TOOL TIME: Stream #4

Source link
Related Articles
All Mix →Detectify security updates for 10 January
For continuous coverage, we push out major Detectify security updates every two weeks, keeping our tool up-to-date with new findings, features and improvements sourced from…
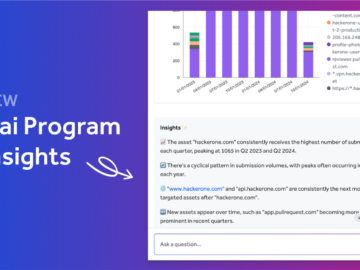
Hai’s Latest Evolution: Intelligence, Context, and More Intuitive UX
Table of Contents Transforming Security Program Management: A Day with Hai 1. Hai Program Insights: Instantly Understand Your Programs 2. Contextual Conversation When It Matters…
Defense for Vulnerable React Server Component Workflows — API Security
Table of Contents What is CVE-2025-55182? What is CVE-2025-66478? What is the Impact? How Does Wallarm Protect Against These Vulnerabilities? Recommended Remediation Conclusion On December…
100 Conversations with Start-up Security Leaders
Table of Contents Why are run-of-the-mill, traditional pentests not delivering effective results? As my business undergoes digital transformation, how can continuous application security testing help…
Self-Contained Scripts: From Python’s UV to Bun’s TypeScript Revolution
Table of Contents The Self-Contained Script Revolution From Python UV to Bun: A Natural Evolution Real-World Self-Contained Scripts: Claude Code Hooks Example 1: Command Logger…
A complete guide to exploiting open URL redirect vulnerabilities
Table of Contents Server-side redirects Client-side redirects Simple open URL redirects Advanced open URL redirects DOM-based cross-site scripting (XSS) GET-based cross-site request forgeries Account takeover…