Velocity Exploit on Paper?

Source link
Related Articles
All Mix →How I See AI Affecting Education
By default AI will magnify gaps between good and bad students June 1, 2025 I’ve got a one-liner for what AI will do to education.…
Getting Back Into Table Tennis
After being dormant for many years in my favorite participation sport, I found my new Table Tennis club on the peninsula. It’s called the Peninsula…
Announcing the Largest DoD Bug Bounty Challenge Ever: Hack the Air Force
The Air Force is asking hackers to take their best shot following the success of Hack the Pentagon and Hack the Army bug bounty challenges.…
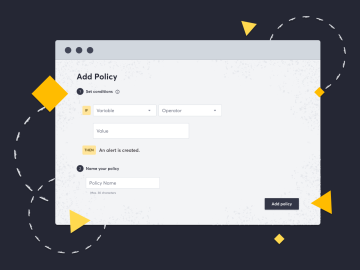
Assign Severity Ratings on Custom Policies
Table of Contents Why would I use severity ratings with Attack Surface Custom Policies? Setting rules on fingerprinted technologies now possible “As part of our…
How I created custom desktop notifications using terminal and cron
Table of Contents Periodically check your dhcp address Periodically display the time and date System log activity How you can use tools your Linux system…
Is it becoming cool to not capitalize story titles?
Table of Contents CNN New York Times Salon Huffington Post The New Yorker The Economist TechCrunch Wall Street Journal NPR Summary While reading certain publications…