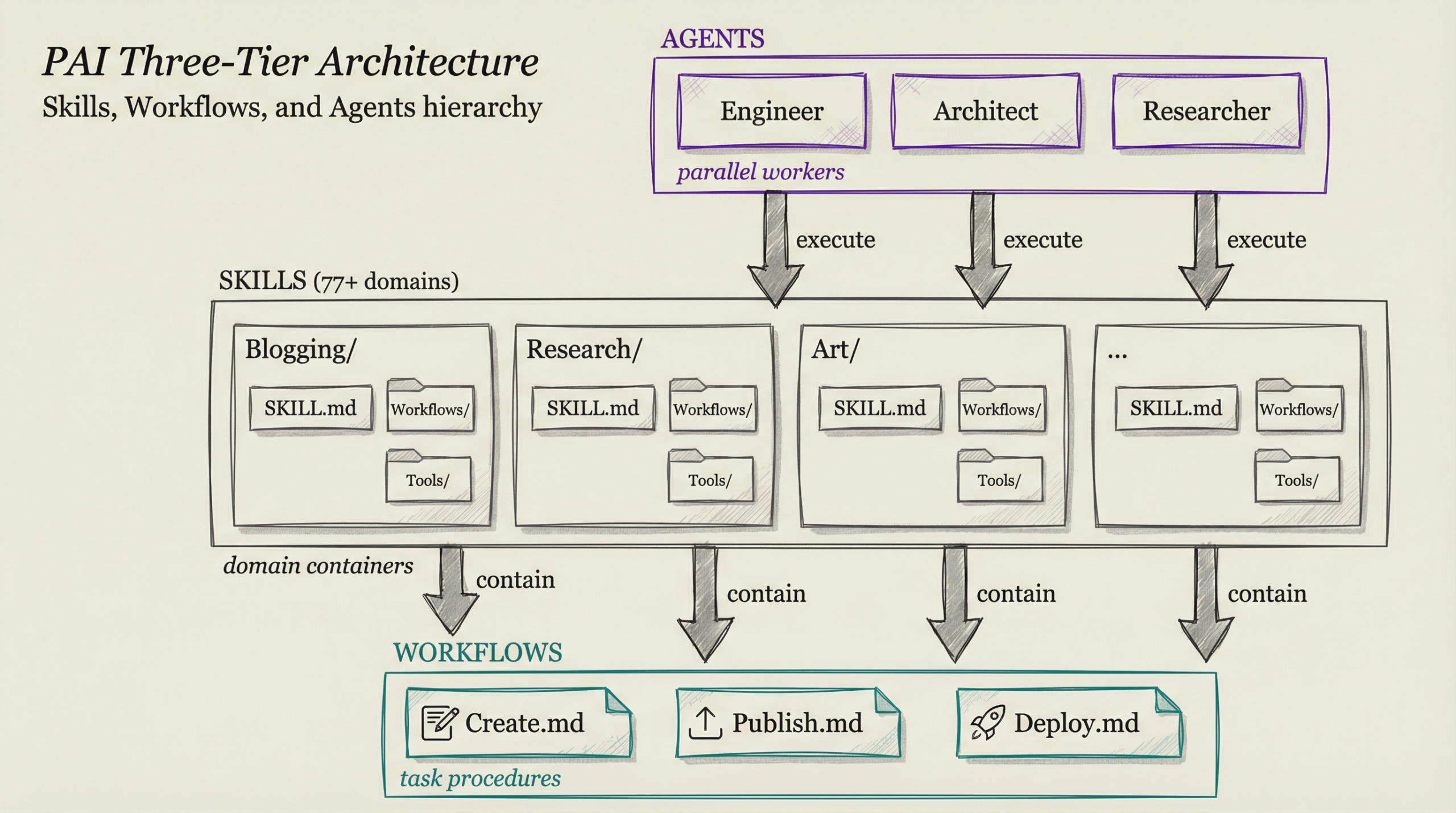
When to Use Claude Code Skills vs Workflows vs Agents
Table of Contents The Quick Answer The Hierarchy Skill Structure Skill Anatomy: SKILL.md The Three Tiers Explained Tier 1: Skills (Domain Containers) Tier 2: Workflows…