A data theft campaign by a relatively new hacking group, UNC6692, has been discovered, in which hackers use social engineering and a custom modular toolset called the SNOW ecosystem to penetrate corporate networks.
This research from Mandiant, part of the Google Threat Intelligence Group (GTIG), indicates that this campaign began in late December 2025.
The Microsoft Teams Trap
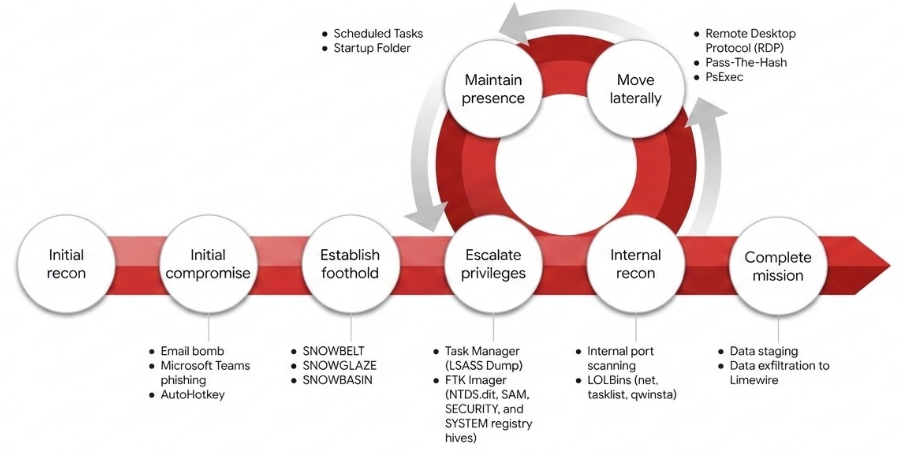
As per Google’s blog post, the attack chain starts with email bombing, where hackers flood a target’s inbox with thousands of messages. While the victim is distracted by the chaos, the hackers send a message on Microsoft Teams pretending to be IT helpdesk staff. They offer a link to a patch that supposedly stops the spam.
This link is a trap. It leads to a credential-stealing page designed to look like a Mailbox Repair Utility. To ensure they’ve gotten the right password, the page uses a psychological trick where it rejects the first two login attempts. Eventually, when the victim starts interacting with the site, they unknowingly download an AutoHotkey binary and script that formally initiates the infection chain.
The Snow Ecosystem
Research reveals that UNC6692 uses a modular suite of malicious tools to perform this attack without detection. The first part is SNOWBELT, a malicious browser extension that acts as a primary foothold and relays commands from the hackers. To keep communication open, they use SNOWGLAZE, a Python-based tunneler that sets up a hidden connection to the attackers’ servers.
The last tool is the SNOWBASIN backdoor. It lets attackers perform remote command execution (RCE) through PowerShell or cmd.exe to run system commands, take device screenshots, and prepare stolen files. Next, they start an internal reconnaissance mission to find other connected computers/servers.
Using Python scripts, attackers scan the network for ports 135, 445, and 3389, used mainly for sharing files/remote access, which leads directly to the next phase, where they target the main servers that manage everyone’s passwords.
Stealing the Data
Reportedly, UNC6692 targeted the LSASS (Local Security Authority Subsystem Service) process memory on backup servers to steal more login details. As researchers explained, the LSASS “process lsass.exe enforces security policy and contains usernames, passwords, and hashes for accounts that have accessed the system.”
Using the Pass-The-Hash technique (where authentication is done via NTLM instead of the account password), they performed lateral movement and reached the Domain Controllers (servers that manage a company’s user identities), which helped them gain control.
Using another tool called FTK Imager, they could mount local drives and extract the Active Directory database, called NTDS.dit, along with registry hives like SAM, SYSTEM, and SECURITY. Finally, they used LimeWire to exfiltrate this data.
Researchers concluded that this campaign highlights “an interesting evolution in tactics” by abusing legitimate cloud services to blend in with normal office traffic, and early detection is our only defence.
“As threat actors continue to professionalize these modular, cross-platform methodologies, the ability to correlate disparate events across the browser, local Python environments, and cloud egress points will be critical for early detection.”
Photo by Tracy Adams on Unsplash