Top 3 Most Dangerous Lines of Code

Source link
Related Articles
All Mix →Decoding the Characteristics of Modern Pentesting: Effectiveness
Table of Contents Pentesting Options The Problem With Pentest Effectiveness Measuring Pentest Effectiveness Security Testing Effectiveness Evaluation Matrix The Power of PTaaS With HackerOne Quality/Effectiveness:…
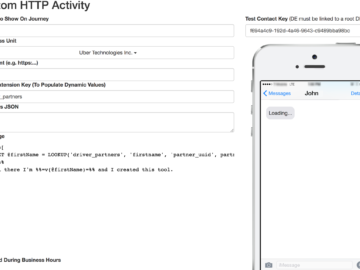
Gaining access to Uber’s user data through AMPScript evaluation
Modern development and infrastructure management practices are fast paced and constantly evolving. In the race to innovate and expand, new assets are being deployed and…
Introducing Bambdas | Blog – PortSwigger
Table of Contents Changing the face of Burp Suite How to work with Bambdas Find requests with a specific cookie value Find JSON responses with…
OWASP TOP 10: Insufficient Logging and Monitoring
Table of Contents Description Prevalence Potential impact Well-known events How to discover Insufficient Logging and Monitoring How Detectify can help Remediation Insufficient Logging and Monitoring…
Teachers and Sex: Yes, There IS A Double Standard
I’m not sure how many agree, but all things being equal I think a male teacher having sex with an underage female student is far…
When You Use One Wrong Javascript Module
When You Use One Wrong Javascript Module Source link