TomNomNom Demos a Ben Eater 8-bit CPU Emulator

Source link
Related Articles
All Mix →Jesus’ Death Was Not a Sacrifice
There’s one question I’ve never heard asked as part of an inquiry into Christianity: Why was Jesus’ so-called “sacrifice” considered to be so significant? Let’s…
Double your signal, double your fun
Table of Contents Introducing Human-Augmented Signal Ensuring smooth public launches What should I do? Noise from invalid or low-impact reports makes it difficult for customers…
facts: Bug Bounty hunters has made ridiculous amounts of $$ from known DNS techniques..
facts: Bug Bounty hunters has made ridiculous amounts of $$ from known DNS techniques.. Source link
Add A “Reddit this” Option To Your Feedburner RSS Feed (FeedFlare)
I’ve just completed a “Reddit this” FeedFlare module for Feedburner users. This will add the option for your RSS users to submit your posts to…
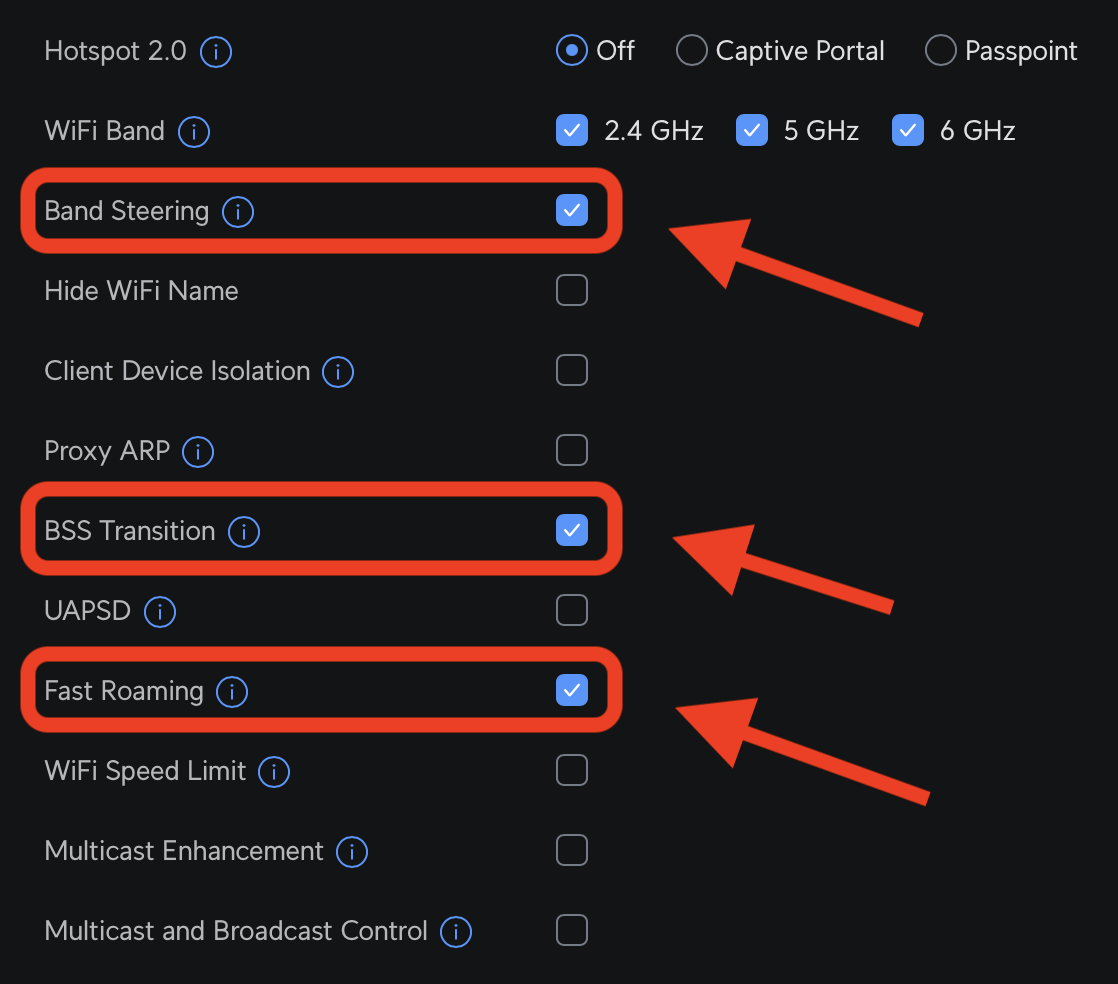
Fixing Ubiquiti WiFi Roaming | Daniel Miessler
The three settings I had to enable to get proper WiFi roaming The problem I’m a massive fan of Ubiquiti stuff, but even after upgrading…
A Warm Welcome To Our New SVP of Customer Success
Table of Contents Why I Joined HackerOne Making HackerOne Core to the CISO Playbook Building a World-Class Team of Leaders First Things First Hello HackerOne…