A newly exposed malware framework, VoidLink, is reshaping how attackers manage implants across modern cloud and enterprise environments.
Cisco Talos has now linked this framework to a threat actor tracked as UAT-9921, highlighting how on-demand compilation, modular plugins, and early Windows support point toward the next generation of AI-enabled attack platforms.
UAT-9921 compromises internet-facing servers, often with pre-obtained credentials or by exploiting Java serialization flaws such as Apache Dubbo remote code execution, then deploys VoidLink as its main implant.
Cisco Talos recently identified UAT-9921 using VoidLink in active campaigns, with evidence suggesting the group has been operating since at least 2019, even before the framework existed.
Once inside a network, the actor installs VoidLink command-and-control (C2) components on compromised hosts and launches internal and external scanning from there.
To support reconnaissance, UAT-9921 deploys a SOCKS proxy on victim servers and uses tools like FSCAN to map internal networks before expanding further.
Language artifacts and code comments indicate the developers and operators are likely Chinese-speaking, and Talos assesses with medium confidence that UAT-9921 has been active for several years using other tooling before adopting VoidLink.
While the activity looks like a real intrusion campaign, researchers cannot fully rule out that some operations might be related to red-team exercises, given the framework’s built-in oversight features.
VoidLink: modular, cloud-aware, and AI-assisted
VoidLink is a cloud-native, modular framework primarily targeting Linux systems, designed to deliver long-term, stealthy access rather than quick smash-and-grab attacks.
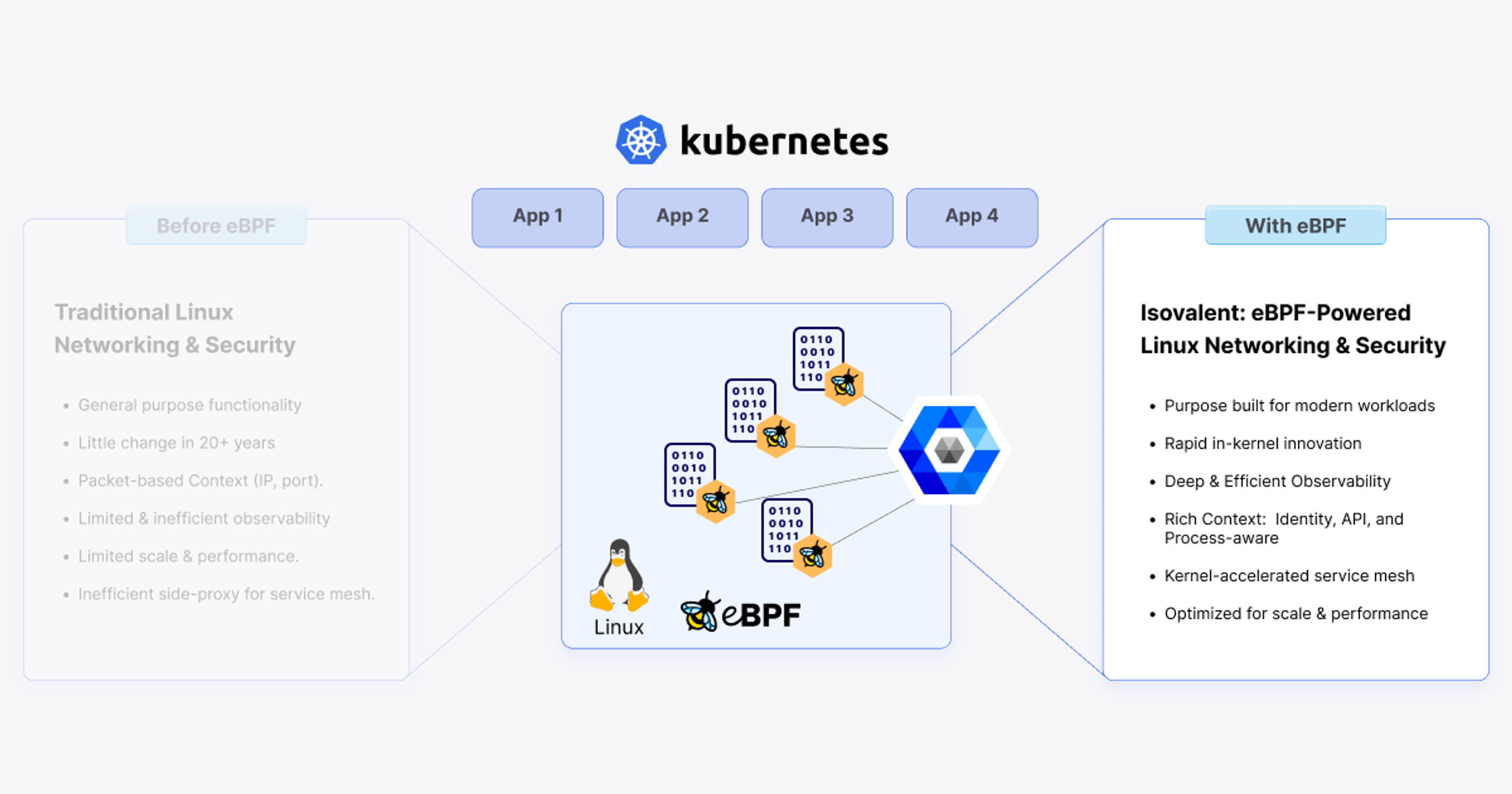
Tetragon both alerts on and blocks events directly within the kernel. Enforcement mechanisms include overriding the syscall’s return value.
The main implant is written in Zig, plugins are in C, and the backend uses Go, giving operators a flexible stack that can be quickly extended to different environments.
The framework is cloud-aware and can detect when it is running in Kubernetes or Docker, then query provider-specific metadata APIs to understand its surroundings better.
Its Linux implants include advanced capabilities such as eBPF- or loadable kernel module-based rootkits, container privilege escalation, and sandbox escape, with many plugins aimed at desktop Linux as well as servers, which is relatively uncommon in today’s threat landscape.
Development appears to have been heavily assisted by large language model–enabled integrated development environments, allowing the framework to reach a near-production-ready state in roughly two months.
Cisco Talos notes that different teams seem to be working on development and operations, with operators holding access to implant kernel module sources and tools that can talk to implants without going through the C2, indicating deep knowledge of internal protocols.
VoidLink’s innovation is its compile-on-demand model, where the C2 server builds kernel modules and plugins dynamically for each target.
This enables tailored implants optimized for specific Linux distributions and kernel versions, while reducing static signatures and avoiding the need for build tools on victim machines.
This architecture lays the groundwork for future AI-enabled attack frameworks in which implants could request new “tools” from the C2 as needed, such as a database access plugin or an exploit for an internal web service.
An agent on the C2 side could research, generate, and compile these tools on demand, allowing continuous adaptation while the operator keeps exploring the environment.
Windows indications
Unlike many offensive frameworks, VoidLink includes enterprise-style controls such as full audit logging and role-based access control with SuperAdmin, Operator, and Viewer roles.
These features support legal and corporate oversight, reinforcing the idea that such toolchains are approaching “defense contractor grade” implant management platforms.
Mesh peer-to-peer routing and dead-letter queue mechanisms allow implants to route traffic through one another, building hidden internal networks that can bypass strict egress filters.
While publicly documented samples focus on Linux, Cisco Talos reports clear that the main implant has also been compiled for Windows and can load plugins through DLL sideloading, even though no Windows samples have yet been recovered.
VoidLink’s capabilities, including EDR awareness, obfuscation, and anti-analysis features, are designed to make detection harder and shrink the time to lateral movement and data theft.
Still, vendors have begun shipping coverage: Cisco provides Snort 2 and Snort 3 signatures for VoidLink traffic and behaviors, while ClamAV detects the malware as Unix.Trojan.VoidLink-10059283.
As frameworks like VoidLink evolve, defenders should expect more campaigns where AI-accelerated development and on-demand tool generation give attackers a rapid advantage over traditional detection and response cycles.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.