Visa is warning about a spike in detections for a new version of the JsOutProx malware targeting financial institutions and their customers.
In a security alert from Visa’s Payment Fraud Disruption (PDF) unit seen by BleepingComputer and sent to card issuers, processors, and acquirers, Visa says they became aware of a new phishing campaign distributing the remote access trojan on March 27, 2024.
This campaign targeted financial institutions in South and Southeast Asia, the Middle East, and Africa.
First encountered in December 2019, JsOutProx is a remote access trojan (RAT) and highly obfuscated JavaScript backdoor that allows its operators to run shell commands, download additional payloads, execute files, capture screenshots, establish persistence on the infected device, and control the keyboard and mouse.
“While PFD could not confirm the ultimate goal of the recently identified malware campaign, this eCrime group may have previously targeted financial institutions to conduct fraudulent activity,” reads the Visa alert seen by BleepingComputer.
The alert provides indicators of compromise (IoCs) related to the latest campaign and recommends several mitigation actions, including raising awareness about phishing risks, enabling EMV and secure acceptance technologies, securing remote access, and monitoring for suspicious transactions.
The phishing campaign
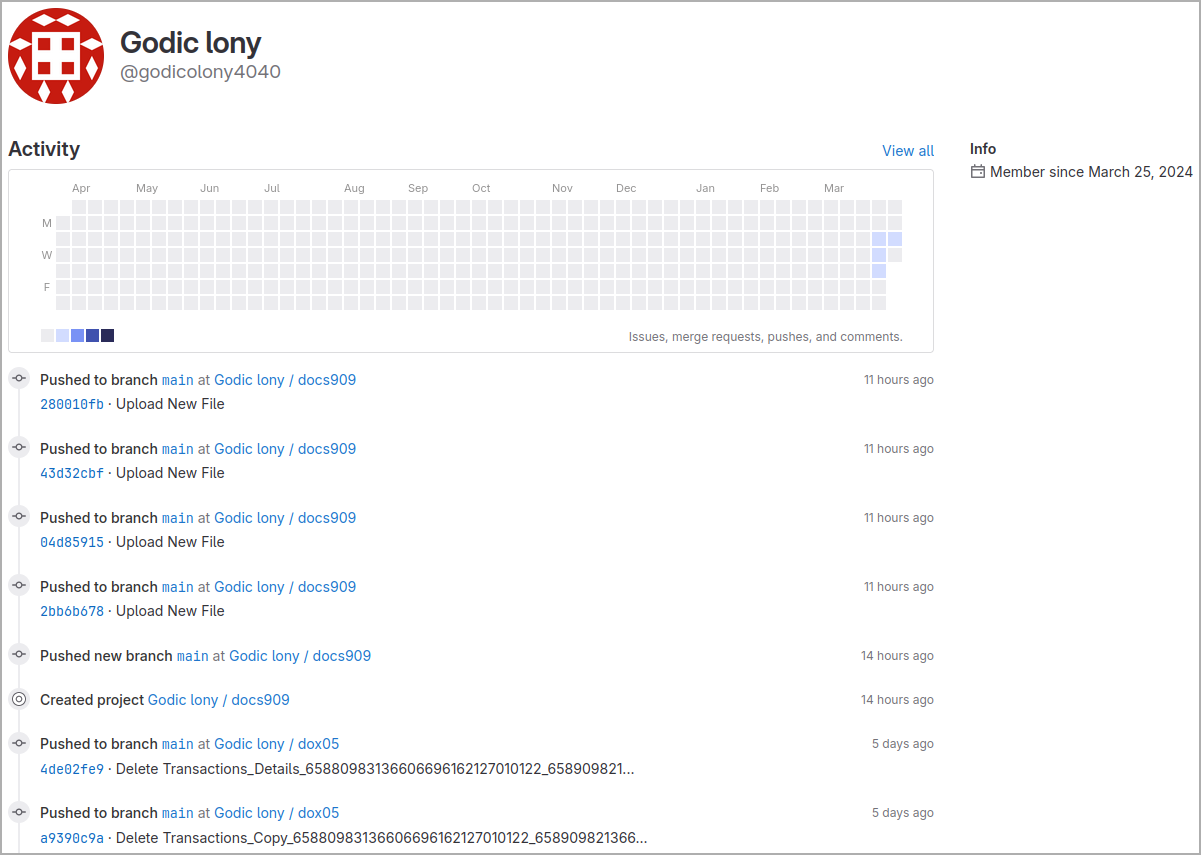
A related report by Resecurity dives deeper into the JSOutProx phishing operation details, explaining that the malware has evolved its latest version for better evasion and now uses GitLab to host its payloads.
In the observed attacks against banking customers, Resecurity saw fabricated financial notifications sent to targets via emails that impersonate legitimate institutions, presenting them with fake SWIFT or MoneyGram payment notifications.
Attached to the emails are ZIP archives containing .js files that, when executed, download the malicious JSOutProx payloads from a GitLab repository.
The first stage of the JSOutProx implant supports a range of commands that enable the attackers to perform basic functionalities such as updating it, managing its sleep time for operational discretion, executing processes, and exiting the implant when necessary.
The second stage of the implant introduces additional plugins that significantly expand the range of malicious activities the attackers can perform and include the following:
- Set the RAT’s active communication and operations, allowing it to avoid detection by staying dormant.
- Alter proxy settings for internet traffic manipulation and security measure evasion.
- Steal or change clipboard content, accessing sensitive data like passwords.
- Adjust DNS settings to redirect traffic, aiding in phishing or stealthy C2 communication.
- Extract details and contact from Outlook for potential phishing attacks or malware spread.
- Bypass UAC and modify the registry for deeper system access and maintaining persistence.
- Tweak DNS and proxy settings to control or disguise internet traffic.
- Automate malicious activities or ensure persistence by creating and modifying shortcut files.
- Recover and send data from the infected system to attackers, potentially for information theft or ransomware activities.
- Steal One-Time Passwords (OTPs) to bypass two-factor authentication protections on the target account.
Resecurity says early operations of JSOutProx were attributed to a threat actor named ‘Solar Spider,’ but there’s no concrete attribution for the latest campaign.
Based on the attacks’ sophistication, the targets’ profile, and their geography, the analysts estimate with moderate confidence that JSOutProx is operated by Chinese or China-affiliated threat actors.