Hackers are abusing a stealthy Python backdoor called VIPERTUNNEL, hiding it behind a fake DLL file and a multi‑stage obfuscated loader to quietly tunnel traffic out of victim networks.
A review of persistence mechanisms revealed a sitecustomize.py file in C:ProgramDatacp49sLib. This special Python module auto‑loads at interpreter startup and can silently run code without command‑line input.
This script used ctypes to call the Python C API (Py_GetArgcArgv) and check whether Python was launched with only one argument (the executable itself).
During an incident involving the DragonForce ransomware group, analysts spotted a suspicious scheduled task named 523135538 executing C:ProgramDatacp49spythonw.exe with no arguments, an uncommon pattern for legitimate Python use on Windows.
If so, it built a path to b5yogiiy3c.dll in C:ProgramDatacp49s and executed it with runpy run_path, treating the “DLL” as a Python script rather than a real Windows library.
Fake DLL and layered obfuscation
The file b5yogiiy3c.dll turned out to be a heavily obfuscated Python loader mislabelled as a DLL, not a native PE library.
It imported several embedded modules from the same directory and relied on cryptographic primitives such as BLAKE3, SHA‑256, AES, ChaCha20, base64, and zlib, strongly indicating an encrypted payload and staged decryption chain.
To frustrate static analysis, the script replaced meaningful function and API names with random variable identifiers and pre‑bound operations such as zlib.decompress and base64.b85decode for later use.
Base85 encoding, which is denser than standard Base64, helps the malware evade simplistic pattern‑based detections that only look for familiar Base64 markers.
Investigators recovered two core decoding functions: one to reverse Base85‑encoded blobs and another to convert integer arrays back into strings, forming the main translation layer for the hidden code.
Tracing control flow led to a large high‑entropy blob that was decrypted and compiled at runtime using compile(…, ‘
The decryption routine itself used control‑flow flattening via a while True loop and a state variable, making the logic non‑linear and harder to follow.
Three distinct obfuscation stages were identified: each stage decoded a payload, compiled it, and executed it, before handing off to the next, with all stages staying in memory.
A public unpacker for a similar framework exists from eSentire’s ShadowCoil research, but the variant used here diverged enough that the public tool could not fully decode this chain.
The final stage implements a SOCKS5 proxy that creates an outbound tunnel to a hard‑coded command‑and‑control server over port 443, blending into normal HTTPS traffic.
While a default C2 and credentials are embedded, operators can also pass alternate C2 details via command‑line parameters when launching the backdoor.
VIPERTUNNEL’s architecture revolves around three main classes: Wire, Relay, and Commander.
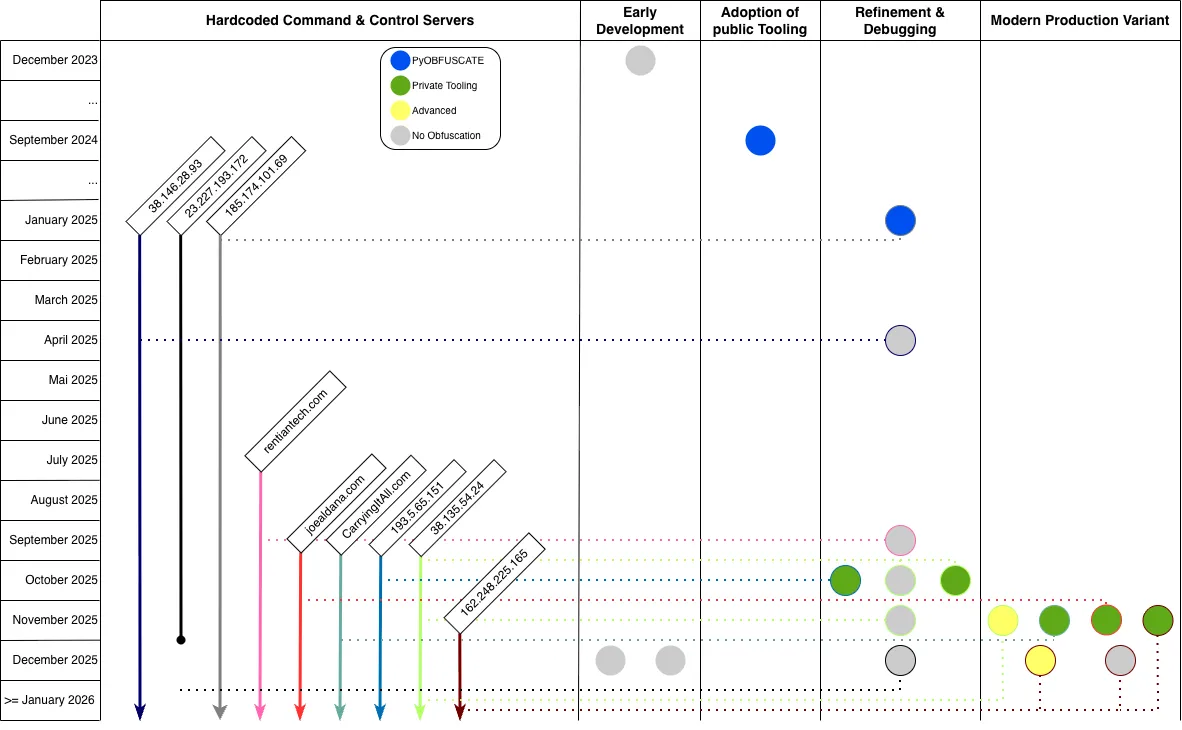
C2 communication shows active deployment periods, but VirusTotal upload timestamps and domain registration records help fill gaps.
Commander inherits from threading.Thread, manages the initial C2 handshake, and spawns Relay threads; Relay handles SOCKS5 proxy logic between the C2 and internal hosts; Wire abstracts socket operations and encapsulates tunneled data, enabling multiple concurrent tunnels for lateral movement and data exfiltration.
Attribution and links to ShadowCoil
Threat‑intel mapping links this Python backdoor to UNC2165/EvilCorp activity and the VIPERTUNNEL family previously observed as a follow‑on payload for FAKEUPDATES (SocGholish) infections, often used to maintain access and pivot networks before ransomware deployment by groups including RansomHub.
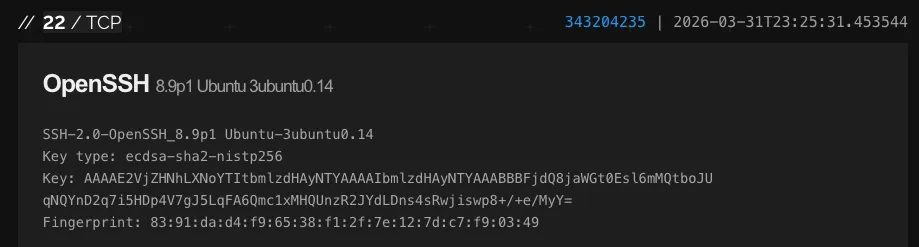
OpenSSH version is largely consistent across servers, it is not identical in all cases and therefore is not a reliable indicator.
In the DragonForce case, the timeline indicates VIPERTUNNEL access pre‑dated the ransomware deployment, but there is not yet conclusive proof that access was sold or transferred to that affiliate.
Hunting across telemetry revealed other samples using the same multi‑stage obfuscation packer to deliver ShadowCoil (aka COILCAGE/RATTLEGRAB), a Python‑based credential stealer focused on Chromium browsers and, increasingly, Firefox.
ShadowCoil variants share the layered loader design but add extra anti‑debugging checks, including a Linux‑specific TracerPid check in /proc/self/status; errors under Windows are silently ignored, suggesting a cross‑platform framework whose payloads currently focus on Windows targets.
Overall, this campaign shows a clear evolution from un‑obfuscated, typo‑ridden early VIPERTUNNEL versions in late 2023 to a mature, modular production backdoor by late 2025, with refined code, stronger obfuscation, and stealthy infrastructure tightly integrated with the Python‑based loader chain and fake DLL disguise.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.






