U.S. CISA adds a flaw in Apache ActiveMQ to its Known Exploited Vulnerabilities catalog

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds a flaw in Apache ActiveMQ to its Known Exploited Vulnerabilities catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added a flaw in Apache ActiveMQ, tracked as CVE-2026-34197 (CVSS score of 8.8), to its Known Exploited Vulnerabilities (KEV) catalog.
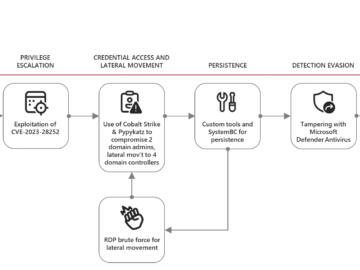
CVE-2026-34197 is a critical flaw in Apache ActiveMQ caused by improper input validation and unsafe code execution. It affects the Jolokia JMX-HTTP bridge exposed via the web console, which allows execution of certain management operations.
An authenticated attacker can send crafted requests with a malicious discovery URI that forces the broker to load a remote Spring XML configuration. Because Spring initializes beans before validation, attackers can execute arbitrary code, for example via Runtime.exec(). This results in remote code execution on the broker’s JVM.
“Apache ActiveMQ Classic exposes the Jolokia JMX-HTTP bridge at /api/jolokia/ on the web console. The default Jolokia access policy permits exec operations on all ActiveMQ MBeans (org.apache.activemq:*), including BrokerService.addNetworkConnector(String) and BrokerService.addConnector(String).” reads the advisory. “An authenticated attacker can invoke these operations with a crafted discovery URI that triggers the VM transport’s brokerConfig parameter to load a remote Spring XML application context using ResourceXmlApplicationContext. Because Spring’s ResourceXmlApplicationContext instantiates all singleton beans before the BrokerService validates the configuration, arbitrary code execution occurs on the broker’s JVM through bean factory methods such as Runtime.exec().”
The issue affects versions before 5.19.4 and 6.2.3, and users are strongly advised to upgrade.
According to Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities, FCEB agencies have to address the identified vulnerabilities by the due date to protect their networks against attacks exploiting the flaws in the catalog.
Experts also recommend that private organizations review the Catalog and address the vulnerabilities in their infrastructure.
CISA orders federal agencies to fix the vulnerability by April 30, 2026.
Pierluigi Paganini
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, US CISA Known Exploited Vulnerabilities catalog)