Trojanized installers for the TOR anonymity browser are being used to target users in Russia and Eastern Europe with clipper malware designed to siphon cryptocurrencies since September 2022.
“Clipboard injectors […] can be silent for years, show no network activity or any other signs of presence until the disastrous day when they replace a crypto wallet address,” Vitaly Kamluk, director of global research and analysis team (GReAT) for APAC at Kaspersky, said.
Another notable aspect of clipper malware is that its nefarious functions are not triggered unless the clipboard data meet specific criteria, making it more evasive.
It’s not immediately clear how the installers are distributed, but evidence points to the use of torrent downloads or some unknown third-party source since the Tor Project’s website has been subjected to blockades in Russia in recent years.
Regardless of the method used, the installer launches the legitimate executable, while also simultaneously launching the clipper payload that’s designed to monitor the clipboard content.
“If the clipboard contains text, it scans the contents with a set of embedded regular expressions,” Kamluk noted. “Should it find a match, it is replaced with one randomly chosen address from a hardcoded list.”
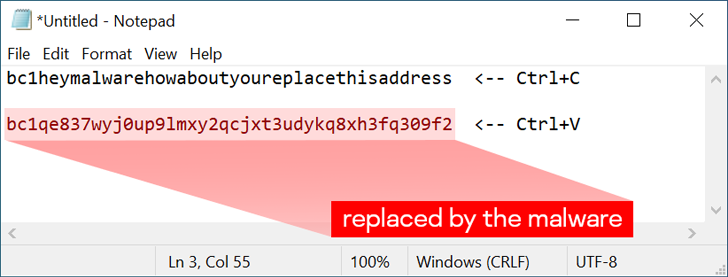
Each sample is packed with thousands of possible replacement addresses that’s selected at random. It also comes with the ability to disable the malware by means of a special hotkey combination (Ctrl+Alt+F10), an option likely added during the testing phase.
The Russian cybersecurity firm said it recorded roughly 16,000 detections, of which a majority are registered in Russia and Ukraine, followed by the U.S., Germany, Uzbekistan, Belarus, China, the Netherlands, the U.K., and France. In all, the threat has been spotted in 52 countries worldwide.
Discover the Hidden Dangers of Third-Party SaaS Apps
Are you aware of the risks associated with third-party app access to your company’s SaaS apps? Join our webinar to learn about the types of permissions being granted and how to minimize risk.
RESERVE YOUR SEAT
The scheme is estimated to have netted the operators almost $400,00 in illicit profits through the theft of Bitcoin, Litecoin, Ether, and Dogecoin. The amount of Monero assets plundered is not known owing to the privacy features built into the service.
It’s suspected that the campaign could be larger in scope due to the possibility that the threat actors could be leveraging other software installers and hitherto unseen delivery methods to target unwary users.
To secure against such threats, it’s always recommended to download software only from reliable and trusted sources.