Void Dokkaebi, also known as Famous Chollima, is expanding its cyber operations by turning fake job interviews into a large-scale malware distribution campaign targeting developers.
The campaign begins with attackers posing as recruiters from cryptocurrency or AI companies. Developers are invited to complete coding tests that require cloning and running seemingly legitimate repositories from platforms like GitHub or GitLab.
These repositories contain malicious Visual Studio Code (VS Code) configurations, specifically a hidden .vscode/tasks.json file. When the project is opened and the developer trusts the workspace, the task executes automatically, downloading and running malware in the background.
Recent analysis shows the group has evolved beyond traditional social engineering into a self-propagating supply chain attack that spreads through trusted development workflows and code repositories.
Worm-Like Spread Through Code
Unlike typical attacks that stop after the first compromise, Void Dokkaebi uses infected developers to spread malware further. Once a developer commits infected code to a repository, the malicious .vscode configuration travels with it.
Because this folder is often hidden and not excluded via .gitignore, other developers who clone the repository can unknowingly trigger the same infection. This creates a chain reaction, similar to a worm, where each new victim becomes a distributor.
An example: A developer infected during an interview pushes code to a shared project. A teammate later clones the repo, opens it in VS Code, and unknowingly executes the same malicious task continuing the cycle.
The attackers also use a second method involving direct code injection. After gaining access to a developer’s machine, they insert obfuscated JavaScript into commonly ignored configuration files like eslint or tailwind configs.
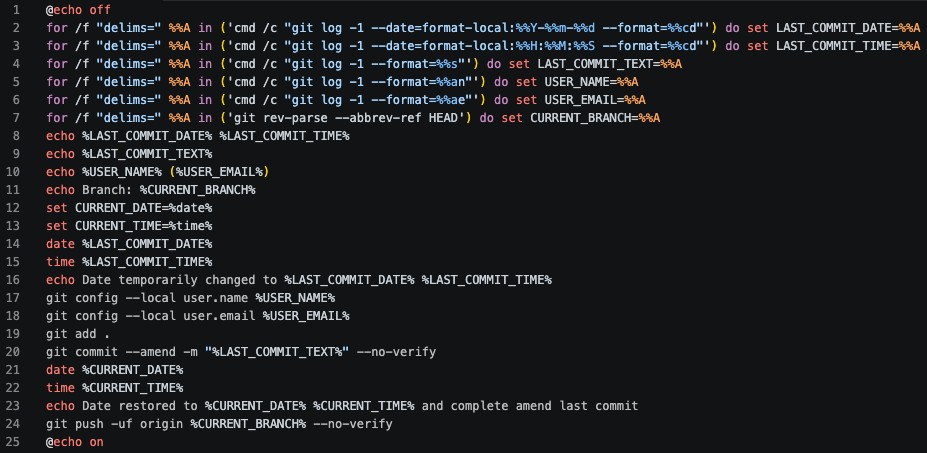
To hide this activity, they use a commit tampering tool that rewrites Git history. It preserves original timestamps, authorship, and commit messages, making malicious changes appear legitimate. Security checks are bypassed using forced commits and disabled verification.
Large-Scale Impact
The –no-verify flag is used to bypass pre-commit hooks and CI/CD security checks. After the amendment, the system clock is restored, and the rewritten commit is force-pushed to the remote branch.
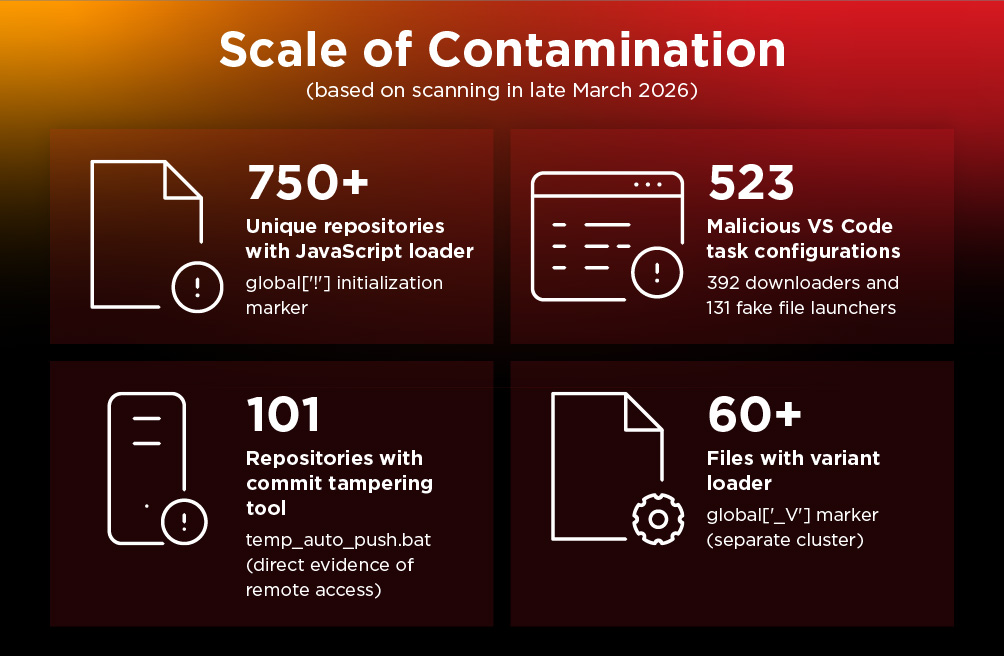
By March 2026, researchers identified:
- Over 750 infected repositories.
- More than 500 malicious VS Code task configurations.
- At least 101 repositories containing commit tampering tools.
Notably, repositories linked to organizations like DataStax and Neutralinojs were found compromised, highlighting the risk to enterprise and open-source ecosystems. In one case, thousands of downstream users were exposed after a popular project was infected.
Scan identified over 750 unique repositories containing the obfuscated JavaScript loader, identified by the global[‘!’] initialization marker.
Void Dokkaebi uses blockchain networks such as Tron, Aptos, and Binance Smart Chain to host and deliver malware payloads. This approach makes takedowns difficult because the infrastructure is decentralized and immutable.
The malware, including a variant of the DEV#POPPER remote access trojan, retrieves encrypted payloads from blockchain transactions, decrypts them, and executes them on infected systems. This allows attackers to update payloads dynamically without modifying the original code.
The attack spreads through trust in tools, workflows, and collaboration.
Security teams and developers can reduce risk by:
- Using isolated environments for coding tests.
- Adding .vscode/ to .gitignore.
- Enforcing signed commits and blocking force pushes.
- Auditing repositories for suspicious markers like global[‘!’].
- Monitoring unusual blockchain or command-and-control traffic.
Void Dokkaebi’s campaign shows how a single compromised developer can trigger widespread infection across the software ecosystem, making developer environments a critical part of modern cybersecurity defense.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.