Slides Supplemental Demo Video:

Source link
Related Articles
All Mix →Cyber Regulations Can Make Our Nation Safer
While a largely voluntary approach to critical infrastructure cybersecurity has led to some improvements, a general lack of mandatory requirements has too often resulted in…
Elixir Cheatsheet
1 min read 💎 Cullinan :: Develop Elixir Cheatsheet HAHWUL in cullinan Source link
HACK HARD. HAVE FUN. INCREASE SECURITY
Amazon’s Live Hacking Event with HackerOne At Amazon, ensuring security is essential for earning customers’ trust. As part of Amazon’s ongoing public Vulnerability Research Program (VRP),…
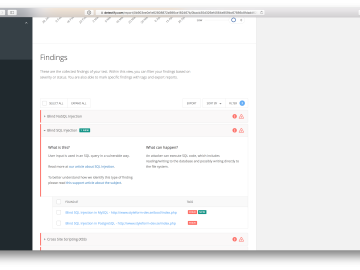
5 things we’ve done to make your Detectify experience better
Table of Contents 1) More transparency on what tests we have performed 2) Manual findings export to JIRA 3) See what findings are new 4)…
Pentesting for iOS Mobile Applications
Table of Contents iOS Testing Methodologies Common iOS Vulnerabilities Improper Credential Usage Insecure Authentication or Authorization Inadequate Privacy Controls iOS Best Practices Careful Scoping Skills-Based…
Automating your reconnaissance workflow with ‘meg’
Table of Contents The Basics Discovering Interesting Files On The Web Live Preview Time To Experiment For the past few months, I have been playing…