Threat actors recently abused a critical Apache ActiveMQ vulnerability to gain deep access to a Windows environment, eventually deploying LockBit ransomware over RDP.
The attack shows how failing to patch CVE-2023-46604 can give adversaries repeat access and time to turn an initial foothold into full-domain impact.
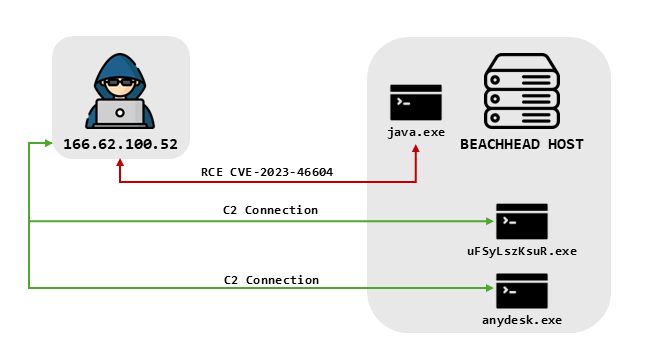
The exploit loaded a malicious Java Spring bean configuration XML file, which instructed the server to use CertUtil to download a payload from a remote host.
The downloaded file was a Metasploit stager that connected back to the attacker’s command-and-control (C2) infrastructure, turning the ActiveMQ host into their beachhead.
In mid-February 2024, the attacker exploited CVE-2023-46604 on an internet-facing Apache ActiveMQ server, leveraging the Java OpenWire protocol vulnerability to achieve remote code execution.
Roughly 40 minutes after the initial exploit, the threat actor began post-exploitation activities through Metasploit, likely using Meterpreter.
Apache ActiveMQ Vulnerability
They ran GetSystem to escalate privileges to SYSTEM, then accessed the LSASS process memory to dump credentials from the beachhead server.
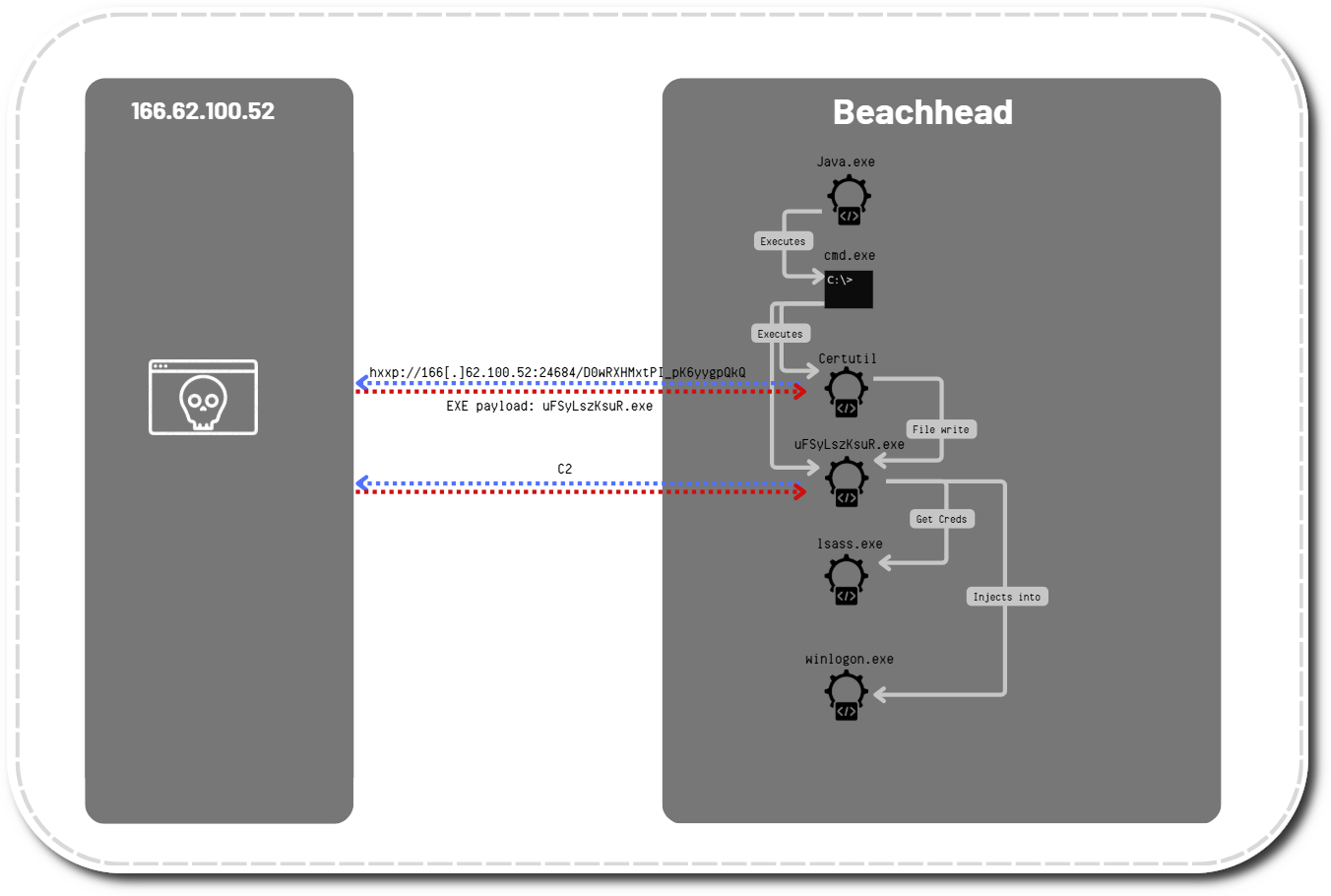
Sysmon event ID 1 showed the execution, with Java – the ActiveMQ server process – listed as the parent process.
Within the next 20 minutes, a spike in SMB traffic indicated network scanning, followed by lateral movement using a domain administrator account to execute Metasploit payloads as remote services on multiple hosts.
On several of these systems, LSASS memory was accessed again, and one server hosted a privileged service account tied to a line-of-business application, which later became crucial to the second-stage intrusion.
During this first phase, the attackers also deployed AnyDesk for persistence and defense evasion, installing it as an AutoStart service and enabling RDP through firewall and registry changes via an rdp.bat script.
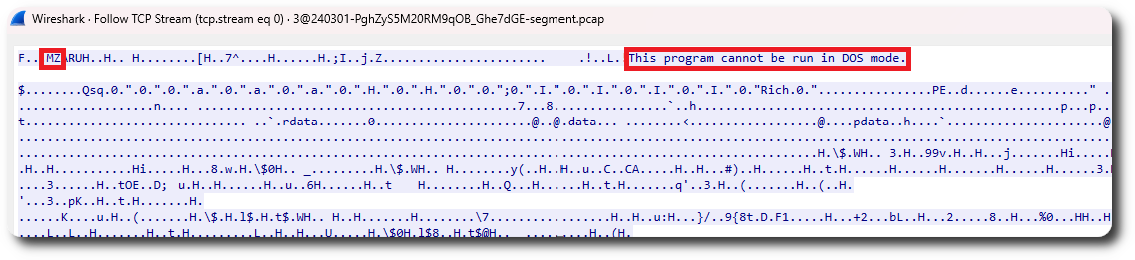
Reviewing the network traffic, we also saw the download of an executable file with the typical MZ header and the “This program cannot be run in DOS mode” string.
They cleared Windows System, Application, and Security event logs to hinder incident response, while active antivirus on some systems successfully blocked a subset of their Metasploit-based lateral movement.
On the second day, the attacker performed additional discovery with standard Windows utilities, albeit with syntax errors that suggested either unfamiliarity with Windows or a faulty playbook, before ultimately losing access to the environment.
Eighteen days later, the same threat actor returned, exploiting Apache ActiveMQ server again using the same CVE-2023-46604 attack path and C2 infrastructure.
Mitigations
After repeating the GetSystem privilege escalation and LSASS credential theft on the beachhead, they quickly confirmed domain admin group membership and pivoted laterally using the previously harvested privileged service account.
They then used RDP to access key systems such as backup and file servers, ensuring RDP was enabled and dropping AnyDesk, network scanning tools, and two LockBit payloads (LB3_pass.exe and LB3.exe) staged under C:Intel and user Downloads directories.
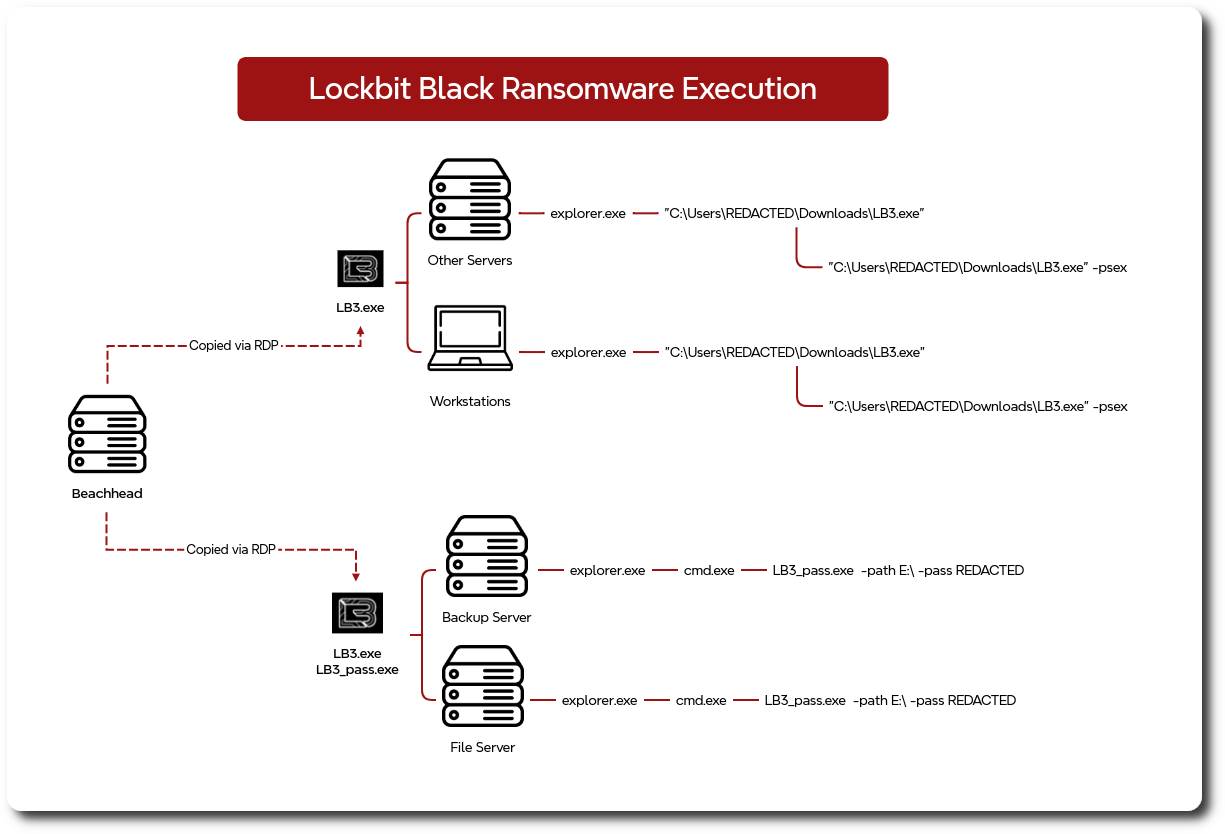
From there, the attacker executed LockBit ransomware interactively over RDP sessions across the environment for roughly four hours, using specific path and password flags on critical servers and leveraging a PsExec-style spreader option on others.
The ransomware binaries matched LockBit signatures but appeared to be generated with the leaked LockBit Black builder, as the ransom note diverged from standard LockBit guidance and instead instructed victims to communicate solely via the Session private messaging application rather than official LockBit infrastructure.
Overall time to ransomware was about 419 hours (19 days) from initial access, but once the actor re-entered the network on day 18, defenders had less than 90 minutes before widespread encryption began.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.