Top 3 Most Dangerous Lines of Code

Source link
Related Articles
All Mix →Bugcrowd Security Flash – The Kaseya REvil Attack Explained
Bugcrowd Security Flash – The Kaseya REvil Attack Explained Source link
The relentless rise of atmospheric CO2 since 1950
Table of Contents The numbers tell a stark story Why Mauna Loa matters The pre-industrial baseline What drives the acceleration? The path forward The Keeling…
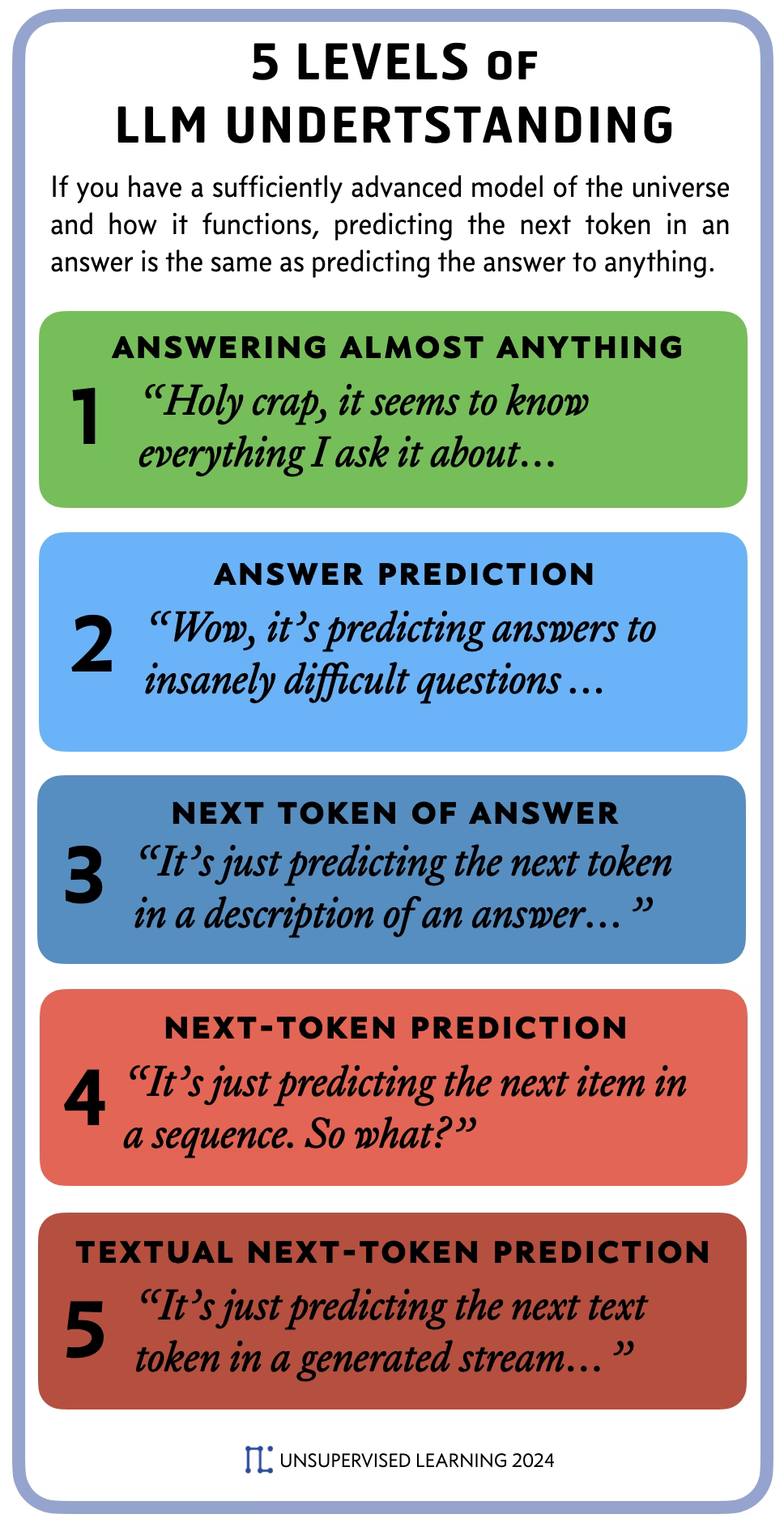
World Model + Next Token Prediction = Answer Prediction
Table of Contents Table of Contents A new way to explain LLM-based AI The 5 Levels of LLM Understanding Answers as descriptions of the world…
Observations of Japan | Daniel Miessler
I had the opportunity to go to Tokyo, Japan for a week this month for work and while there I kept a running list of…
Women in sales brings unique strengths and perspectives to the table
Table of Contents Networking and Mentorship Diverse Perspectives for Better Results Overcoming Challenges Challenging the Status Quo Earlier this year, I was part of a…
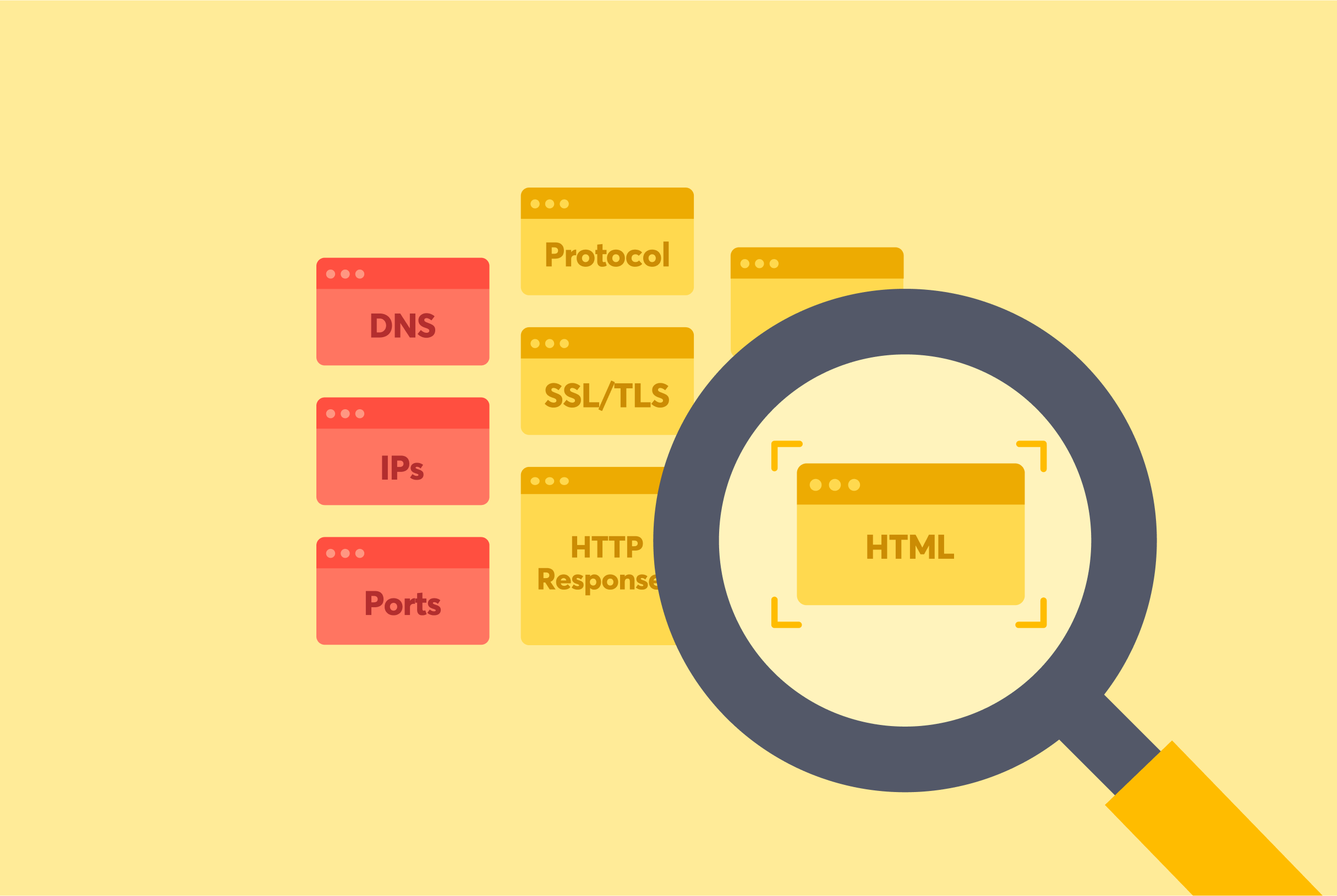
A practitioner’s guide to classifying every asset in your attack surface
Table of Contents TLDR: This article details methods and tools (from DNS records and IP addresses to HTTP analysis and HTML content) that practitioners can…