North Korean threat actor UNC1069 has escalated attacks against the cryptocurrency and decentralized finance (DeFi) sector using sophisticated AI-powered social engineering tactics and seven distinct malware families, according to a recent Mandiant investigation.
The financially motivated group, active since 2018, deployed an unprecedented arsenal of tools, including newly discovered malware dubbed SILENCELIFT, DEEPBREATH, and CHROMEPUSH, during a targeted intrusion against a FinTech entity.
The attack began with a compromised Telegram account belonging to a cryptocurrency company executive.
UNC1069 built rapport with the victim before sending a Calendly scheduling link that directed to a spoofed Zoom meeting hosted on attacker-controlled infrastructure at zoom[.]uswe05[.]us.
During the fake video call, the victim reportedly encountered an AI-generated deepfake impersonating a CEO from another cryptocurrency company, though Mandiant could not independently verify the AI’s use.
The social engineering scheme employed a ClickFix attack technique, where threat actors trick users into running malicious commands under the guise of troubleshooting technical issues.
The fake meeting presented the victim with apparent audio problems, prompting them to execute “troubleshooting” commands that actually initiated the infection chain.
Advanced Malware Arsenal
Mandiant discovered seven unique malware families deployed during the intrusion, with SUGARLOADER being the only previously identified tool.
The new malware included DEEPBREATH, a Swift-based data miner that manipulates macOS Transparency, Consent, and Control databases to steal credentials from Keychain, browser data from Chrome, Brave, and Edge, and user information from Telegram and Apple Notes.
CHROMEPUSH, a C++-written data miner, installed itself as a browser extension masquerading as a Google Docs offline editor to capture keystrokes, username and password inputs, and browser cookies.
The backdoor SILENCELIFT beaconed host information to command-and-control servers while maintaining the capability to interrupt Telegram communications when executed with root privileges.
Evolving Tactics and Targeting
ClickFix attacks have become increasingly prevalent across the threat landscape, with attackers using fake error messages and CAPTCHA verification prompts to manipulate users into executing malicious code themselves.
Notably, while UNC1069 has had a smaller impact on cryptocurrency heists compared to other groups like UNC4899 in 2025.
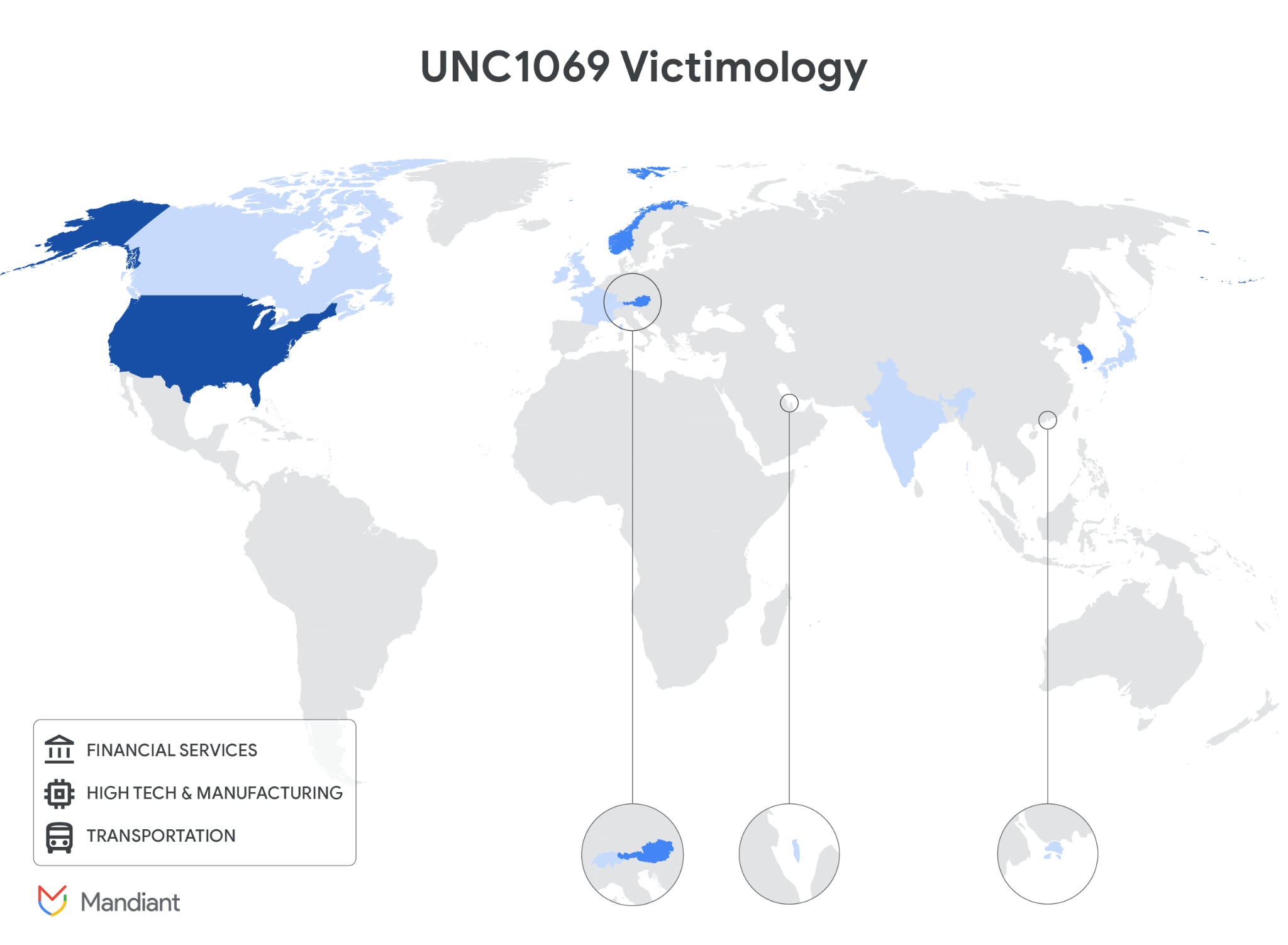
UNC1069 has transitioned from traditional spear-phishing to sophisticated Web3 industry targeting, focusing on centralized exchanges, software developers at financial institutions, and venture capital firms.
The group leverages AI tools like Gemini for developing malware, conducting operational research, and reconnaissance.
The massive volume of tooling deployed on a single host demonstrates UNC1069’s determined effort to harvest credentials, browser data, and session tokens for cryptocurrency theft and future social engineering campaigns using stolen victim identities.
Indicators of Compromise
| Indicator | Description |
|---|---|
| mylingocoin.com | Hosted the payload that was retrieved and executed to commence the initial infection |
| zoom.uswe05.us | Hosted the fake Zoom meeting |
| breakdream.com | SUGARLOADER C&C (Command & Control) |
| dreamdie.com | SUGARLOADER C&C (Command & Control) |
| support-zoom.us | SILENCELIFT C&C (Command & Control) |
| supportzm.com | HYPERCALL C&C (Command & Control) |
| zmsupport.com | HYPERCALL C&C (Command & Control) |
| cmailer.pro | CHROMEPUSH upload server |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.