A highly coordinated social engineering campaign is actively targeting top open-source developers in the Node.js and npm ecosystem.
Following the recent compromise of the popular package Axios, which sees over 100 million weekly downloads, several high-impact software maintainers have reported similar attacks.
Security researchers believe this is a strategic shift by advanced threat actors aiming to secretly poison the global software supply chain.
The attackers are hunting developers who maintain foundational JavaScript tools. Targeted individuals include the creators and maintainers of widely used packages like WebTorrent, Lodash, Fastify, and dotenv. Together, these essential tools are downloaded billions of times every single month by companies worldwide.
Socket engineers, including CEO Feross Aboukhadijeh, and Node.js Technical Steering Committee Chair Matteo Collina, confirmed they were recently targeted. Collina noted the attackers posed as a legitimate company doing outreach.
Aboukhadijeh stated that these highly sophisticated attacks against individual maintainers are becoming the new normal and are accelerating rapidly across the ecosystem.
A Patient and Deceptive Playbook
Unlike standard, easy-to-spot phishing emails, this operation takes weeks to execute. Security researcher Tay links these attacks to a North Korean threat group known as UNC1069.
According to her analysis, the hackers are extremely patient and deliberate in their approach to open-source developers.
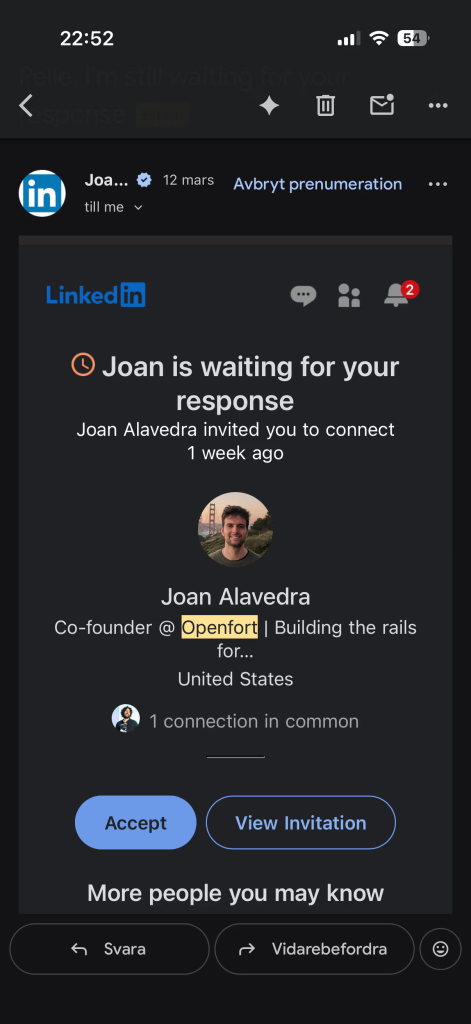
They reach out on professional platforms like LinkedIn or Slack, using fake personas from spoofed companies like “Openfort.” Developers like Pelle Wessman and Jean Burellier reported being invited to private Slack channels and pushed to join podcast interviews.
The attackers build trust over time, scheduling and even rescheduling calls to appear entirely normal and disarming.
The trap is finally set during the scheduled video call. Hackers send a link to a fake meeting platform built to look exactly like Microsoft Teams or Streamyard.
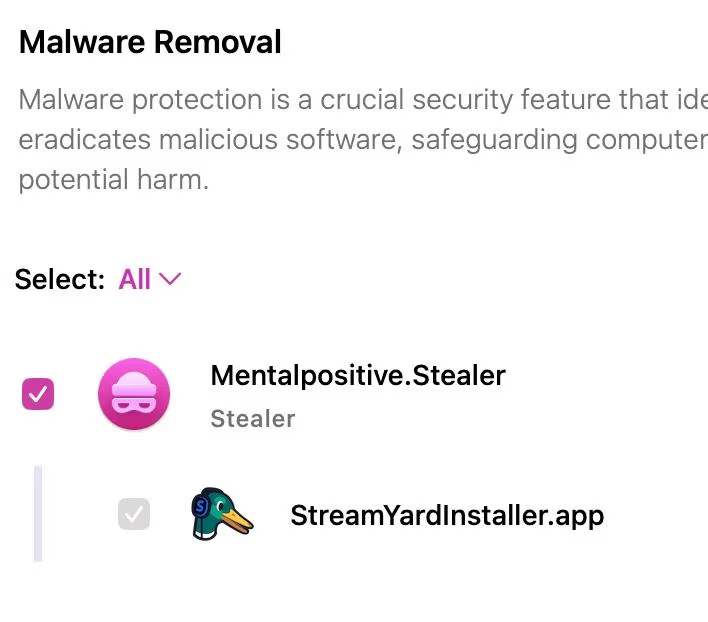
When the victim joins, the site fakes an audio failure. To “fix” the problem, the site urges the developer to download an application or run a simple command in their terminal. This action triggers the actual attack.
Bypassing Modern Security
If the developer falls for the trick, the download instantly installs a hidden Remote Access Trojan (RAT). This dangerous malware silently collects sensitive data from the victim’s computer.
It steals browser cookies, cloud credentials, password keychains, and active developer tokens, then contacts the hackers every sixty seconds for new instructions.
Because the malware steals active session data, standard two-factor authentication provides no real defense. The attackers bypass login screens completely.
This gives them immediate, full control to publish code directly to the npm registry. Even advanced publishing hygiene cannot stop a compromised machine.
Historically, this specific hacking group targeted cryptocurrency founders to steal digital money. Now, they have pivoted to open-source software.
Instead of hacking targets one by one, compromising a single popular npm package allows them to reach millions of users at once through automated updates.
Security experts are urging the open-source community to stay alert and support one another without victim-blaming.
The attacks are highly convincing, and anyone could be tricked on a busy day. As these advanced threats grow, the safety of modern applications depends heavily on protecting the developers who build our foundational code.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.







