UAT-10362 linked to LucidRook attacks targeting Taiwan-based institutions

LucidRook is Lua malware used in phishing attacks on NGOs and universities in Taiwan, linked to UAT-10362, spread via password-protected emails.
LucidRook is a new Lua-based malware used in targeted phishing attacks against NGOs and universities in Taiwan. Cisco Talos links it to a skilled group tracked as UAT-10362. In Oct 2025, attackers used password-protected email attachments to spread the malware in spear-phishing campaigns.
“Cisco Talos observed a spear-phishing attack delivering LucidRook, a newly identified stager that targeted a Taiwanese NGO in October 2025. The metadata in the email suggests that it was delivered via authorized mail infrastructure, which implies potential misuse of legitimate sending capabilities.” reads the report published by Cisco Talos. “The email contained a shortened URL that leads to the download of a password protected and encrypted RAR archive. The decryption password was included in the email body. Based on this email and the collected samples, Talos observed two distinct infection chains originating from the delivered archives.”
The phishing emails came from likely legitimate infrastructure and included shortened links to password-protected RAR archives, with passwords inside the message.
The archives contained fake government or security-related decoy documents to distract victims.

The researchers observed two infection chains: one LNK-based and one EXE-based.
The LNK infection chain starts when a shortcut file from a phishing archive is opened, triggering the LucidPawn dropper hidden in nested folders. It uses LOLBAS techniques and PowerShell to run code through trusted Windows tools, reducing detection. LucidPawn decrypts payloads, including a legitimate DISM executable disguised as a trusted app and the LucidRook stager. It abuses DLL sideloading to load malicious code via the signed DISM binary. The malware also opens decoy documents to distract the user. Persistence is achieved by placing a malicious LNK in the Startup folder, ensuring execution at reboot.

The second infection chain uses a standalone EXE dropper written in .NET, distributed inside password-protected archives disguised as legitimate security software. When executed, it decodes embedded Base64 payloads and drops multiple files, including a legitimate DISM executable, the LucidRook stager, and a Startup LNK for persistence. The DISM binary is abused for sideloading the malware, while the dropper impersonates trusted security tools and shows a fake completion message to mislead the victim.

Both chains aim to deliver LucidRook and maintain stealth on targeted Taiwanese systems.
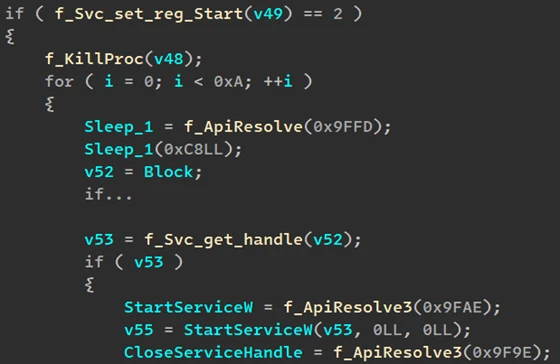
“LucidRook is a sophisticated 64-bit Windows DLL stager consisting of a Lua interpreter, embedded Rust-compiled libraries, and Lua bytecode payload. The DLL embeds a Lua 5.4.8 interpreter and retrieves a staged payload (in our sample named archive1.zip) from its C2 over FTP.” continue the report. “After unpacking and validating the downloaded stage, the implant loads and executes the resulting Lua bytecode on the compromised host.”
LucidRook is a complex malware that embeds a Lua 5.4.8 interpreter inside a large Rust-based DLL, turning it into a flexible execution platform. The malicious code downloads encrypted Lua bytecode from its command and control server, verifies it, and runs it locally, allowing operators to quickly change behavior per target. The DLL is hard to analyze due to thousands of functions and stripped components. On execution, it first collects system data like usernames, processes, and installed software, then encrypts and exfiltrates it. It uses RSA and password-protected ZIP files for protection. Communication happens over FTP using stolen or exposed credentials, often abusing public servers from companies with open upload services. The malware also hides strings using multi-stage XOR and address calculation tricks. Payloads are protected with different passwords and keys per campaign for modular deployment now
Talos also detailed LucidPawn, a dropper linked to LucidRook, sharing Rust code, obfuscation, and COM DLL masquerading. Upon execution, it queries a DNS OAST service (dnslog[.]ink) to confirm infection without attacker infrastructure. It uses geo-targeting, checking Windows UI language and only runs on Traditional Chinese systems (Taiwan/HK), avoiding sandboxes. The researchers also spotted a variant that only drops payloads and installs LucidKnight. LucidKnight is a recon tool that gathers system data, encrypts it, and exfiltrates email Gmail SMTP sending ZIP attachments disguised as ‘Sports Information Platform’. This shows a modular toolkit using different components per mission.
Talos has not yet recovered a decryptable Lua bytecode payload used by LucidRook, but is publishing its findings to enable early detection. They hope sharing this information will help the security community identify additional indicators, improve clustering of related activity, and support future attribution efforts.
“Based on the tactics, techniques, and procedures (TTPs) and the level of engineering investment observed across these infection chains, we assess with medium confidence that this activity reflects a targeted intrusion rather than broad, opportunistic malware distribution.” concludes the report. “Delivery via spearphishing, combined with LucidRook’s sophisticated design, suggests a sophisticated threat actor prioritizing flexibility, stealth, and victim-specific tasking.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, Taiwan)