A highly evasive multi-stage malware campaign deploying the Vidar Infostealer. First discovered in late 2018 and built on the Arkei stealer source code, Vidar is notorious for aggressively harvesting user credentials, browser session cookies, cryptocurrency wallets, and detailed system data.
According to an analysis by researcher Mahadev Joshi, this recent campaign utilizes AutoIt scripting and legitimate platforms to mask its activities and silently communicate with command-and-control (C2) servers.
The infection sequence initiates when a victim executes MicrosoftToolkit.exe, a commonly abused software activation tool. Instead of exploiting system vulnerabilities, the attackers rely on users willingly downloading and running this utility. Once launched, the executable spawns a command shell to begin the staging phase.
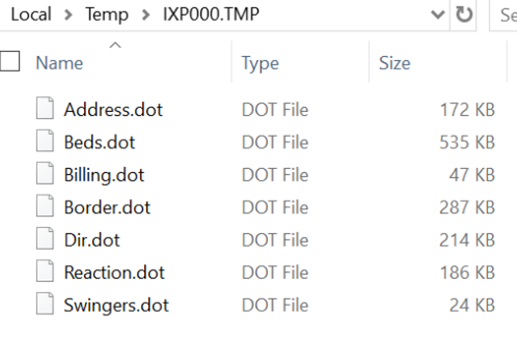
The malware then renames a disguised data file, originally named swingers.dot, into a batch script. This file extension masquerading allows the malicious script to bypass basic security controls and execute embedded commands within the user space without raising immediate alarms.
Vidar Infostealer Campaign Steals Passwords
Before dropping its final payload, the malware actively maps the local environment to avoid detection. It invokes built-in Windows commands like tasklist.exe and findstr.exe to enumerate running processes and attempt to disrupt active security tooling, as reported by LevelBlue.
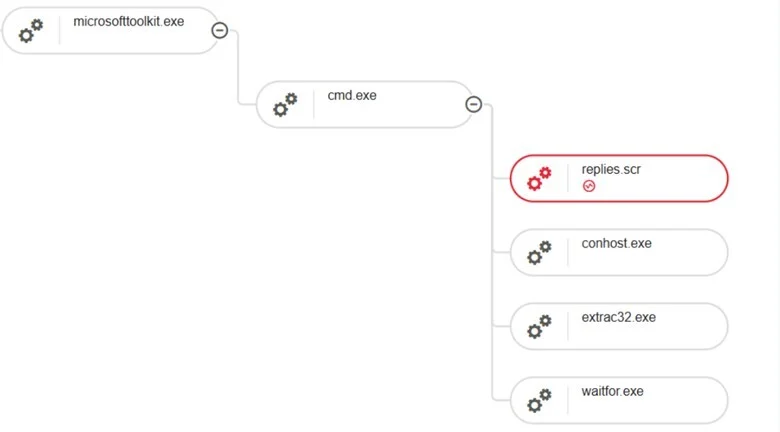
Following this reconnaissance, the malware uses extract32.exe to extract secondary payload components from multiple .dot files. The core of this staging phase involves an AutoIt-compiled binary named Replies.scr.
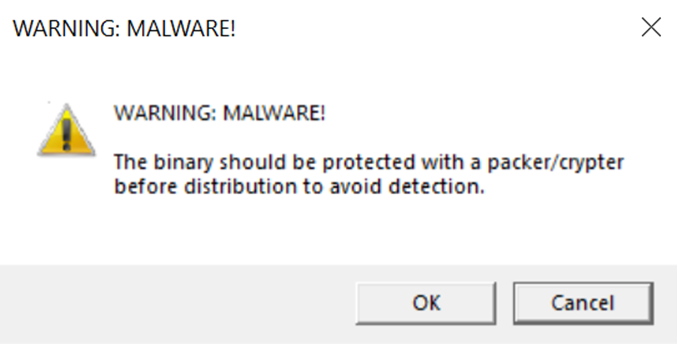
AutoIt is a legitimate Windows automation language, making it a perfect disguise for attackers to run malicious logic without triggering antivirus signatures. This executable functions as a builder-style loader, reading an encrypted external payload file into memory for decryption and execution.
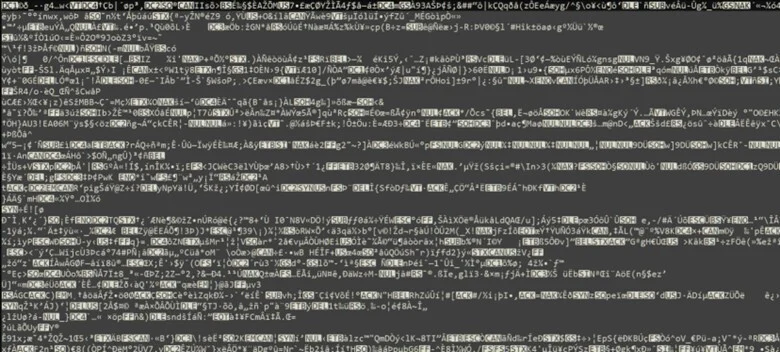
The payload actively resists security analysis during runtime. It leverages ZwQueryInformationProcess to check for process debug flags, effectively pausing or altering the process’s behavior if it detects a researcher’s debugger. It also checks for instrumentation callbacks typically used by Endpoint Detection and Response (EDR) solutions.
Once the Vidar stealer is successfully loaded into memory, it establishes outbound communication using WinINet-based application programming interfaces (APIs). The malware retrieves its configuration data and staging instructions from public web content before beginning data exfiltration.
The C2 communication strategy is particularly stealthy because it targets legitimate services. Researchers observed the malware constructing HTTP GET requests to specific Telegram and Steam Community profile URLs.
By using these trusted platforms as dead-drop resolvers, the malware blends its beaconing activity with normal web traffic, making network-level detection incredibly difficult. It also resolves dynamic domain names via public Google DNS before establishing broader outbound connections.
After successfully exfiltrating data, the initial MicrosoftToolkit.exe process runs an extensive cleanup routine to erase its tracks. The malware resets the attributes of all dropped .dot payload files and systematically deletes them from the disk.

It then frees all associated memory structures, iterates through the staging directory to remove remaining execution artifacts, and terminates its own process using RtlExitUserProcess.
This self-deletion capability significantly reduces forensic artifacts on the compromised endpoint, greatly complicating retrospective incident response efforts and allowing the threat actors to remain hidden long after the data theft is complete.
IOCs
| IOC | IOC type | Description |
| fc27479ff929d846e7c5c5d147479c81e483a2ec911bd1501a53aa646a29620d | SHA-256 | MicrosoftToolkit.exe |
| d4fe9f48178cdf375a3be30d17f1dc016b5861dff8683f0bb35a0ba8d44f892f | SHA-256 | swingers.dot.bat |
| 978ad86c90d85b74947bb627ec24f8bcd26812b500e82f5af202160506ac29c6 | SHA-256 | Beds.dot |
| 881619a47b62b52305d92640cc4d4845a279c23a5a749413785fc8fcb0fdf7fb | SHA-256 | replies.scr |
| 968ecf51c442ec0ff91f91689ac524e7e8e9eab0c1a2a65cf13e54cf95194efe | SHA-256 | D (payload file) |
| 149.154.167[.]99 | IP Address | Vidar-associated C2 IP |
| telegram[.]me | Domain Name | C2 domain |
| gz[.]technicalprorj[.]xyz | Domain Name | Vidar-associated C2 domain |
| Tactic | Techniques / Sub-Techniques | Summary |
| TA0001 – Initial Access | T1204.002 – User Execution: Malicious File | User downloaded and executed microsofttoolkit.exe (hacktool), serving as the initial entry point into the system |
| TA0002 – Execution | T1204.002 – User Execution: Malicious File | User executed microsofttoolkit.exe, initiating the infection under the assumption of legitimate software activation |
| TA0002 – Execution | T1059.003 – Command and Scripting Interpreter: Windows Command Shell | Batch/script-based execution used to stage further activity |
| TA0002 – Execution | T1027 – Obfuscated/Compressed Files | Payload staged via compressed or embedded format using extract32.exe |
| TA0002 – Execution | T1140 – Deobfuscate/Decode Files or Information | Extraction process used to unpack the next-stage payload |
| TA0002 – Execution | T1059 – Command and Scripting Interpreter | AutoIt-based loader executed via script-like behavior |
| TA0002 – Execution | T1218 – Signed Binary Proxy Execution | .scr (AutoIt compiled binary) used as a loader to execute malicious logic |
| TA0005 – Defense Evasion | T1036 – Masquerading | A .dot file was renamed to .bat to bypass basic file-type restrictions |
| TA0005 – Defense Evasion | T1562.001 – Disable or Modify Security Tools | taskkill.exe used to terminate security-related processes |
| TA0005 – Defense Evasion | T1059.003 – Command Shell | findstr.exe leveraged for filtering and identifying security processes |
| TA0005 – Defense Evasion | T1070.004 – Indicator Removal on Host: File Deletion | Malware deleted dropped files to remove evidence |
| TA0005 – Defense Evasion | T1489 – Service Stop | Processes terminated to reduce forensic artifacts and evade detection |
| TA0011 – Command and Control | T1071.001 – Application Layer Protocol: Web Protocols | Malware communicated with C2 over HTTP/HTTPS |
| TA0011 – Command and Control | T1573 – Encrypted Channel | Encrypted communication used to evade detection |
| TA0010 – Exfiltration | T1041 – Exfiltration Over C2 Channel | Stolen data (credentials, browser data) exfiltrated via C2 channel |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.