Slides Supplemental Demo Video:

Source link
Related Articles
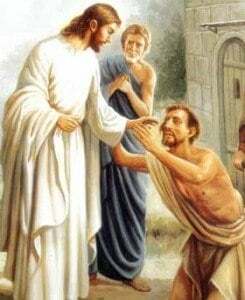
All Mix →The Jesus Quote You’ll Never Hear in Church
Christians love to rail against hateful language in the Koran, saying that the extremist teachings there can be used to justify violence. Well, it’s in…
Unsupervised Learning NO. 392 | Daniel Miessler
Unsupervised Learning is a Security, AI, and Meaning-focused podcast that looks at how best to thrive as humans in a post-AI world. It combines original…
AT&T Celebrates $1 Million Awarded to Hackers in One Year
AT&T Communications recently celebrated its first anniversary on HackerOne, passing $1 million in payouts to more than 850 researchers worldwide. The HackerOne program is a…
How to Tell if Someone is a True Libertarian
In short, if they’re against these things on moral grounds, and, importantly, want them to be illegal–they are outright fakes. The giveaway isn’t that they…
How to set up a fresh Ubuntu desktop using only dotfiles and bash scripts
Configure settings, install programs, and customize your desktop environment with a single bash command. One of my most favorite things about open source files on…