UMBC Cyberdawgs CTF: The Hacker One

Source link
Related Articles
All Mix →Mac vs. PC Security In One Sentence
If you follow Information Security at all or have been part of a PC vs. Mac discussion at any level, you’ve probably come across the…
Why Apple Keeps Winning – Daniel Miessler
Table of Contents Lessons from other industries Vision and ecosystem matter too Notes Apple’s competitors haven’t solved the trinity of quality, design, and ecosystem Created/Updated:…
We Have It Backwards: Liberal Arts Should Guide Science and Technology
The term liberal arts denotes a curriculum that imparts general knowledge and develops the student’s rational thought and intellectual capabilities, unlike the professional, vocational, technical…
Detectify wins 2022 Fortress Cyber Security Award
The Business Intelligence Group announced on June 7 that Surface Monitoring by Detectify has won the 2022 Fortress Cyber Security Award in the Application Security…
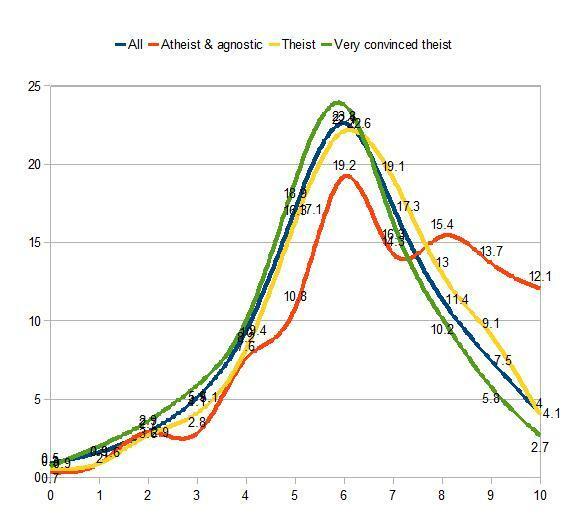
10 Interesting Data Points on IQ and Demographics
Gene Expression recently put up a brilliant post showing data on the GSS‘s WORDSUM scores correlated to various demographic data points, such as educational attainment,…
Q: How to write a BUG BOUNTY report that actually gets paid?
Q: How to write a BUG BOUNTY report that actually gets paid? Source link